5 Lessons Learnt from BJJ that Are Applicable to Cybersecurity

Over the last decade, I have focused quite heavily on technology and the cybersecurity space. I’ve been motivated to create a world that is more inclusive and safer. In 2019, I began a bit of a different journey. Whilst still motivated in a security point of view, this time, I focused on the physical side by beginning to train in Brazilian Jiu-Jitsu (BJJ).
If you’ve never practiced martial arts, what you may be surprised to learn is the value of listening to your body and knowing your own personal limits. Cybersecurity is much the same. Find your strengths, continuously validate your approach and find others who have a different approach to run tabletop exercises with and increase your skills.
In BJJ, you find your preferred approach, and you continuously validate by time spent on the mat training and rolling with a variety of people to test your skills. An added bonus is that the introspection, the increased strength, all play a wonderful role in building your confidence.
One of the best decisions I have made was starting BJJ, and even if it wasn’t the goal from the start, I think there are many lessons we can take from BJJ and apply to our cybersecurity practices:
1. Close the distance: Unskilled, you may believe distancing yourself from an attacker would keep you safe. However, within Brazilian Jiu-Jitsu (BJJ) and self defence, you learn distance is actually the enemy. Closing the gap between you and the attacker is the best way to keep them at bay.
“Defenders Advantage: you are defining the battle field.” @secvalve #2017acsc
— Zoë Rose (@RoseSecOps) March 15, 2017
How do we close the distance and keep ourselves right against malicious actors? Layering! That is, by removing gaps within our infrastructure,with layered controls, implementing the Principle of Least Privilege and adding segmentation to restrict network traversal. We can close the distance a malicious actor has, limit their moves and in some more innovative environments force them to take actions we want to.
It is important to note that sexy new solutions and expensive tools aren’t required to do this. Whilst the most advanced software out there can provide great resources and even reduce investigation time, the reality is if your team is not trained on it or your organization can’t afford the licensing costs or customization time, it’s useless. It is far better to make use of what you have to continuously improve, reduce false positives and negatives.
2. Keep your friends close, but your elbows closer: When rolling or competing against someone, you learn that elbows and arms are vulnerable and can be used against you. This can lead to submissions such as shoulder locks, wrist locks, and armbars.

Don’t let your infrastructure betray you. A great example is the recent publication of CVE-2020-5902, a flaw ddiscovered by security researcher Mikhail Klyuchnikov and privately disclosed to F5. When exploited, the unauthorized malicious actor has access to configuration of the tool, which they can then use to traverse the directory, intercept information and inject both system commands and code. This flaw ultimately received a CVSS score of 10, the highest score a vulnerability can receive. Read what NIST wrote about this vulnerability here.
Maintaining your environment doesn’t just require tailoring the alerts and controls; it also involves monitoring intelligence feeds to ensure these tools aren’t providing malicious actors with a way in. Oftentimes, the biggest defense against this is a robust patch management program. These program include a structured validation and implementation process to ensure that all systems receive regular updates, that firmware is kept up to date, and that testing is done to ensure user workflows aren’t impacted to cause them to find workarounds.
3. Size doesn’t matter: interestingly, the person credited with founding Brazilian Jiu-Jitsu, Mitsuyo Maeda (nicknamed Count Koma, or simply Koma), was in fact of average build, 164 cm and 64 kg. Koma was a prized judo fighter and one of the first mixed martial arts fighter in the modern era. From my personal experience, teachings from Coaches Mariusz Grzywinski, Sergio “Malibu” Jardim, Mickey Musumaci and Caio Terra, I have learned that size thankfully doesn’t matter. What’s most important is the techniques that you use and how you apply them. The most vital part is feeling the opponent’s movements and predicting their steps prior to them taking it – like chess.


Just as size doesn’t matter in BJJ, your security team having an unlimited budget or team members isn’t what protects you. A robust cybersecurity program is how you proportionately and intelligently protect your attack surface from likely threats and scenarios.
For reduced teams and budgets, a hybrid approach to securing and understanding your environment is key. You need to ensure that your in-house team is properly trained and resourced in order to handle the governance for third parties along with to action their responsibilities.
4. When you know how to defend, you know how to attack: Coach Mariusz Grzywinski says his focus wasn’t to attack when he was a white belt. It was to defend, to simply survive. Whilst doing this, he was able to learn and feel the way the opponent reacted to different things, ultimately teaching him areas of weakness and vulnerability that can be exploited.
You know what the attackers processors are, you can exploit this. @secvalve #2017acsc
— Zoë Rose (@RoseSecOps) March 15, 2017
Similar to lesson one, as the defender, you know the system and understand how things are interconnected. By understanding how things work, you will be able to identify gaps, bugs, and bypasses that are available.
“Hacker mindset: looking at something not for what it’s meant to do but what you can make it do for you.”
When Mariusz was defending against attacks until the opponent was tired, he was able to identify weaknesses in the defense and get around them. In your environment, you can continuously improve controls and defenses by finding ways to bypass them. In order to continuously improve, you must have a vulnerability management program in place. This will include automatic tools and scanners but also hands-on validation and investigation as well as a team for receiving reports. When identifying a vulnerability within your environment, use this ‘what can I make it do’ point of view to remediate potential issues before a malicious actor takes advantage of them.
5. Everything in life changes, but jiu-jitsu stays the same: Regardless of the school of training, the coaches you have, even your personal style, the foundations of Brazilian jiu-jitsu remain the same. Reduce the gap, keep your body ready and in check so it cannot betray you, proactively plan for attack and how to defend and put the hours in on the mat.
No matter your situation and resources, the principles of cybersecurity stay the same. Foundations are so vital in order to be the least attractive target.

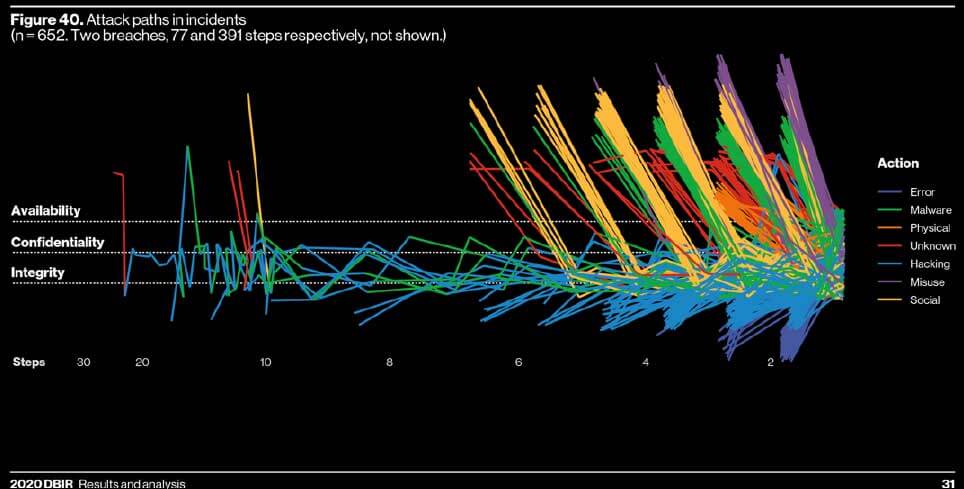
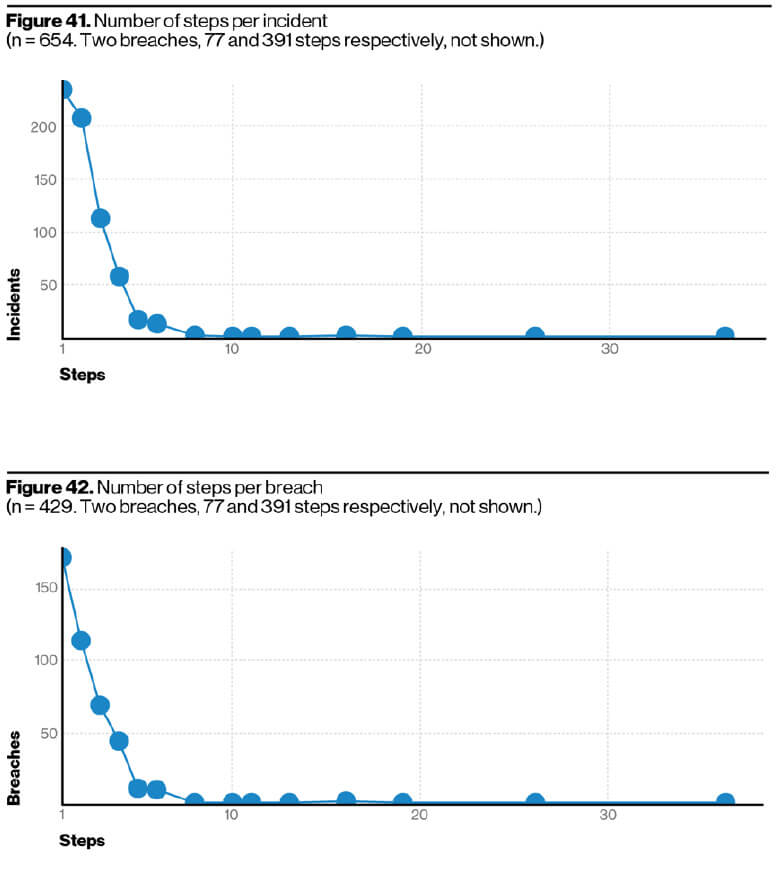
As noted within the Verizon Data Breach Investigations Report 2020, malicious actors seek attacks that are achievable with fewer steps. Therefore, adding additional controls such as multi-factor authentication in the event of stolen credentials goes a long way to reduce your threats. Consider the PoLP or end device firewalls and network segmentation. These are all ways to add barriers in the way of gaining unauthorized access to systems and services.

The post ” 5 Lessons Learnt from BJJ that Are Applicable to Cybersecurity” appeared first on TripWire
Source:TripWire – Zoë Rose
