DarkGate Malware Spreading via Messaging Services Posing as PDF Files
A piece of malware known as DarkGate has been observed being spread via instant messaging platforms such as Skype and Microsoft Teams.
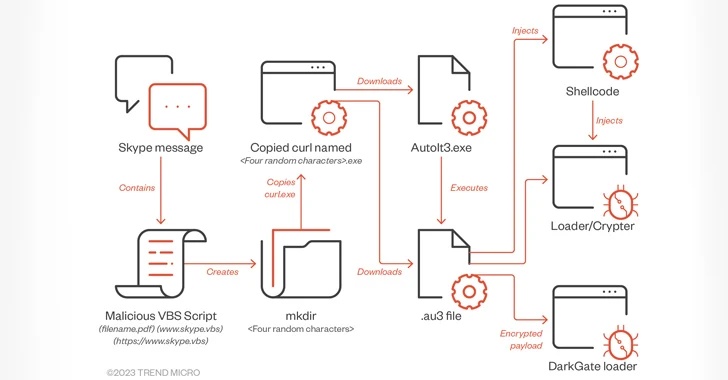
In these attacks, the messaging apps are used to deliver a Visual Basic for Applications (VBA) loader script that masquerades as a PDF document, which, when opened, triggers the download and execution of an AutoIt script designed to launch the malware.
“It’s unclear how the originating accounts of the instant messaging applications were compromised, however it is hypothesized to be either through leaked credentials available through underground forums or the previous compromise of the parent organization,” Trend Micro said in a new analysis published Thursday.
DarkGate, first documented by Fortinet in November 2018, is a commodity malware that incorporates a wide range of features to harvest sensitive data from web browsers, conduct cryptocurrency mining, and allow its operators to remotely control the infected hosts. It also functions as a downloader of additional payloads such as Remcos RAT.
Social engineering campaigns distributing the malware have witnessed a surge in recent months, leveraging initial entry tactics such as phishing emails and search engine optimization (SEO) poisoning to entice unwitting users into installing it.
The uptick follows the malware author’s decision to advertise the malware on underground forums and rent it out on a malware-as-a-service basis to other threat actors after years of using it privately.
The use of Microsoft Teams chat message as a propagation vector for DarkGate was previously highlighted by Truesec early last month, indicating that it’s likely being put to use by several threat actors.
A majority of the attacks have been detected in the Americas, followed closely by Asia, the Middle East, and Africa, per Trend Micro.
The overall infection procedure abusing Skype and Teams closely resembles a malspam campaign reported by Telekom Security in late August 2023, save for the change in the initial access route.
“The threat actor abused a trusted relationship between the two organizations to deceive the recipient into executing the attached VBA script,” Trend Micro researchers Trent Bessell, Ryan Maglaque, Aira Marcelo, Jack Walsh, and David Walsh said.
“Access to the victim’s Skype account allowed the actor to hijack an existing messaging thread and craft the naming convention of the files to relate to the context of the chat history.”
The VBA script serves as a conduit to fetch the legitimate AutoIt application (AutoIt3.exe) and an associated AutoIT script responsible for launching the DarkGate malware.
An alternate attack sequence involves the attackers sending a Microsoft Teams message containing a ZIP archive attachment bearing an LNK file that, in turn, is designed to run a VBA script to retrieve AutoIt3.exe and the DarkGate artifact.
“Cybercriminals can use these payloads to infect systems with various types of malware, including info stealers, ransomware, malicious and/or abused remote management tools, and cryptocurrency miners,” the researchers said.
“As long as external messaging is allowed, or abuse of trusted relationships via compromised accounts is unchecked, then this technique for initial entry can be done to and with any instant messaging (IM) apps.”
The post “DarkGate Malware Spreading via Messaging Services Posing as PDF Files” appeared first on The Hacker News
Source:The Hacker News – [email protected] (The Hacker News)



