Phishers Using Redirector Sites with Custom Subdomains for Evasion

Malicious actors launched a phishing attack that’s using redirector websites with custom subdomains in order to evade detection.
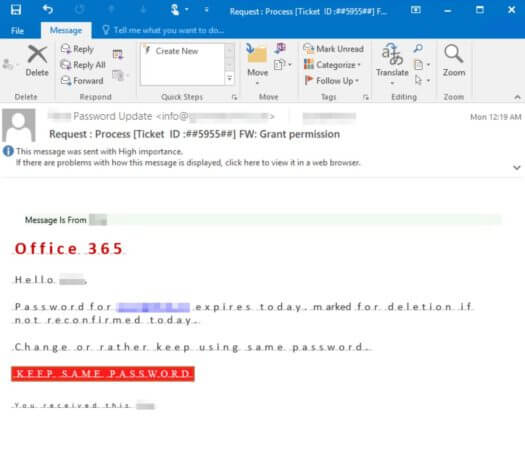
On November 16, Microsoft Security Intelligence tweeted out that it had spotted the phishing attack attempting to lure in recipients with emails disguised as password update reminders, helpdesk tickets and other seemingly legitimate business correspondence.
Microsoft Security Intelligence found that those responsible for the attack were using redirector websites with a custom subdomain for each target.
That subdomain always included the recipient’s username and organization domain name. This information helped to increase the attack’s appearance of legitimacy.
This subdomain naming scheme resulted in the creation of large volumes of phishing URLs, thus improving the chances of the phishers evading detection.
The redirector website URLs also consisted of base domains for compromised websites most of the time along with an extra dot after the Top Level Domain (TLD) and the Base64-encoded version of the recipient’s email address.


In the interest of keeping their activity hidden, the attackers designed their redirector websites so that they’d redirect to a legitimate website if they found that they were being accessed from within a sandbox environment.
Microsoft Security Intelligence summarized the phishing attack’s tactics in this way:
These techniques, in addition to the fact the email message uses heavy obfuscation in its HTML code, make for a sophisticated phishing campaign, exemplifying the increasingly complex email threats that enterprises face today.
The emergence of sophisticated email operations such as the one described above highlights the need for organizations to defend themselves against phishing attacks. They can do this by educating their employees about some of the most common types of phishing attacks that are in circulation today.
The post ” Phishers Using Redirector Sites with Custom Subdomains for Evasion” appeared first on TripWire
Source:TripWire – David Bisson
