New ‘MontysThree’ Toolset Used in Targeted Industrial Espionage Attacks

Researchers uncovered a new toolset they’ve dubbed “MontysThree” that has played a role in targeted industrial espionage attacks stretching back to 2018.
In the summer of 2020, Kaspersky Lab discovered that an unknown actor had been using a modular C++ toolset called “MT3” to conduct targeted industrial espionage campaigns for years.
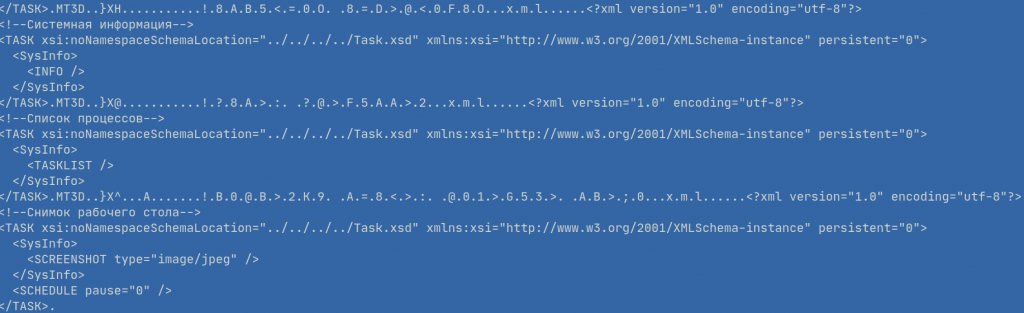
The security firm analyzed MT3, which they nicknamed “MontysThree,” and found that the malware relied on RAR self-extracting archives (SFX) for distribution. Those files commonly contained the names of employees’ phone lists, medical test results and technical specifications.
Ultimately, the SFX archives didn’t use any lures. All they had were PE files disguised as .PDF or .DOC files—a common technique in spear-phishing campaigns.
The researchers found that the threat didn’t break any new ground in its use of a Windows Quick Launch .lnk modifier as its persistence mechanism, in its storage of encryption keys in the same file as well as other techniques and design choices.
Even so, MontysThree stood out to Kaspersky Lab for using a custom steganography method that helped it to evade Intrusion Detection Systems (IDSes). The toolset also abused legitimate cloud services to conceal its command-and-control (C&C) traffic and stored a 3DES key under RSA encryption.
Kaspersky Lab dug a little deeper and found that whoever was responsible for developing the toolset had attempted to misdirect researchers’ attribution efforts. As quoted in the security firm’s research:
MontysThree contains natural language artifacts of proper Russian language and configuration that seek directories that exist only on Cyrilic localised Windows versions. While most external public cloud communications use token-based authorisation, some samples contain email-based accounts for them, which pretend to be a Chinese lookalike. We consider these names to be false flags. Many more artifacts suggest that the malware was developed by a Russian-speaking actor and is targeting Cyrillic Windows versions.
The emergence of toolsets like MontysThree highlight the need for organizations to harden the security of their industrial environments. They can do so by investing in a solution that can help to grant them visibility over their industrial networks, monitor for potential network issues, avoid plant disruptions and detect misconfigured industrial devices. Learn how Tripwire can help.
The post ” New ‘MontysThree’ Toolset Used in Targeted Industrial Espionage Attacks” appeared first on TripWire
Source:TripWire – David Bisson
