Center for Internet Security (CIS) Controls v8: Your Complete Guide to the Top 18
The Center for Internet Security (CIS) controls are a relatively short list of high-priority, highly effective defensive actions that provide a “must-do, do-first” starting point for every enterprise seeking to improve its cyber defense.
Initially developed by the SANS Institute and known as the SANS Critical Controls, these best practices are indispensable to organizations both large and small. By adopting these sets of controls, organizations can prevent the majority of cyberattacks.
18 Critical Security Controls for Effective Cyber Defense
The latest release of the CIS Controls is version eight, which was published in 2021. The list is still prioritized in order of importance, but there are some notable changes to the controls and their order. The controls are now task-focused and combined by activities. Another change is that what were previously called sub-controls are now called safeguards.
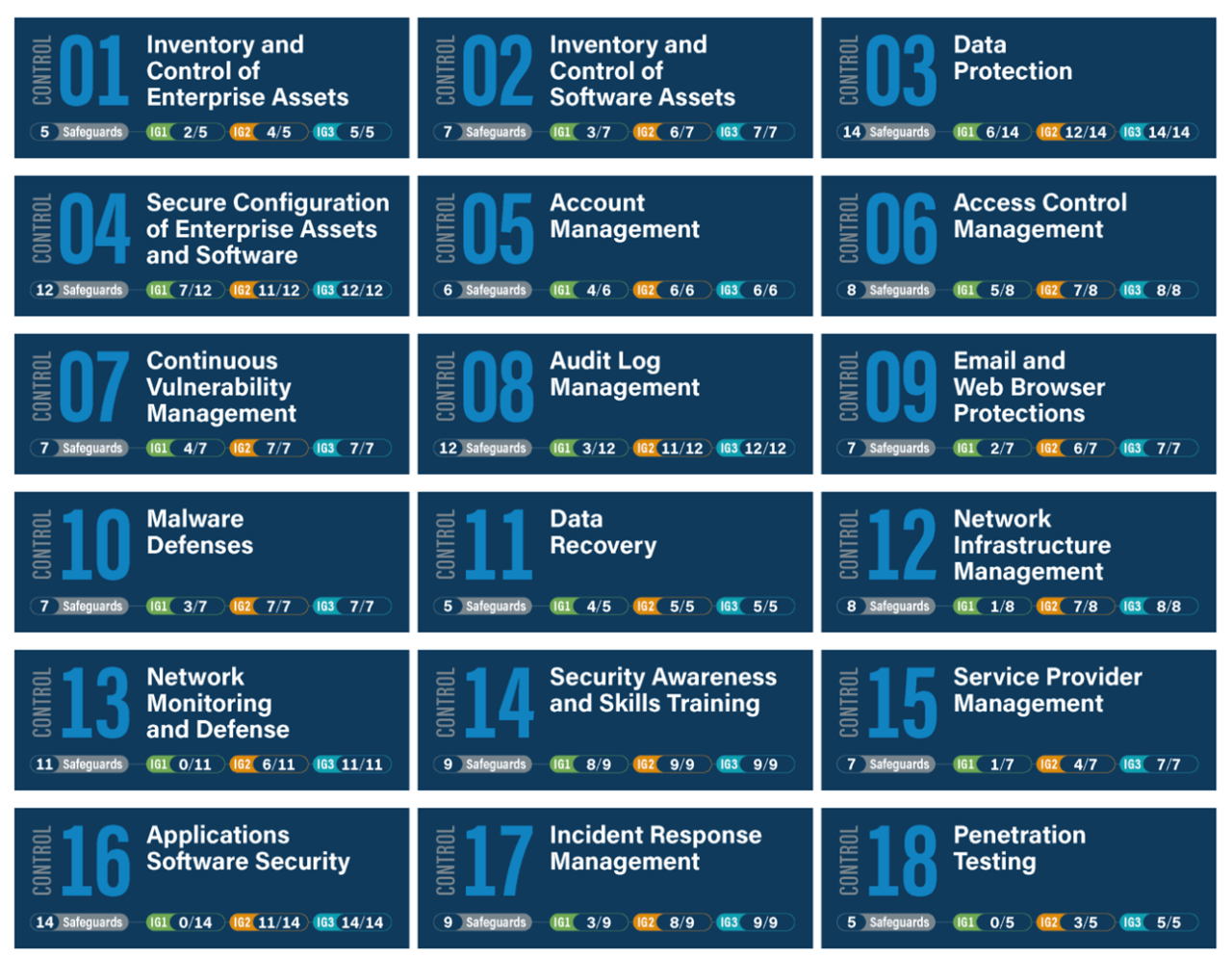
CIS Control 1: Inventory and Control of Enterprise Assets
A comprehensive view of the devices on your network is the first step in reducing your organization’s attack surface. Use both active and passive asset discovery solutions on an ongoing basis to monitor your inventory and make sure all hardware is accounted for.
CIS Control 2: Inventory and Control of Software Assets
Another one of the top controls also deals with asset discovery, making network inventorying the single most critical step you can take to harden your system. After all, you can’t keep track of assets that you don’t know you have on your network.
CIS Control 3: Data Protection
A comprehensive data management plan incorporates the answers to these questions with policy decisions and incident response procedures. Knowing what data an enterprise produces or consumes as well as being able to classify it based on sensitivity are the keystones of such a plan. Despite its simple name, this is one of the more complex and difficult controls to put into practice thanks to ongoing processes like inventorying sensitive information.
CIS Control 4: Secure Configuration of Enterprise Assets and Software
Leverage file integrity monitoring (FIM) to keep track of configuration files, master images, and more. This control speaks to the need for automating configuration monitoring systems so that departures from known baselines trigger security alerts. The systems in scope under this control include mobile devices, laptops, workstations, servers, and other devices.
CIS Control 5: Account Management
In order to keep valid credentials out of hackers’ hands, you must have a system in place to control authentication mechanisms. Administrative credentials are a prime target for cybercriminals. Luckily, there are several steps you can take to safeguard them, such as keeping a detailed inventory of admin accounts and changing default passwords. Monitoring and controlling accounts makes it much harder for malicious actors to successfully attack a company and steal or damage assets.
CIS Control 6: Access Control Management
The first step in implementing this control is inventorying your network’s wireless access points. From there, the control takes a deep dive into mitigating all types of wireless access risks. By encrypting information in transit and disabling communication between workstations, you can also start to limit potential security incidents that can occur when data privileges are overly lax.
CIS Control 7: Continuous Vulnerability Management
A major challenge in cybersecurity involves keeping up with all the common vulnerabilities and exposures (CVEs) identified in real time around the world. Effective security programs have to keep up with a plethora of new vulnerabilities every day. CIS lists continuous vulnerability assessment and remediation as a key part of risk and governance programs.
CIS Control 8: Audit Log Management
System logs provide an accurate account of all activity on your network. This means that in the event of a cybersecurity incident, proper log management practices will give you all the data you need about the who, what, where, when, and how of the event in question. Security teams must pay attention to logs and use them in conjunction with tools that are designed to analyze log information and generate actionable management guidance.
CIS Control 9: Email and Web Browser Protections
There are more security threats in email and web browsers than phishing alone. Even a single pixel in an email image can give cybercriminals the information they need in order to carry out an attack. Attackers frequently use web browsers and email clients as entry points for code exploitation and social engineering, and controls need to be implemented to protect against interactions with untrusted environments.
CIS Control 10: Malware Defenses
Increasing ransomware attacks necessitate that organizations bolster their malware defenses. Make sure your antivirus tools integrate well with the rest of your security toolchain. Implement anti-malware software and ensure that it is kept regularly updated. This control also involves disabling certain functions, such as autorun and autoplay for removable media.
CIS Control 11: Data Recovery
Organizations must have a strong plan for dealing with the recovery of lost data should preventive controls fail. Are you performing regular, automated backups? Are you protecting your backed-up data? Ensuring proper data recovery capabilities will protect you from threats like ransomware. It’s also important to practice and test restoring your data so you will be prepared in the event of actual data loss.
CIS Control 12: Network Infrastructure Management
Implementing this control will help you reduce your attack surface by way of tactics like automated port scanning and application firewalls. Network devices can be viewed as the gateways to your enterprise, whether physical or virtual. Proper administration and secure configuration of routers, switches, firewalls, and other network devices is essential to managing ingress and egress filtering rules for enterprise policy-based protection.
CIS Control 13: Network Monitoring and Defense
This control involves centralizing security event alerting, deploying host-based intrusion detection systems, using a network intrusion detection system, and more. Network monitoring and defense must be viewed as an ongoing process that is given substantial attention by security teams. Safeguards such as network segmentation and application layer filtering will help ensure that networks stay hardened against attacks.
CIS Control 14: Security Awareness and Skills Training
Security training should be a bigger priority at most organizations, due in part to the widening cybersecurity skills gap. This control also emphasizes the need for ongoing security training rather than one-time engagements. When employees understand how to practice stringent cyber hygiene, they are much harder to exploit by way of phishing and social engineering attacks.
CIS Control 15: Service Provider Management
Most organizations entrust certain processes and functions to third-party service providers who frequently have access to sensitive data. Unfortunately, service providers have become an attack vector for cybercriminals, so managing the security of your organization’s service providers is now a necessity. And this isn’t just for security’s sake; many compliance standards, HIPAA and PCI for example, require compliance to cover third-party service providers.
CIS Control 16: Application Software Security
Code developed in-house needs security assessments through processes like static and dynamic security analysis to uncover hidden vulnerabilities. The most popular target for hackers is your application base, so it’s essential to implement a comprehensive program of application security controls. This should include scanning, testing, and software development lifecycle (SDLC) controls.
CIS Control 17: Incident Response Management
This control helps you put strategies in place to plan and test for cybersecurity incidents so that you’re not left scrambling when they occur. Know who at your organization is responsible for handling incidents and what processes they’ll use to mitigate them. It’s also crucial to conduct post-incident reviews to understand what happened and how to prevent a repeat occurrence.
CIS Control 18: Penetration Testing
Regular penetration testing helps you identify vulnerabilities and attack vectors that would otherwise go unknown until discovered by malicious actors. It’s an important aspect of discovery and identifying potential critical vulnerabilities within your organizations external network, internal network, applications, or systems.
Use Tripwire to Meet the CIS Controls
See how simple and effective security controls can create a framework that helps you protect your organization and data from known cyberattack vectors by downloading this guide here.
The post ” Center for Internet Security (CIS) Controls v8: Your Complete Guide to the Top 18″ appeared first on TripWire
Source:TripWire – Megan Freshley
