Survey: 99% of Security Pros Struggling to Secure Their IoT & IIoT Devices

Organizations are increasingly introducing new Internet of Things (IoT) devices into their environments. According to Statista, the aggregate number of IoT devices deployed by organizations globally increased from 7.74 billion in 2019 to around 8.74 billion a year later. The market and consumer data firm reported that the next few years will see growth in all types of IoT devices, including Industrial Internet of Things (IIoT) offerings like smart monitors. It wrote that connected devices are expected to grow from 10.07 billion in 2021 to 25.44 billion by 2030.
This growth raises an important question: how are security professionals feeling about this projected influx of IoT and IIoT devices? Do they feel confident in their ability to secure these additional products? What approaches are they using to fuel their security efforts?
To answer this question, Tripwire partnered with Dimensional Research to conduct a survey between March 3 and March 10, 2021 of individuals who were directly responsible for IoT security at their company. Their responses helped to illuminate the approaches, challenges and opinions of security professionals toward connected devices in their enterprise environments and industrial infrastructure.
Challenges with Securing Devices
Of the 312 security professionals who participated in the survey, 99% of them informed Tripwire that they had encountered challenges in the process of securing their organization’s IoT and IIoT devices. Two-thirds of those respondents said that they had experienced difficulty in their attempts to discover and remediate vulnerabilities. They were followed closely by those who encountered issues in tracking an inventory of their IoT devices (60%), validating compliance with security policies (58%), establishing secure configurations (56%) and detecting changes on those devices (55%). More than a third (37%) of security professionals also revealed that they had a hard time gathering forensic data after a detected incident.
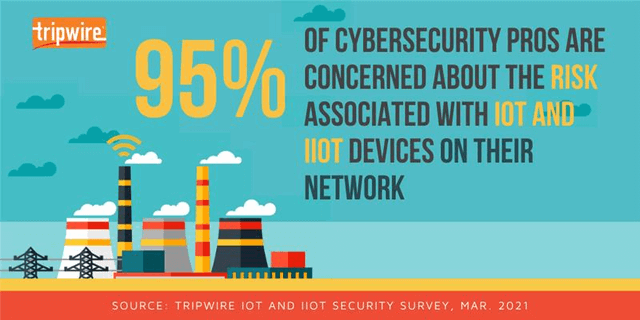
Acknowledging those challenges, it’s not surprising that 53% of survey participants said that they were somewhat concerned about the risks associated with those devices. Another 42% of respondents indicated that they were very concerned about those security risks.
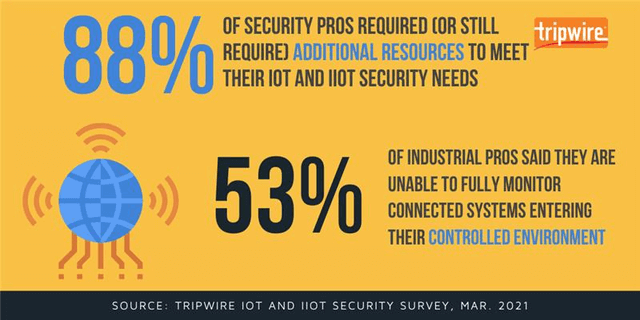
Tripwire asked those security professionals to expand upon those risks. In the process, more than three quarters of respondents clarified that they were worried their organization’s connected devices didn’t fit within their existing security approach, with 88% fearful that they would need additional resources to adequately meet the needs of their organization’s IoT and IIoT devices.
These concerns deepened among industrial-minded survey participants. Indeed, 53% of those respondents said that they lacked the ability to fully monitor newly connected systems.

Tim Erlin, vice president of product management and strategy at Tripwire, explained that this finding highlights the need for industrial cybersecurity professionals to gain a better understanding of what’s going on in their environments:
The industrial sector is facing a new set of challenges when it comes to securing a converged IT-OT environment. In the past, cybersecurity was focused on IT assets like servers and workstations, but the increased connectivity of systems requires that industrial security professionals expand their understanding of what’s in their environment. You can’t protect what you don’t know.
Securing the Industrial Supply Chain
That wasn’t the only visibility issue that respondents brought up with Tripwire.
Indeed, 61% of industrial cybersecurity professionals said that they didn’t have visibility into the types of changes that security vendors in their supply chain might be experiencing. A majority (97%) of those survey participants said that they therefore had concerns about the security of their supply chain. More than four-fifths (87%) of them said that they were specifically worried about the supply chain security risks introduced by existing IoT and IIoT security guidelines.
Erlin wasn’t surprised to learn of this:
It’s understandable that managing supply chain risk is top of mind for industrial security teams given the level of attack we have seen this year. Large-scale supply chain risk isn’t new, so if anything, this should encourage companies to invest in resources that help maintain a more secure environment.
It appears that some companies are heeding Erlin’s advice. More than half (59%) of respondents explained that their organization’s budget for managing supply chain security had increased in the past year. That spending could support the 88% of security professionals who are already using PCI, NIST as well as other standards and frameworks to secure their supply chains. Even so, that didn’t prevent professionals in a variety of industrial sectors from stating that their organizations would benefit from expanded security industrial control systems (ICS) standards.
How Tripwire Can Help
Organizations can work with Tripwire to evaluate the security of their connected devices. Using security assessments, Tripwire can evaluate those devices for security risks and vulnerabilities that exist in those devices’ physical construction as well as for potential weaknesses in the ways in which organizations have configured them. Learn more about those assessments here.
To download the full survey results, click here: https://www.tripwire.com/misc/iot-and-iiot-cybersecurity-report
The post ” Survey: 99% of Security Pros Struggling to Secure Their IoT & IIoT Devices” appeared first on TripWire
Source:TripWire – Jess Glackin
