Android Locker Variant Uses Innovative Sequence to Load Ransom Note

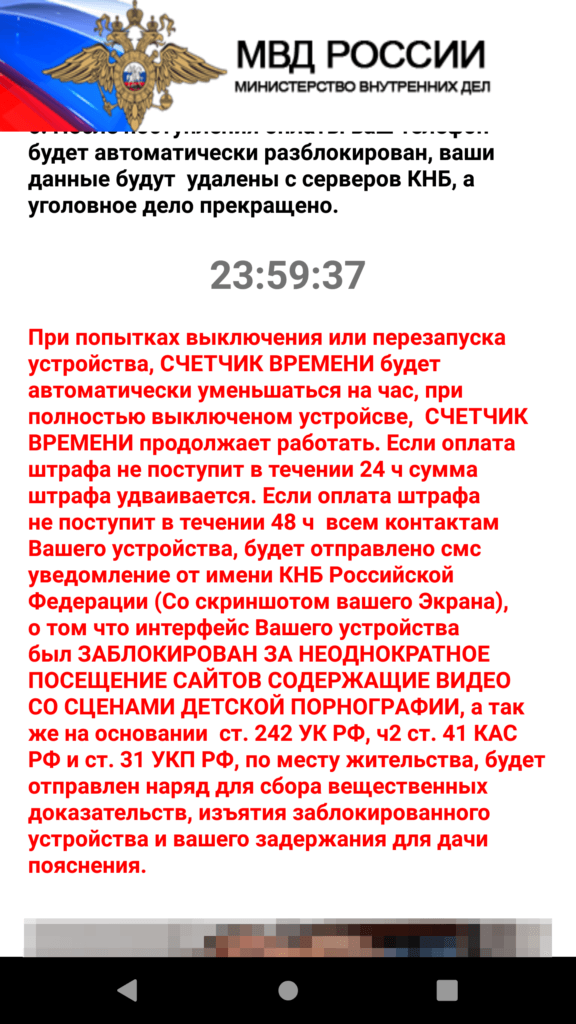
A new variant of a sophisticated Android locker family used an innovative sequence to load its ransom note on infected devices.
On October 8, Microsoft Defender Research Team revealed that it had spotted a new Android locker variant using novel techniques to display its ransom note to its victims.
This threat specifically targeted two components on Android devices: the “call” notification and
In essence, the locker Android locker variant created a notification builder whose notifications (i.e. the ransom note) required special privileges and automatically popped up by being wired to a GUI.
Those responsible for the locker also included code responsible for overriding the onUserLeaveHint() callback function. This tactic helped to ensure that the malware screen would return to the foreground in the event that the user attempted to send it to the background.
The sequence described above differed from other Android ransomware families’ attack chains in that it didn’t abuse “SYSTEM_ALERT_WINDOW,” a special permission for which Google ultimately introduced platform-level changes in early 2019.
Microsoft’s researchers predicted that this particular Android locker family isn’t done evolving. As quoted in their research:
This ransomware family’s long history tells us that its evolution is far from over. We expect it to churn out new variants with even more sophisticated techniques. In fact, recent variants contain code forked from an open-source machine learning module used by developers to automatically resize and crop images based on screen size, a valuable function given the variety of Android devices.
The ongoing evolution of Android locker tactics highlights the need for organizations to defend themselves against a ransomware attack. One of the ways they can do this is by preventing a ransomware infection in the first place.
The post ” Android Locker Variant Uses Innovative Sequence to Load Ransom Note” appeared first on TripWire
Source:TripWire – David Bisson
