Ransomware Gangs Not Honoring Ransom Payments for Stolen Data

Security researchers observed that multiple ransomware gangs are not honoring the ransom payments received from victims for their stolen data.
In its Quarterly Ransomware Report for Q3 2020, Coveware revealed that almost 50% of crypto-malware cases involved the threat to publish unencrypted data stolen from victims in addition to the use of encryption to render victims’ information inaccessible.
Adding data theft into the mix enables digital attackers to demand two ransoms from its victims: one for the deletion of all stolen information and the other for the receipt of a working decryption key.
However, Coveware revealed in its report that at least five different ransomware gangs weren’t honoring payments received for the former by either doxxing victims after they had paid or asking for an additional ransom payment to prevent the publication of victims’ data.
For instance, the security firm found that REvil, a group which now controls the KPOT infostealer, re-extorted victims for the same data just weeks after they had submitted a ransom payment.
Meanwhile, the attackers responsible for the Netwalker and Mespionza families went ahead and posted the stolen information of their victims despite having received payment to delete that data.
The gang responsible for Conti, crypto-malware which is the likely successor of Ryuk, did something similar in that it showed fake files to victims as proof of deletion. This trick enabled the attackers to publish their victims’ data and/or re-extort them at a later point, if they so chose.
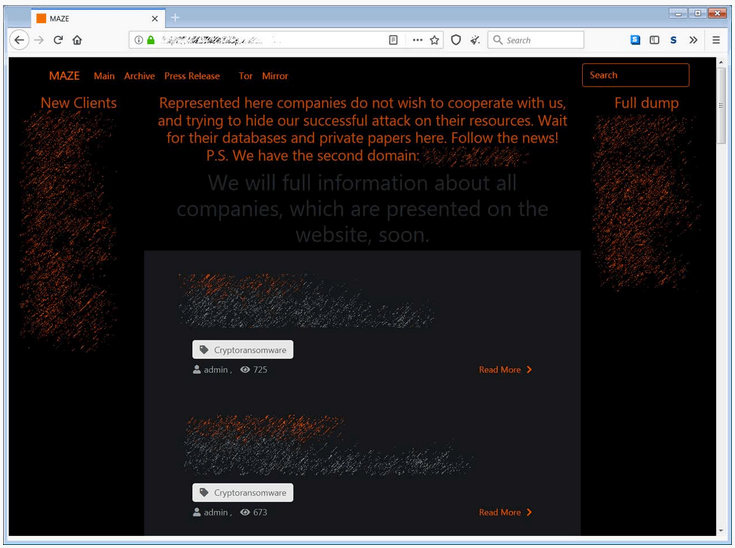
Finally, Maze’s operators published victims’ data either accidentally or willfully on their data leaks site before they even told victims that they had stolen their data.
These betrayals highlight the inherent difficulty of negotiating with ransomware actors, especially over stolen data. As Coveware explained in its report:
Unlike negotiating for a decryption key, negotiating for the suppression of stolen data has no finite end. Once a victim receives a decryption key, it can’t be taken away and does not degrade with time. With stolen data, a threat actor can return for a second payment at any point in the future. The track records are too short and evidence that defaults are selectively occurring is already collecting.
Acknowledging this trend, organizations and users alike should consider directing their focus towards preventing a ransomware infection in the first place. This resource serves as a good starting point.
The post ” Ransomware Gangs Not Honoring Ransom Payments for Stolen Data” appeared first on TripWire
Source:TripWire – David Bisson
