Fake Windows Defender Antivirus Theme Used to Spread QBot

Digital attackers incorporated a fake Windows Defender Antivirus theme into a malicious document in order to distribute QBot malware.
According to Bleeping Computer, the QBot gang began using a new template for their email attack campaigns’ malicious documents beginning on August 25, 2020.
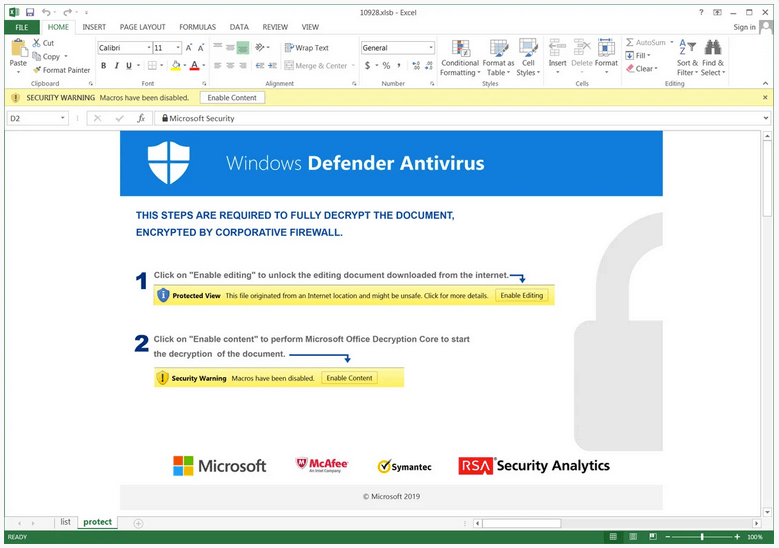
The template adopted the disguise of a Windows Defender Antivirus alert in order to convince the recipient that the malicious document was actually a legitimate email attachment.
To add further legitimacy to their efforts, the actors replicated branding not only pertaining to Windows Defender but also to several other well-known security firms.
Bleeping Computer highlighted the efficacy of this type of disguise in its reporting:
To people who work in cybersecurity, are IT admins, or Windows enthusiasts, the above message appears silly and made up. To casual users, though, it is convincing enough that many would follow the instructions and become infected with Qbot.
Like many others before it, this malicious email attachment attempted to trick the recipient into thinking that they needed to enable the content of the document in order to view it.
If the user went ahead and clicked the “Enable Content” button, the document’s malicious macros executed and subsequently downloaded a sample of QBot onto the victim’s computer.
A botnet known for stealing information and providing remote access to digital attackers, QBot had a busy few months in the third quarter of 2020. The trojan earned a place on Check Point’s Global Threat Index in August 2020. The next month, the malware rose to 6th place on the list.
The growth of QBot along with its use of antivirus alerts as a disguise highlight the need for organizations to defend themselves against malware.
Organizations can protect themselves by investing in a solution that analyzes suspicious files in a quarantined environment and by providing reports about relevant system changes. Learn how Tripwire File Analyzer can help strengthen your anti-malware defenses.
The post ” Fake Windows Defender Antivirus Theme Used to Spread QBot” appeared first on TripWire
Source:TripWire – David Bisson
