Qlocker ransomware gang shuts shop after extorting owners of QNAP NAS drives

With all the headlines about ransomware attacks hitting companies hard, you might think there’s only bad news around the subject.
Well, think again.
Not only has the Darkside ransomware gang seemingly shut down since the high-profile attack which resulted in the Colonial Pipeline being shut down, and numerous dark web forums announce that they will no longer promote ransomware-as-a-service (RAAS) schemes, but it also appears that another notorious ransomware outfit has decided to close its doors.
Qlocker has made a name for itself – not for attempting to extort millions of dollars from large corporations it has stolen files from – but by targeting the owners of poorly-secured Network Access Storage (NAS) drives.
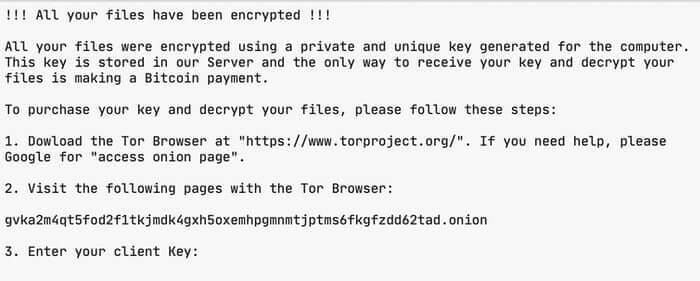
Victims were greeted with a ransom demand for 0.01 Bitcoins (approximately US $400 at current exchange rates) for the recovery of files on their QNAP NAS drives that had been encrypted and placed in password-protected 7zip archives.
On some occasions, it is said that the extortionists would increase the size of the ransom by an additional 0.02 Bitcoin once a victim made contact.
Reports claim that the Qlocker gang successfully made $350,000 in a month from their victims by exploiting a series of security vulnerabilities in QNAP devices. While there is much debate about whether companies are right to pay extortionists millions of dollars for the recovery of their systems, it seems it’s possible to make a tidy criminal profit hitting home users and small businesses for a much smaller amount.
At the end of April, QNAP responded to the threat, warning customers to deploy patches, update their apps, and run a malware scan, following widespread reports that devices had been compromised and user data encrypted by two families of ransomware: Qlocker and eCh0raix.
But in recent days, as Bleeping Computer reports, a message appeared on the Qlocker website saying:
This site will be closed soon.
Sure enough, Qlocker-associated websites have now disappeared – leaving victims no way to pay a ransom.
The reason for the Qlocker gang’s decision to take a step away from its criminal ransomware operation is unclear, but may be related to a general increase in nervousness in the cyberextortion industry since the high profile attack on Colonial Pipeline.
Late last month security researcher Jack Cable described how he had been able to exploit a flaw in the Qlocker ransomware’s infrastructure to trick it into believing victims had already paid a ransom, and unlock files for free.
Unfortunately the ransomware operators later fixed the weakness in its systems, although not before Cable was able to decrypt keys for 50-or-so victims, saving them in total approximately $27,000.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc
The post ” Qlocker ransomware gang shuts shop after extorting owners of QNAP NAS drives” appeared first on TripWire
Source:TripWire – Graham Cluley
