Expert Tips on How to Spot a Phishing Link
Phishing attacks are becoming more advanced and harder to detect, but there are still telltale signs that can help you spot them before it’s too late. See these key indicators that security experts use to identify phishing links:
1. Check Suspicious URLs
Phishing URLs are often long, confusing, or filled with random characters. Attackers use these to disguise the link’s true destination and mislead users.
The first step in protecting yourself is to inspect the URL carefully. Always ensure it begins with “HTTPS,” as the “s” indicates a secure connection using an SSL certificate.
However, keep in mind that SSL certificates alone are not enough. Cyber attackers have increasingly used legitimate-looking HTTPS links to distribute malicious content.
This is why you should be suspicious of links that are overly complex or look like a jumble of characters.
Tools like ANY.RUN’s Safebrowsing allow users to check suspicious links in a secure and isolated environment without the need to manually inspect every character in a URL.
Example:
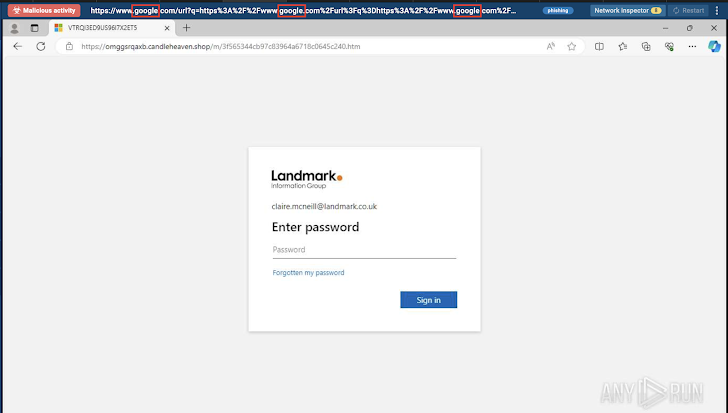
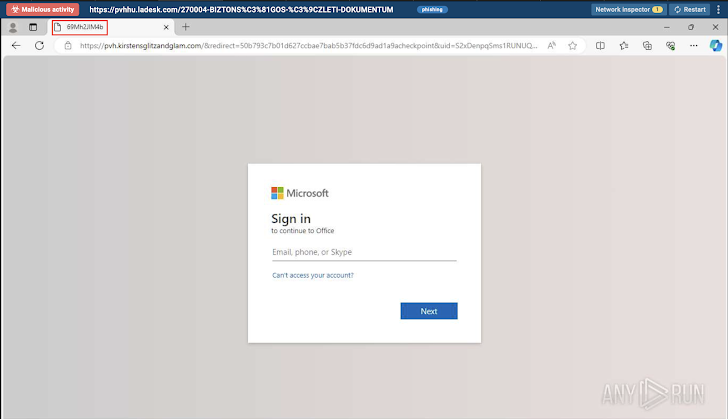
One of the recent cases involved Google’s URL redirect being used several times to mask the real phishing link and make it difficult to trace the true destination of the URL.
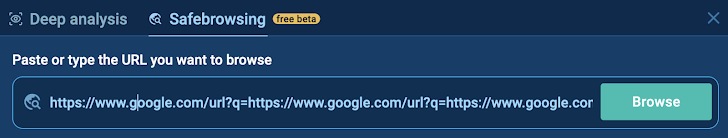  |
| Complex URL with redirects |
In this case, after the initial “Google” in the URL, you see 2 other instances of “Google,” which is a clear sign of a redirection attempt and misuse of the platform.
  |
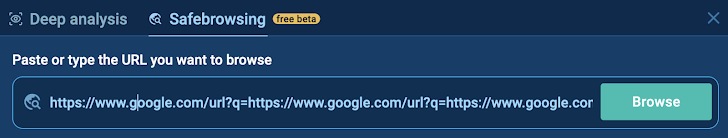
| Analysis of suspicious link using ANY.RUN’s Safebrowsing feature |
2. Pay Attention to Redirect Chains
As you can see from the example mentioned above, redirecting is one of the main tactics used by cyber attackers. Besides considering the complexity of the URL, find out where the link leads you.
This tactic extends the delivery chain and confuses users, making it harder to spot the malicious intent.
One more common scenario is when attackers send an email, claiming a file needs to be downloaded. But instead of an attachment or direct link, they send a URL leading through redirects, ultimately asking for login credentials to access the file.
To investigate this safely, copy and paste the suspicious link into ANY.RUN’s Safebrowsing tool. After running the analysis session, you’ll be able to interact with the link in a secure environment and see exactly where it redirects and how it behaves.
Example:
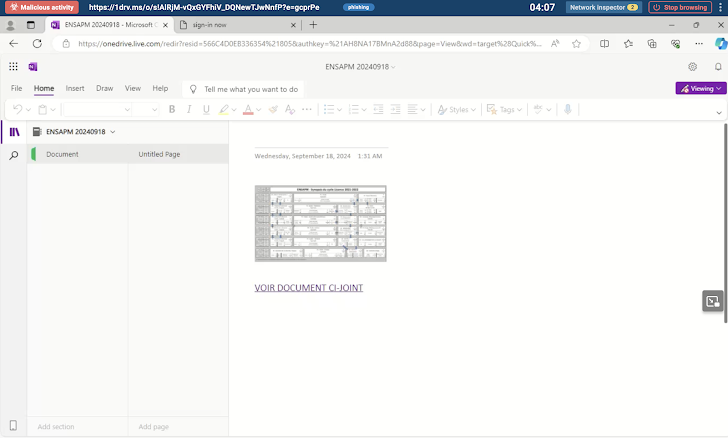  |
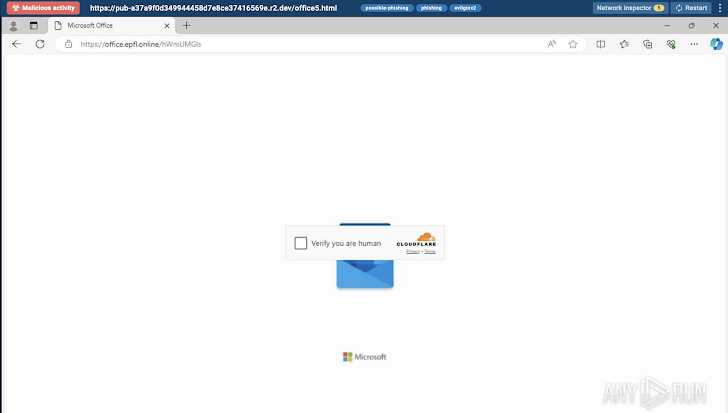
| Redirect chain displayed in ANY.RUN’s VM |
In this instance, attackers shared a seemingly harmless link to a file storage page. However, instead of leading directly to the intended document, the link redirected users multiple times, eventually landing on a fake login page designed to steal their credentials.
3. Inspect Strange Page Titles and Missing Favicons
Another way to spot phishing links is paying attention to the page titles and favicons. A legitimate page should have a title that matches the service you’re interacting with, without strange symbols or gibberish. Suspicious, random characters or incomplete titles are often signs that something is wrong.
Besides the page title, valid websites have a favicon that corresponds to the service. An empty or generic favicon is an indication of a phishing attempt.
Example:
  |
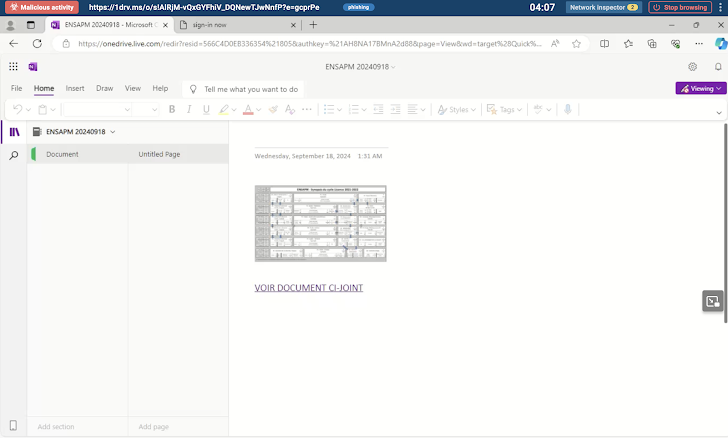
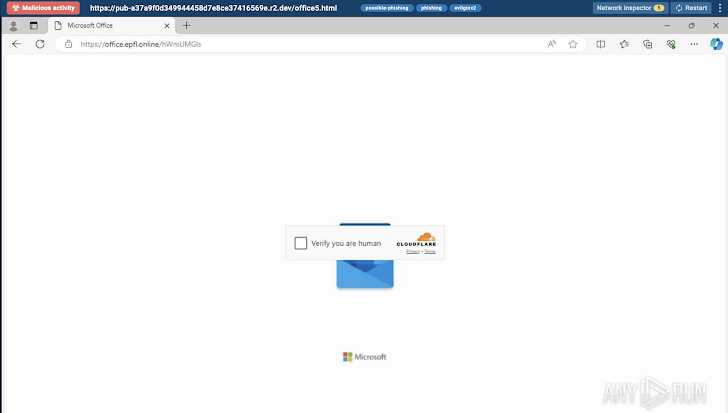
| Suspicious page title along with broken Microsoft favicon analyzed inside ANY.RUN |
In this Safebrowsing session, you’ll notice how the page title and favicon don’t align with what you would expect from a legitimate Microsoft Office login page.
Normally, you would see the Microsoft favicon along with a clear, relevant page title. However, in this example, the title consists of random numbers and letters, and the Microsoft favicon is broken or missing. This is a major red flag and likely indicates a phishing attempt.
4. Beware of Abused CAPTCHA and Cloudflare checks
One common tactic used in phishing links is the abuse of CAPTCHA systems, particularly the “I’m not a robot” verification.
While CAPTCHAs are designed to verify human users and protect against bots, phishing attackers may exploit them by adding unnecessary, repetitive CAPTCHA challenges on malicious websites.
A similar tactic involves the misuse of services like Cloudflare, where attackers may use Cloudflare’s security checks to slow down users and mask the phishing attempt.
Example:
  |
| Cloudflare verification abuse observed in ANY.RUN’s Safebrowsing session |
In this analysis session, attackers use Cloudflare verification as a deceptive layer in their phishing scheme to add legitimacy and obscure their malicious intent.
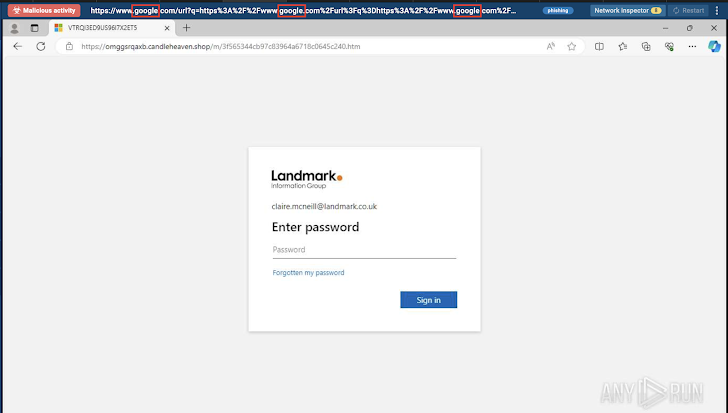
5. Verify Microsoft Domains Before Entering Passwords
Phishers often create websites that mimic trusted services like Microsoft to trick users into providing their credentials. While Microsoft typically asks for passwords on a few official domains, it’s important to remain cautious.
Here are some of the legitimate Microsoft domains where password requests may occur:
Keep in mind that your organization may also request authentication through its official domain. Therefore, it’s always a good idea to verify the link before sharing the credentials.
Use ANY.RUN’s Safebrowsing feature to verify the legitimacy of the site before entering any sensitive information. Make sure to protect yourself by double-checking the domain.
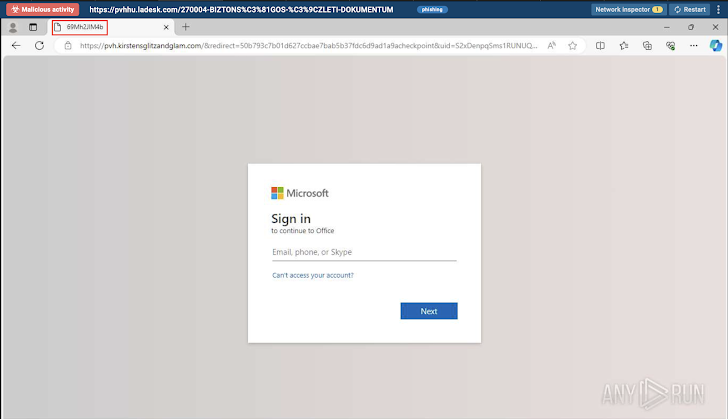
6. Analyze Links with Familiar Interface Elements
You can also spot phishing links by closely examining the interface elements of programs. Keep in mind that program interface elements on a browser page with a password input form are a major warning sign.
Attackers often attempt to gain users’ trust by mimicking familiar software interfaces, such as those from Adobe or Microsoft, and embedding password input forms within them.
This makes potential victims feel more comfortable and lowers their defenses, ultimately leading them into the phishing trap. Always double-check links with such elements before entering sensitive information.
Example:
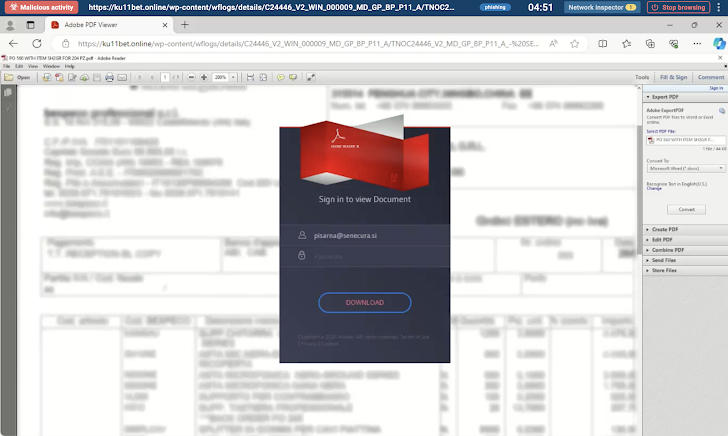 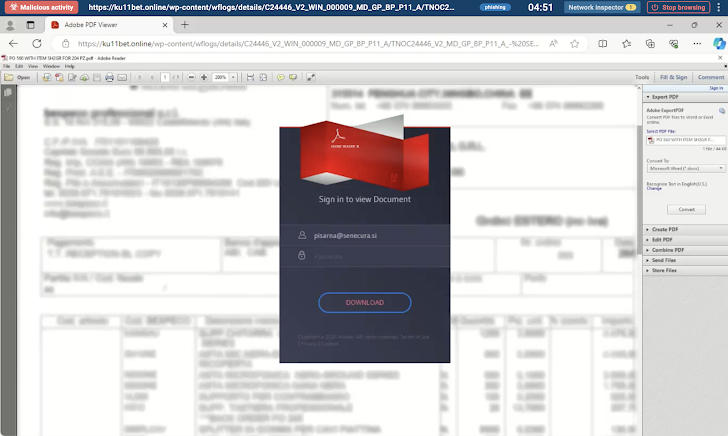 |
| Interface elements mimicking Adobe PDF Viewer |
In this Safebrowsing session, attackers mimicked Adobe PDF Viewer, embedding its password input form.
Explore Suspicious Links in ANY.RUN’s Safe Virtual Browser
Phishing links can be incredibly damaging to businesses, often leading to the compromise of sensitive information like login credentials and financial data with just a single click.
ANY.RUN’s Safebrowsing offers a secure, isolated virtual browser where you can safely analyze these suspicious links in real-time without risking your system.
Explore suspicious websites safely, inspect network activity, detect malicious behaviors, and gather Indicators of Compromise (IOCs) for further analysis.
For a deeper level of analysis on suspicious links or files, ANY.RUN’s sandbox provides even more advanced capabilities for threat detection.
Start using ANY.RUN today for free and enjoy unlimited Safebrowsing or deep analysis sessions!
The post “Expert Tips on How to Spot a Phishing Link” appeared first on The Hacker News
Source:The Hacker News – [email protected] (The Hacker News)
