New Attack Abused Windows Error Reporting Service to Evade Detection

Security researchers came across a new attack that abused the Windows Error Reporting (WER) service in order to evade detection.
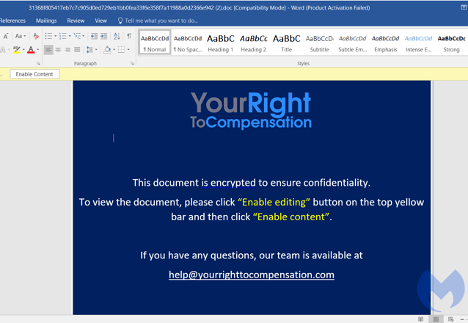
Malwarebytes observed that the attack began with a .ZIP file containing “Compensation manual.doc.”
The security firm reasoned that those responsible for this attack had likely used spear-phishing emails to distribute the document, a file which pretended to contain information about workers’ rights.
This document harbored a malicious macro that used a modified version of the CactusTorch VBA module to conduct a fileless attack by loading a .Net compiled binary into memory using VBScript to execute it.
Named “Kraken.DLL,” this binary advanced the infection chain by injecting embedded shellcode into the Windows Error Reporting service (WerFault.exe). Malwarebytes explained in its research that this tactic might have helped the attack attempt to evade detection:
WerFault.exe is usually invoked when an error related to the operating system, Windows features, or applications happens. When victims see WerFault.exe running on their machine, they probably assume that some error happened while in this case they have actually been targeted in an attack.
The injected shellcode created a DLL that executed its malicious activity in multiple threads in order to evade detection. More than that, the DLL also performed several anti-analysis routines such as checking for the existence of a debugger and looking to see if it was running in VmWare or VirtualBox.
Assuming those checks came back negative, the loader created its final shellcode in a new thread. This shellcode, in turn, used an HTTP request to connect to a hard-coded domain, download a malicious payload and inject it into a process.
The security firm reasoned that this payload was another shellcode hosted on a compromised website. Even so, the URL was down at the time of analysis, so it couldn’t investigate further.
Malwarebytes explained that APT32 might have been behind this campaign given the fact that it’s observed the threat actor use CactusTorch HTA to drop the Denis Rat in the past.
The post ” New Attack Abused Windows Error Reporting Service to Evade Detection” appeared first on TripWire
Source:TripWire – David Bisson
