O365 Phishing Attack Used Real-Time Validation against Active Directory

A phishing attack used real-time validation against an organization’s Active Directory in order to steal users’ Office 365 credentials.
According to Armorblox, the phishing attack targeted an executive working at an American brand that was named one of the world’s Top 50 most innovative companies for 2019 on a Friday evening.
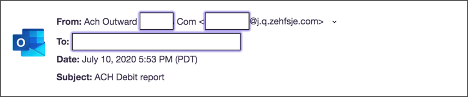
The email used spoofing techniques along with the subject line “ACH Debit Report” to try to trick the recipient into believing that it was an internal final report.
Despite using the recipient’s name, however, the sender address didn’t use an internal email address. Its actual domain was “j[dot]q[dot]zehfsje[dot]com.”
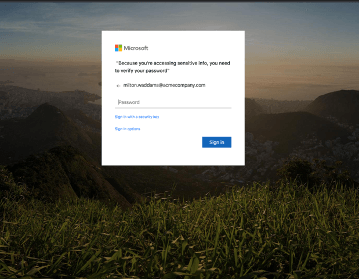
Using all of these techniques, the attack email instructed the recipient to open what appeared to be a text file. Opening the text file from Office 365 in a browser revealed a web page that was identical to Microsoft’s official O365 login page. This imposter portal even had the recipient’s username pre-entered in the corresponding text field.

Armorblox took a closer look at the campaign and found that the attackers had used a customizable toolkit to generate their phishing emails. It also learned that the malicious actors had ultimately used Amazon Simple Email Service (amazonses.com) to send out their emails.
In examining the Office 365 phishing page, the security firm realized that the page had used Office 365 APIs to perform real-time validation of the recipient’s credentials against the organization’s Active Directory. This tactic enabled the malicious actors to receive immediate feedback for the purpose of moving forward with their attack.
Analysis of the phishing page unveiled the international scope of this campaign, as well. As quoted in Armorblox’s research:
The web service behind the credential phishing page is hosted on teenagemoglen[.]com. The domain has been registered at Alibaba.com with a Singapore domain registrar since the end of May 2020. The website is hosted by UnifiedLayer, a hosting company based out of India, at a datacenter in Provo, Utah, United States. The website appears to host web pages copied from another website. None of the links which allow for active engagement with a visitor appear to be active.
At the time of writing, Armorblox had detected 120 visits to the phishing page since the beginning of June. These findings suggest that the attack was targeted in nature and not a “spray-and-pray” campaign.
The campaign described above highlights the need for organizations to defend themselves against phishing attacks. They can do so by educating their users about some of the most common types of phishing campaigns in circulation today.
The post ” O365 Phishing Attack Used Real-Time Validation against Active Directory” appeared first on TripWire
Source:TripWire – David Bisson
