New Microsoft Spear-Phishing Attack Uses Exact Domain Spoofing Tactic

Security researchers detected a new spear-phishing attack that’s using an exact domain spoofing tactic in order to impersonate Microsoft.
On December 7, IRONSCALES revealed that it had spotted the campaign targeting Office 365 users. Those users primarily worked in the financial services, healthcare, insurance, manufacturing, utilities and telecom industries.
The email security provider took a deep dive into the campaign and found that it was using an exact domain spoofing technique. This means that the campaign’s attack emails used a fraudulent domain that was an exact match to the spoofed entity’s domain.
For the attack, malicious actors disguised the attack emails so that they appeared to have originated from “Microsoft Outlook” at the email no-reply@microsoft[dot]com.
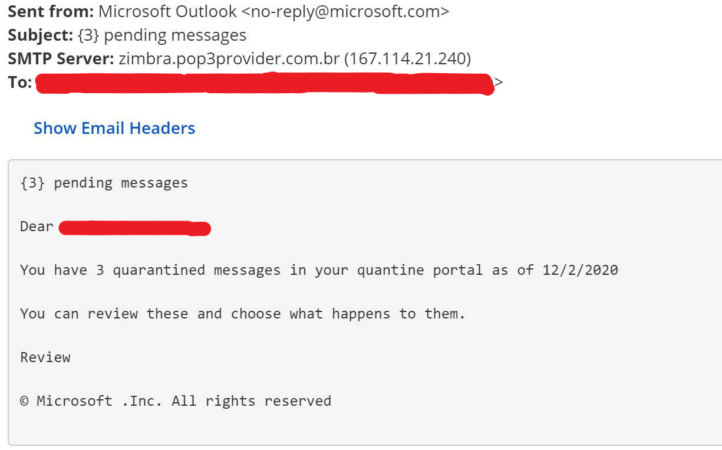
Those emails used the lure of quarantined messages to trick recipients into clicking on a malicious link. If they complied, the campaign redirected the recipients to a fake login page designed to steal their Office 365 credentials.
Notwithstanding their spoofing techniques, the attack emails failed their Sender Policy Framework (SPF) check. This means that the messages were able to bypass the email gateway and land in users’ inboxes.
IRONSCALES investigated this issue and arrived at an explanation. As quoted in its blog post:
Our research found that Microsoft servers are not currently enforcing the DMARC protocol, meaning these exact domain spoofing messages are not being rejected by gateway controls, such as Office 365 EOP and ATP…. It remains unknown as to why Microsoft is allowing a spoof of their very own domain against their own email infrastructure.
News of this campaign highlights the need for organizations to defend themselves against phishing attacks. One of the ways they can do this is by educating their workforce about some of the most common types of phishing attacks and techniques that are in circulation today. This resource is a good place to start.
The post ” New Microsoft Spear-Phishing Attack Uses Exact Domain Spoofing Tactic” appeared first on TripWire
Source:TripWire – David Bisson
