Types of Penetration Testing

If you are thinking about performing a penetration test on your organization, you might be interested in learning about the different types of tests available. With that knowledge, you’ll be better equipped to define the scope for your project, hire the right expert and, ultimately, achieve your security objectives.
What is penetration testing?
Penetration testing, commonly referred to as “pen testing,” is a technique that simulates real-life attacks on your IT systems to find weaknesses that could be exploited by hackers. Whether to comply with security regulations such as ISO 27001, gain customer and 3rd party trust, or achieve your own peace of mind, penetration testing is an effective method used by modern organizations to strengthen their cyber security posture and prevent data breaches.
Read about the different types of penetration testing to find out which type you can benefit from the most:
Network penetration testing
As the name suggests, a network penetration test aims to identify weaknesses in your network infrastructure, be that on the premises or in cloud environments. It is one of the most common and crucial tests to perform to ensure the security of your business-critical data.
Network penetration testing covers a broad range of checks, including insecure configurations, encryption vulnerabilities, and missing security patches in order to determine the steps a hacker could take to attack your organization. Security professionals often categorize this test into two different perspectives: external and internal.
External penetration testing involves searching for vulnerabilities that could be exploited by any attacker with access to the internet. In this scenario, penetration testers are trying to get access to your business-critical systems and data in order to determine how an attacker without any prior access or knowledge would be able to target your organization. You can think of this test as being performed from the perspective of an “outsider”.
In contrast, internal penetration testing is concerned with testing your internal corporate environment. This type of testing considers scenarios in which an attacker has managed to gain an initial foothold within your corporate network, for example by exploiting a vulnerability in one of your internet-facing systems, or through the use of social engineering. In this case, the test is performed from an “insider” perspective, with an objective of finding a way to steal sensitive information or disrupting the operations of an organization.
Generally speaking, external weaknesses are considered to pose a more serious threat than internal. For one thing, a hacker has to overcome an external security barrier before accessing your internal networks and pivoting to other systems. If you haven’t conducted any kind of penetration testing before, an external or “perimeter” test is often the best place to start, as the perimeter is the easiest thing for attackers to get to. If you have trivial vulnerabilities in your internet-facing infrastructure, that’s where the hackers will start.
Web application penetration testing
Web application penetration testing attempts to uncover vulnerabilities across websites and web applications, such as e-commerce platforms, content management systems, and customer relationship management software. This type of test deals with reviewing the entire web application’s security, including its underlying logic and custom functionalities, to prevent data breaches.
Some of the common vulnerabilities detected during a web app penetration test include database injections, cross-site scripting (XSS), and broken authentication. If you are interested in learning more about different types of web application weaknesses, their severity and how you can prevent them, the Open Web Application Security Project (OWASP) Top 10 is a great place to start. Every few years OWASP publishes information about the most frequent and dangerous web application flaws, basing its findings on the data collected from many thousands of applications.
Considering the prevalence of web applications in modern organizations, and the valuable information that they transmit and store, it is unsurprising that they are an attractive target to cybercriminals. According to Verizon’s “2021 Data Breach Investigations Report”, the proportion of incidents, which involved web application assets, reached nearly 50%. For this reason, organizations that are developing or managing their own internet-facing applications should strongly consider conducting web application penetration testing.
Automated penetration testing
Understandably, as penetration tests can be costly and infrequent (only run once or twice per year), many people naturally wonder if automated penetration testing is feasible.
While it’s not possible to fully automate a penetration test (as there will always be an element of manual work conducted by skilled professionals), it’s similarly impossible for humans to manually check for every vulnerability that exists, there are simply too many. That’s where vulnerability scanning comes in, with these tools you can: schedule scans; get rapidly tested for many thousands of weaknesses; and be notified of your results in a variety of channels and formats. It’s no wonder that vulnerability scanners form a critical part of a penetration testers toolkit.
One such tool that you can explore is Intruder. It offers automated security scanning that is designed to be simple and fast, so you can get set-up and protected in little to no time. Intruder includes Emerging Threat Scans, which proactively check your systems for newly discovered vulnerabilities as soon as they are disclosed.
It may not be a fully automated penetration test, but it certainly is like having an automated penetration tester watching over your systems. When you combine continuous vulnerability scanning with an annual penetration test, you can rest assured that your systems are covered by a robust and comprehensive cyber security program.
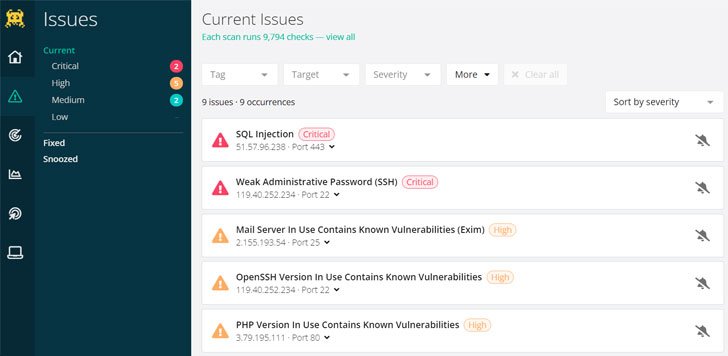 |
| Intruder automatically separates purely informational results from actionable issues, significantly saving technical teams time on analyzing their scan results. |
If you’d like to see the automated tool in action, you can take Intruder’s Pro Plan for a spin with the 30-day free trial.
Social engineering
In comparison to previously described penetration testing types, which focus on finding weaknesses in technology, social engineering attempts to compromise the security of an organization by exploiting human psychology. It can take a variety of forms and could be executed both remotely, for example by trying to obtain sensitive information from users through phishing emails or phone calls, or on-site, in which case a penetration tester will attempt to gain access to a physical facility. In all cases, an objective of this penetration test is to manipulate individuals, usually the company’s employees, to give away valuable information.
The success of a social engineering penetration test largely depends on the information gathered in the “reconnaissance” phase, which involves researching targeted individuals or an organization by using publicly accessible open-source intelligence (OSINT). After building a more precise image of their target, a penetration tester can use discovered information to proceed with the creation of a tailored attack strategy.
One of the most common attack vectors in social engineering is a phishing attack, usually delivered by email. When performing a phishing attack, a penetration tester does not necessarily stop when an unsuspecting employee clicks on a malicious link, but can go further, attempting to steal user credentials and get access to an employee’s laptop. Such attacks can be extremely successful, especially when performed by experienced penetration testers.
Social engineering penetration testing is not as widely adopted as network or web application testing. However, if your organization is already doing regular security awareness training, conducting a dedicated social engineering test can be a great addition to your arsenal for identifying and fixing security issues in your operations.
Red teaming
This advanced technique has its origin in military training exercises. It is designed to challenge an organization’s security, processes, policies and plans by adopting an adversarial mindset. In contrast, Blue teaming, otherwise known as “defensive security,” involves detecting and withstanding Red team attacks as well as real-life adversaries.
Red Teaming combines digital, social and physical domains to implement comprehensive real-life attack scenarios. As such, Red Teaming can be considered a distinct operation from penetration testing, but since its tasks span all of the penetration testing types described above, we thought it was worth mentioning it in this article.
An objective of a standard penetration test is to find as many vulnerabilities as possible within a given timeframe. The breath of this test is naturally limited by the scope of work; but real-life adversaries don’t have such artificial restrictions to follow. As a result, even if an organization regularly performs penetration tests and vulnerability scans, it can still be exposed to more sophisticated attacks such as where social engineering and internal network weaknesses are chained together. This is where Red Teaming comes in. It assesses an organization’s environment as a whole, understanding how all parts function together. It then applies critical thinking to discover new vulnerabilities that attackers can exploit, helping the organization to assess its response to real-world attacks.
Compared to the standard penetration test, which lasts several days or weeks, Red Team assessments generally take much longer, in some cases several months to complete. Due to its complex nature, it is a rather rare operation, typically performed by larger organizations or by government contractors with well-established security programmes.
To conclude
Penetration testing is a broad discipline that encompasses different techniques, so it is important to understand the relative risks that your organization is facing in order to choose the most appropriate type. If you are still unsure what type of testing is appropriate for your organization, you can reach out to Intruder’s team of experienced penetration testers, who will be able to help you.
About Intruder
Intruder is an international cyber security company that helps organizations reduce their cyber exposure by providing an effortless vulnerability scanning solution. Offering industry-leading security checks, continuous monitoring, and an easy-to-use platform, Intruder keeps businesses of all sizes safe from hackers.
Visit their website to find out more about Intruder and to try their online vulnerability scanner for free.
The post “Types of Penetration Testing” appeared first on The Hacker News
