Checking the Windows Store for Patching the Codecs Library Vulnerability

What is the Windows Store?
The Windows Store is a digital platform that allows for the distribution of applications. This platform offers both free and paid. Users use the Window Store to install applications that are of interest to them.
Can you disable the Windows Store?
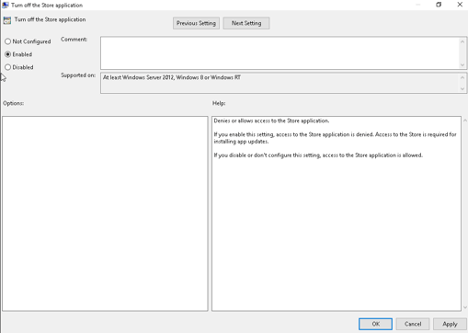
Windows Store can be disabled via group policy to prevent users from installing applications that are not approved. To disable the Windows Store the “Turn off the Store application” group policy has to be enabled. This will prevent users from accessing the Windows Store. However, it disables all access to the Windows Store.
Can an application update when the app store is disabled?
Disabling the Windows Store will leave the default applications or applications that were already installed on the system. The group policy explicitly says that disabling the Windows Store will disable the ability for installed applications to be updated. This could leave an application in a vulnerable state where it cannot receive updates.
Can you disable Windows Store Apps?
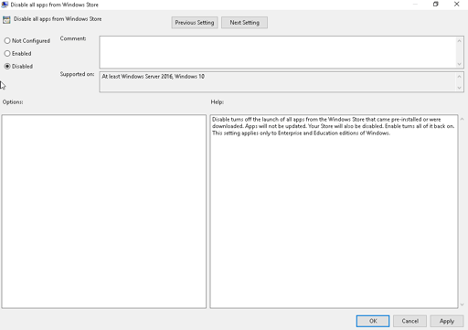
Some versions of Windows 10 ship with default applications installed from the Windows Store. These applications are available for users to execute. However, a group policy can be configured by an administrator to disable these applications from executing. An administrator needs to configure the “Disable all apps from Microsoft Store” setting to prevent all applications installed from the Windows Store from running. To disable applications this configuration option must be set to Disabled. To enable applications this option has to be configured to Enabled. Given the wording of the setting, this logic may seem backward when compared to other group policy settings.

What happens when apps are disabled?
Disabling Windows Store applications leaves the application installed, but the application is unable to run. This means that the application will remain on the system, but not in a usable state. Furthermore, the libraries remain on the system and could potentially be used by another application. If this option is used in conjunction with the disable Windows Store policy then the application may remain in an outdated/vulnerable state.
Why does this matter?
Microsoft released an update for the Windows Codecs library and the patch was release via the Windows Store. This patch is automatically applied on systems that do not block the Windows Store. However, this means that on systems that block the Window Store and have the application installed the system will remain in a vulnerable state. Unfortunately, Microsoft does not mention which application is vulnerable to the vulnerabilities found in the Microsoft Codecs Library. Research indicates that the HEVC Video Extensions application was updated recently and is the vulnerable application that was updated in this week’s Out of Band update (CVE-2020-1425, CVE-2020-1457).
Tripwire IP360 Related Coverage
| VID | Title | Description |
| 448734 | Windows Store Applications are Enabled | The Windows Store Applications are enabled on the Windows system. In this state Windows Applications installed from the Windows Store are able to operate on the system. |
| 448733 | Windows Store Applications are Disabled | The Windows Store applications are disabled on the Windows system. Windows Store Applications in a disabled state cannot run. |
| 448732 | Windows Store is Disabled | The Windows Store is disabled on the Windows system. The Windows Store allows applications to be installed on the Windows system. Windows does come with applications preinstalled from the Windows Store. If the Window Store is disabled the default applications cannot update and stay in an outdated state. |
| 448731 | Windows Store is Enabled | The Windows Store is enabled on the Windows system. The Windows store allows free applications to be installed on the Windows system. |
| 448725 | MS-2020-Jun: Microsoft Windows Codecs Library Remote Code Execution Vulnerability I | The Microsoft Windows codecs library contains a code execution vulnerability. This issue exists because of how the Microsoft Windows codecs library handles objects in memory. If successfully exploited an attacker could execute arbitrary code. To exploit this issue an attacker requires a program to process a specially crafted image file. |
| 448729 | MS-2020-Jun: Microsoft Windows Codecs Library Remote Code Execution Vulnerability II | The Microsoft Windows codecs library contains a code execution vulnerability. This issue exists because of how the Microsoft Windows Codecs library handles objects in memory. If successfully exploited an attacker could obtain information to further compromise the system. To exploit this issue an attacker requires a program to process a specially crafted image. |
The post ” Checking the Windows Store for Patching the Codecs Library Vulnerability” appeared first on TripWire
Source:TripWire – Andrew Swoboda
