Beyond Asset Discovery: How Attack Surface Management Prioritizes Vulnerability Remediation

As the business environment becomes increasingly connected, organizations’ attack surfaces continue to expand, making it challenging to map and secure both known and unknown assets. In particular, unknown assets present security challenges related to shadow IT, misconfigurations, ineffective scan coverage, among others.
Given attack surface sprawl and evolving threats, many organizations are embracing attack surface management (ASM) tools to discover and address critical exposures.
Asset discovery is an important capability to have, and one that’s helping to drive the adoption of attack surface management tools and services. That said, asset discovery is only one aspect of effective attack surface management. Making the attack surface as impenetrable as possible takes offensive security that goes far beyond the discovery phase.
Why Asset Discovery Isn’t Enough
Given the complexity and ever-expanding scale of the digital infrastructure at most companies, cataloging all the known devices and assets is laborious, and discovering all the unknown ones takes deep sleuthing. Building a complete inventory ensures that all devices and assets are subject to the same security measures and that no vulnerabilities are lurking in the shadows. It’s an important and complex step.
However, asset discovery alone is not a solution.
Discover, prioritize, and effectively remediate vulnerabilities with data-driven Offensive Security Vision Report 2023. Get actionable insights based on 300,000+ findings from pentest engagements. Prioritize your defense strategy.
Asset discovery helps security teams gain a comprehensive view of the full attack surface, often referred to as attack surface mapping. What it does not do is help security teams identify weaknesses and vulnerabilities in the attack surface. Most importantly, asset discovery does not support remediation of any of those issues, which means the attack surface remains at risk of being compromised by sophisticated threat actors.
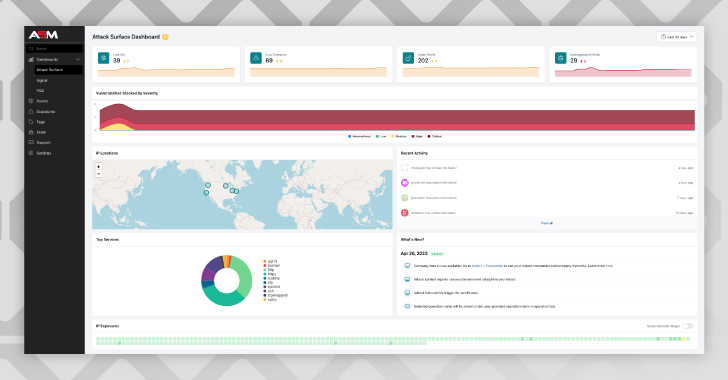 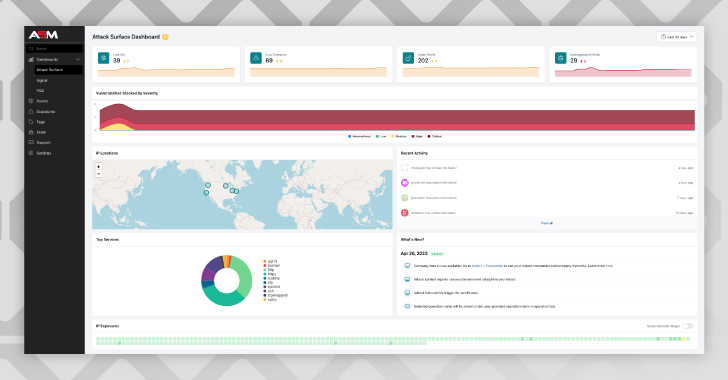 |
| Source: NetSPI Attack Surface Management Platform Home Screen |
Asset discovery improves visibility. For attack surface management to effectively improve an organization’s offensive security program, it must incorporate vulnerability prioritization and remediation as well.
There are many different approaches to vulnerability remediation, with some being more effective than others.
How to Prioritize Vulnerability Remediation
Vulnerability remediation requires multiple phases. The first phase involves finding every weakness in the attack surface – including identifying both known and unknown assets and associated vulnerabilities. Next a vulnerability list is created and ranked by severity so security teams can remediate the most urgent risks first.
Most modern attack surface management tools take this approach to some extent. They call attention to the riskiest vulnerabilities and often outline remediation steps as well. However, the effectiveness of this process depends on the intelligence that informs it. And if the intelligence isn’t sophisticated or backed with human analysis, this means vulnerabilities may get overlooked or under-prioritized. As a result, cyber criminals will have an easier path to breach the attack surface.
What differentiates quality intelligence from the rest? Context, primarily. Vulnerability and risk are complex determinations. And while automation can scan high volumes of data at once, technology alone often struggles or fails to see red flags.
Relying on a combination of technology, a comprehensive methodology, and a human offensive security team with deep experience and cross-domain expertise adds the context that automated vulnerability management tools often lack. The result is better insight into the most critical vulnerabilities, along with smarter strategies to remediate vulnerabilities as quickly, easily, and completely as possible.
Automation is a vital capability, both for asset discovery and vulnerability remediation. But the best outcomes and the strongest possible attack surface happen when expert human teams are also involved.
Select Attack Surface Management Tools Strategically
Getting the full benefits of attack surface management – such as stronger yet more streamlined security – requires thoughtful consideration to select the right tools and vendors.
Look first for a solution that goes beyond asset discovery to enable and improve upon vulnerability remediation. Then prioritize partners that run this process with a human operations team to find a team with tenure.
Global companies trust NetSPI’s experienced team, technology, and comprehensive methodology to discover and address risky exposures before adversaries do. Learn more about NetSPI’s attack surface management capabilities by connecting with the team today.
Note: This expertly contributed article is written by Brianna McGovern. Brianna is NetSPI’s Product Manager of ASM and holds a degree in Industrial Engineering from Penn State University.
NetSPI is the global leader in offensive security, delivering the most comprehensive suite of penetration testing, attack surface management, and breach and attack simulation solutions. Through a combination of technology innovation and human ingenuity NetSPI helps organizations discover, prioritize, and remediate security vulnerabilities. Its global cybersecurity experts are committed to securing the world’s most prominent organizations, including nine of the top 10 U.S. banks, four of the top five leading global cloud providers, four of the five largest healthcare companies, three FAANG companies, seven of the top 10 U.S. retailers & e-commerce companies, and many of the Fortune 500. NetSPI is headquartered in Minneapolis, MN, with offices across the U.S., Canada, the UK, and India.
The post “Beyond Asset Discovery: How Attack Surface Management Prioritizes Vulnerability Remediation” appeared first on The Hacker News
Source:The Hacker News – [email protected] (The Hacker News)

