User Created Content with Tripwire Configuration Manager

Tripwire Configuration Manager allows for user created configuration and compliance management content via a new Policy Management capability. Custom user content can be used alongside existing cloud service provider and third-party SaaS policies, providing multiple new use cases for data gathering and expanding policy compliance support into new services. This blog will describe some of the features and use cases for the Policy Management capability.
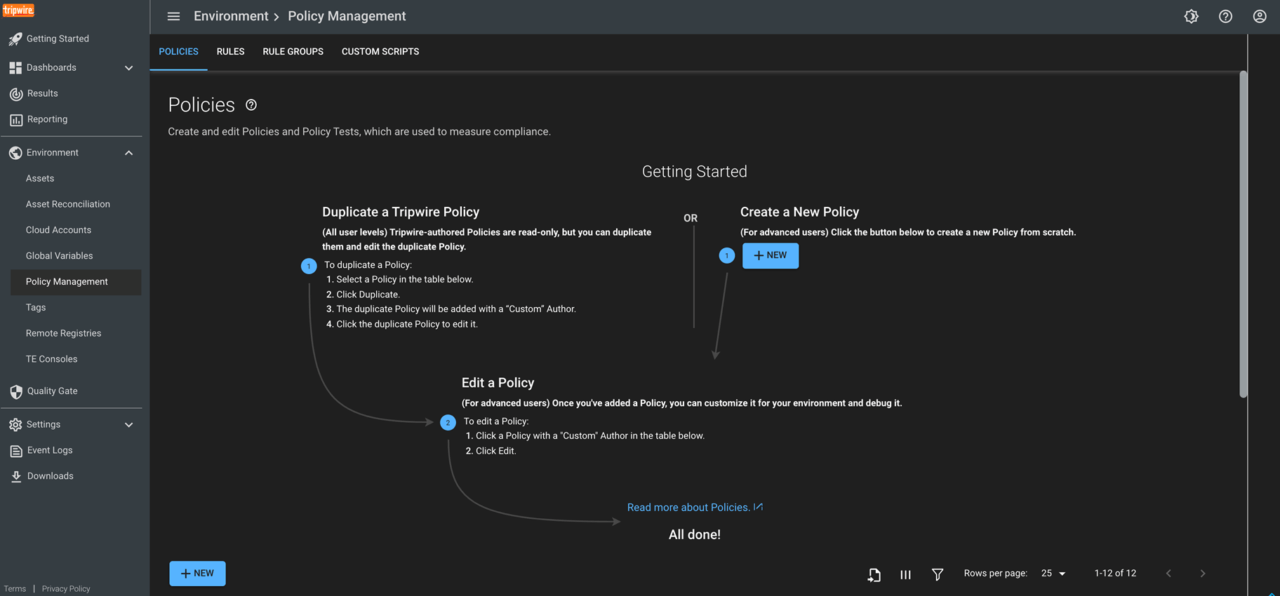
Configuration Manager Policy Management
Configuration Manager Policy Management allows creating, editing, importing, and exporting of the data inventory and policy content which drives Configuration Manager. The internal IDE (Integrated Development Environment) allows for content creation and debugging within the Tripwire.IO user-interface.
While using Configuration Manager, users may want additional information on how data is being gathered or how a response will remediate a non-compliant issue. Tripwire official content can be reviewed in the Policy Management section for greater operational understanding.
Tripwire official policy content can also be duplicated and then modified within the Policy Management section, allowing enhancement or expansion of existing content. This could be used to enhance a security control by requiring more secure values than traditionally recommended.
Creating Custom User Content
Along with modifying existing content, users can create new custom rules and tests, to extend data gathering and compliance within a cloud platform. This allows for checking or enforcing settings and inventory which may have been out of scope for a CIS (Center for Internet Security) policy benchmark but are still important to your organization.
Further, users can create content for entirely new platforms by creating custom cloud accounts and using the Configuration Manager custom scripting capability or REST built-in helpers. The entire Configuration Manager workflow for gathering inventory data, charting, and measuring compliance and even remediation can be applied to new services with compatible API access. Import and Export functionality allows for sharing content between accounts.
To begin experimenting with custom user content, locate the Policy Management section within the Environment menu to get started. As always, information on content creation is available in the getting started help documentation. This can be found in the left-hand navigation menu within Configuration Manager. Note that custom policy content is not available for trial users.
In a future blog, we will discuss more in depth usage of the Policy Management capability to create your own custom content.
Try Tripwire Configuration Manager free for 30 days and discover how Tripwire can keep your cloud accounts compliant with best practice configurations by automatically remediating and enforcing common secure configurations.
The post ” User Created Content with Tripwire Configuration Manager” appeared first on TripWire
Source:TripWire – Ben Layer
