TrickBot Malware Warning Victims of Infection by Mistake

Security researchers observed some variants of the TrickBot malware family mistakenly warning victims that they had suffered an infection.
Advanced Intel’s Vitali Kremez traced the mistake to “password-stealing grabber.dll.” This module is responsible for stealing browser credentials and cookies from Google Chrome, Microsoft Edge and other web browsers that are stored on a victim’s machine. Upon receiving this collected information, those responsible for TrickBot can then use the credentials to authenticate themselves on a victim’s accounts.
Kremez observed that the TrickBot attackers had specifically deployed their malware with a test version of password-stealing grabber.dll. Upon execution, that module spawned a warning message in a victim’s browser informing them that a program was gathering their browser information.
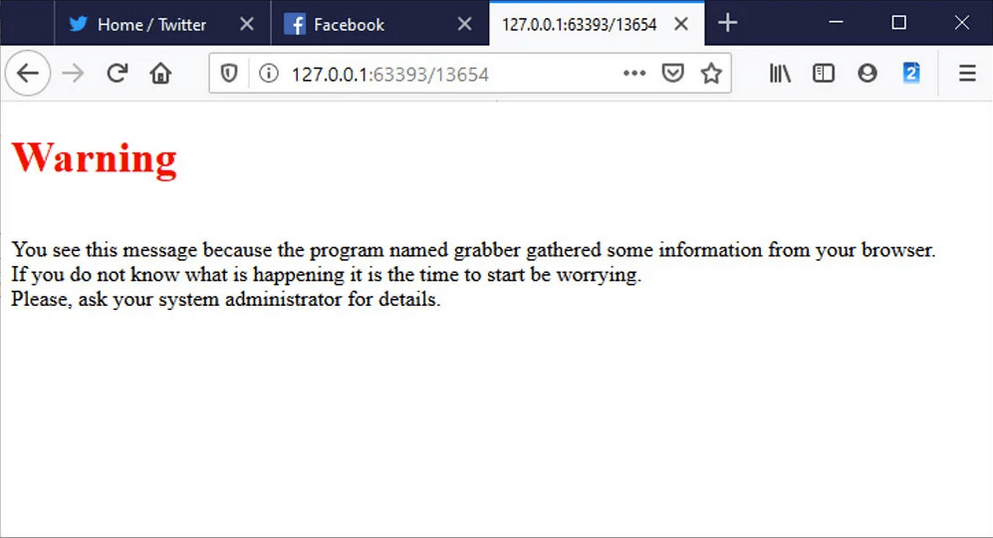
Warning
You see this message because the program named grabber gathered some information from your browser.
If you do not know what is happening it is the time to start be worrying.
Please, ask your system administrator for details.
Reflecting on his discovery, Kremez told Bleeping Computer that the TrickBot gang had likely been testing a new feature and had neglected to remove that warning message when they began distributing it in the wild.
This wasn’t the first time that TrickBot made news at the end of H1 2020. In mid-June, for instance, researchers came across an attack email that leveraged a fake Black Lives Matter voting campaign to distribute Trickbot malware. That was a few weeks before security analysts spotted Trickbot malware checking the screen resolution as a means of evading analysis on a virtual machine (VM). About a week later, security researchers observed Conti ransomware sharing the same TrickBot infrastructure as used by Ryuk for its attack campaigns.
Kremez instructed any victims who saw the warning message displayed above to disconnect their computers from the network and to perform a scan using their anti-virus software. Once the malware is removed, they should change the credentials for any web accounts whose data they might have stored in their web browsers.
The post ” TrickBot Malware Warning Victims of Infection by Mistake” appeared first on TripWire
Source:TripWire – David Bisson
