The Humanity and Evolution of Cyber

We see the word “cyber” everywhere today. It’s included in all the hashtags, events names and even in hand sanitizer available for purchase at Toys ‘R Us: Cyber Clean (72% ethanol alcohol, with aloe.)
With the market booming and the buzzword exploding, many of us still don’t understand what this vague word means. We’re simply toeing the line, either reluctantly when our IT department sends out a reminder to complete our annual security training or enthusiastically to survive and spread the good word.
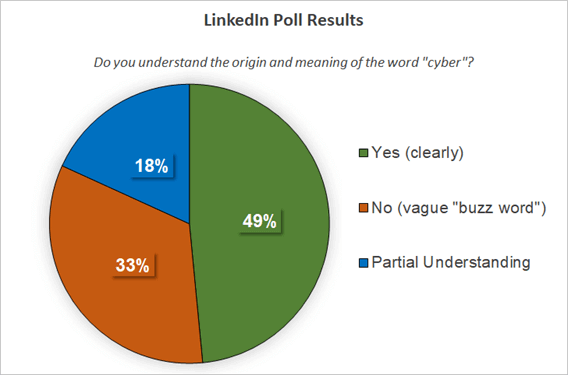
To solicit more feedback from my peers, I conducted and shared a LinkedIn Poll with my professional network in February 2021 (shown below.) Out of 33 voters, just over half of those polled had no or partial understanding of the origin and meaning of the word “cyber.“
How was the term “cyber” coined?
“Cyber” has origins to the Greek word “kubernetes.” If you work in tech or have hung around developers long enough, you may have heard of this open source container system, designed by Google, that automates application deployment.
When we study the Greek roots of the word “kubernetes,” we learn that it refers to a pilot or steersman and that it is closely related to the Greek word “kubernesis” – the gift of governance that applies to leadership.
A quick history lesson teaches us that “cybernetics” was first coined and published by Norbert Wiener in the 1940s. Wiener was involved in the fields of computer science, engineering and biology. He studied their interconnection, specifically the relationship between computers and the human nervous system. Wiener pioneered this fascinating new hybrid field of anthro-cyber, which sprouted up in Ivy League University lecture halls and amphitheaters over half a century ago!
By the late 1980s, with the help of Gizmodo, we have come to assume that cyber equates to anything futuristic. Enter the dystopian cyberpunk scene. Two words: Blade Runner. More on this gloriously gritty high-tech and low-life sub-genre and philosophy in a future article.
Chat rooms and the 1990s
If you were alive when the internet became a household thing, you were fortunate enough to have a family home computer that was split up like a South Beach condominium timeshare for the family’s use. You knew that information, connection and freedom awaited whenever this incredible sound played out.
My teenage son’s generation probably cannot imagine listening to this anytime they want to go online. Go a step further and imagine a time when no one could use the house landline when you were surfing the web. Oh yeah, and smartphones didn’t exist! Remember the beeper? Yes, tech has come a long way! Ahhh the nostalgia of it all!
The 1990s spawned a new generation of tech-savvy gifts and challenges to navigate. Indeed, “to cyber” became synonymous with crude advances that took place within IRC chat rooms and other online forums, leaving a poor taste in the mouths of those coming of age in this era.
For adolescents on the cusp of the millennium, it was standard protocol to be met with questions about your height, weight and chest size as pre-qualifiers and acceptance into these new virtual hangouts.
With a sense of adventure, trepidation and newfound liberation, it felt like you were collecting a virtual stream of infinite consciousness and knowledge, and yet, like any worthy quest, the path was littered with cyber IEDs you hoped to avoid along the way!
Females would strategically masquerade as males in order to avoid such behavior and meaningfully participate in tech-focused conversations in this 8-bit profile icon era.
The tone promoted and carried through was, “This is not a place for your intellect.” In dating terms, it became a catch and release for intellectual conversing strategy rather than the modern-day catfish scenarios that might come to mind.
With the emergence of the new millennial digital era, now commonplace in how we communicate at home, at work (and yes in the dating world), webcams, voice-to-voice software and video streaming, humanity has descended upon all things cyber, taking (some of) the sting away for those of us who nervously waded our way through the aforementioned chat rooms and discussion forums.
Cyber and commerce
In 2005, American retailers debuted Cyber Monday, the day after Thanksgiving which on November 30th, 2020 became the biggest day for online shopping in U.S. history at 10.7 billion in sales.
Any owner of a brick-and-mortar store will tell you that COVID-19’s impact on storefronts also played a role in the growth of online commerce; however, omni-channel retailing has been gaining traction since 2010.
Considering how deeply ingrained the term “cyber” has become in millennial and Gen Z lexicon, many of us may not even question its origins. Others see the loosey-goosey use of the term in marketing campaigns and daily convo to be, at times, irresponsible.
Today, when we talk about cybersecurity (cyber security, cyber-security – all acceptable) we often refer to the technology. Investigating the elements of control and humanity in this growing sector will help proliferate understanding of our role when it comes to all things truly cyber – our collective vision, goals and objectives to safeguard our society.
Bringing the humanity back to cyber
The industry is growing out of necessity to mitigate the ever-evolving and shifting digital threat landscape. It is helpful to remember that when we combine cyber + security, we find ourselves with the concepts of governance and order (of security) as they relate to technology and the people.
Understanding cyber’s root origin and evolution aids us to gain clarity and appreciation for the term and its intentions as well as to move away from the image of the stereotypical black hat hacker in a dark hoodie, illuminated by the glow of a laptop or the Edward Snowdon archetype.
Many experts in the field work to promote this intersection of humanity and cyber as they educate the public on how humans can control technology when empowered to do so.
I’d like to see the word “cyber” affirmatively mean the importance of people in control of technology, encouraging all of us to delve deeper into the relationship between that human-technological-control trinity. All too often cyber has been used as a proxy for technology security, ignoring the human and control aspects of the relationship.
– David Shipley, CEO/Cofounder, Beauceron Security
My intention is to make cyber accessible and digestible for all and to support the preservation of its original context in the present day. This article aims to introduce some critical thinking and relatable examples for the buzzword “cyber,” as we see it often used today to promote cutting-edge products or a futuristic ideal.
About the Author: Melissa Parsons, Security Manager, CISSP, ITIL, ISO 27001 Lead Auditor Melissa helps organizations enhance governance, risk and compliance (GRC) strategies and response activities related to cyber, information security and privacy. Over the last eight years, Melissa has managed increasingly complex IT, security and privacy related projects on behalf of not-for-profit, public and private organizations. She is a professional member of (ISC)2, IAPP, ISACA and OWASP, and she regularly participates in local chapter activities and collaborates on international projects, trainings and presentations.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” The Humanity and Evolution of Cyber” appeared first on TripWire
