Secure Your Configurations with Tripwire’s Configuration Manager
As cybersecurity professionals, we are always impressing the importance of patch management as one of the best ways to protect systems against vulnerabilities. Sometimes, the vulnerabilities are never fully exploited. Regardless of the threat possibility, patching is one of the easiest ways to ensure the minimum level of security in an organization. The best part about patching a system is that it is very easy to see the status of the patch level as compared to the manufacturer’s recommendations.
Configuration Management
One of the areas of security that is more easily overlooked is configuration management. If a system’s configuration is changed, it can often go unnoticed, as there are often no alarms that would be set off, no manufacturer’s warning, and no standard level that is recommended. This is why configuration management is so important towards understanding if any configuration drift has occurred. Configuration management is applicable not only to security professionals but also to all areas of IT management as well as to DevOps.
Contextualizing the Problem
According to one source, some organizations have admitted to a large number of known misconfiguration discoveries. More worryingly, some have reported that there are probably unknown misconfigurations, as well. This is the new “low hanging fruit” for cloud-based attacks as well as for malicious techniques like exploiting unsecured storage containers, crypto-jacking, and discovering exposed sensitive databases. That’s probably why Gartner predicted that misconfigurations would account for 80% of cloud breaches by 2020, as reported by Forbes.
Misconfigurations in the cloud are already having an impact, however. We’ve already seen attackers leverage them against big targets like Equifax and Microsoft Azure. We’ve also seen data breaches tied to cloud misconfigurations carry quite a price tag. As reported by TechRepublic, 196 such incidents exposed more than 33 billion records and cost organizations an estimated $5 trillion worldwide in 2018 and 2019.
More Recent Changes
Then came the events of 2020. Over the last year, we have seen a huge spike in ransomware attacks on businesses and government agencies – so much so that there has been an Executive Order directly related to cybersecurity. This Order requires businesses that do business with the government to implement controls that augment their cloud security so that they can better defend against ransomware and other digital threats.
This raises the following question: how can organizations reduce their cloud misconfigurations?
Well, the National Institute of Standards and Technology (NIST) has released guidance that specifically addresses security-focused configuration management. But many organizations don’t have the internal expertise to carry out these recommendations on their own. Fortunately, there’s another way to protect configurations for both on premise and cloud-based environments, and that’s with the use of a configuration management tool.
Where Tripwire Comes In
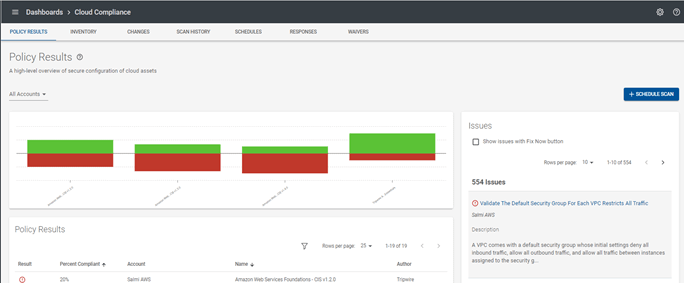
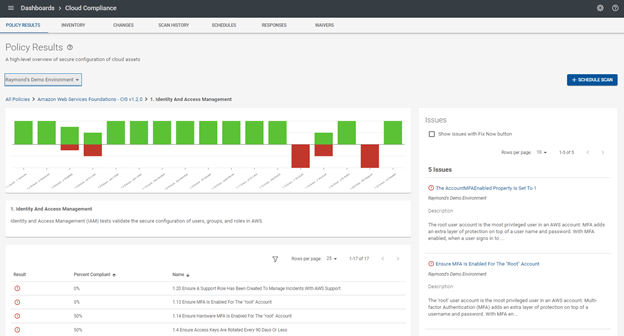
Tripwire Configuration Manager offers an intuitive interface with includes graphical dashboards, which draw attention to key areas of interest, emphasizing focal points that are prioritized based on severity. Configuration Manager is particularly effective because it enables users to monitor their IaaS account configurations against CIS benchmarks. This makes remediation tasks that much easier for system administrators as well as security teams, thus helping to protect from configuration drift.
.

Configuration Manager integrates smoothly with popular third-party applications, adding robust methods to secure your environment. The ability to connect to any third-party SaaS product adds the flexibility to create policies and rules to include their configurations, as well. This helps an organization to gain full visibility and save time and effort by keeping a company’s SaaS application configurations front and center.
Configuration manager prides itself not only on its ease-of-use but also its quick implementation. The “Getting Started” guide points you in all the right directions to attain maximum usability of the product for optimal benefit, from account setup to viewing results and most importantly to remediating issues.
The immediate benefit businesses gain by using Configuration Manager is the ability to have visibility across multiple different cloud environments in one location. With this view, a security team can tackle the most important issues with detailed instructions on how to remediate those issues. The product also includes reports that can be exported and shared through all levels of the C-Level chain and even be used for audit evidence. This provides a perfect summary of your organization’s security posture as well as proof of security readiness.
Careful configuration management is the new focus for many organizations. Unfortunately, it is also the new focus for many cybercriminals. The best way to be sure that your organization is using the best secure configurations is by following reliable guidance and streamlining that process with a trusted tool from a leading security company.
Learn more about Tripwire’s Configuration Manager here. To set up a free trial, click here.
The post ” Secure Your Configurations with Tripwire’s Configuration Manager” appeared first on TripWire
Source:TripWire – Raymond Kirk
