New Mac Ransomware Leveraged Piracy as Means of Distribution

Security researchers detected a new ransomware strain that leveraged piracy as a means of distributing itself to Mac users.
On June 29, a Twitter user reached out to Malwarebytes about a malicious Little Snitch installer that was available for download on a Russian forum known for sharing torrent links.
A close look at the installer revealed that it used a generic icon and arrived within a disk image file. Upon activation, this resource loaded the legitimate installer and uninstaller apps for Little Snitch, a program which alerts users when an app attempts to connect to a web server. The program also installed an executable called “patch” in the /Users/Shared directory.
After a script moved it to a location that appeared to relate to Little Snitch and renamed it “CrashReporter” for the purpose of blending in, “patch” removed itself from the /Users/Shared directory, launched its copy and then launched the Little Snitch installer.
This process didn’t go so well, however. As Malwarebytes explained in its research:
The malware got installed, but the attempt to run the Little Snitch installer got hung up indefinitely, until I eventually forced it to quit. Further, the malware didn’t actually start encrypting anything, despite the fact that I let it run for a while with some decoy documents in position as willing victims.
Further investigation revealed that the threat relied on a malicious installer for DJ software called “Mixed In Key 8.” The malware delivered by that installer was similarly hesitant to get to work, but after Malwarebytes changed the clock setting of its virtual machine, disconnected from the network and restarted the computer a few times, the ransomware finally sprung into action and launched its encryption routine. This process led the threat to encrypt settings files and the keychain files, thus producing error messages and spinning beach balls.
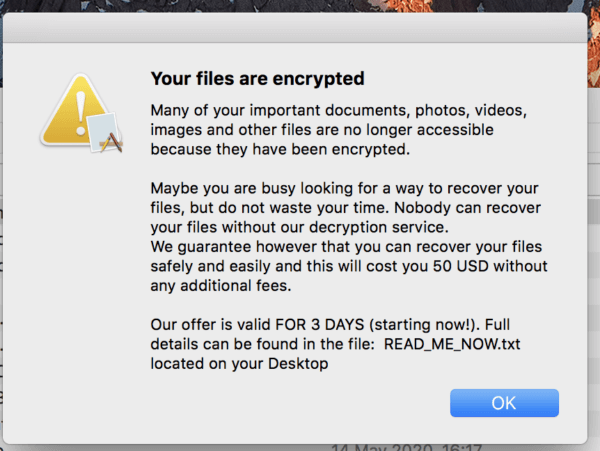
Researchers at the security firm learned from others that the Mac ransomware eventually deployed a ransom note with instructions for payment. Even so, it was unable to replicate this behavior.
This isn’t the first time that researchers have detected ransomware targeting Mac users. Back in 2017, for instance, researchers spotted another crypto-malware strain that relied on cracks to pirate commercial software for distribution. As such, organizations should follow these steps to prevent a ransomware infection from occurring in the first place.
The post ” New Mac Ransomware Leveraged Piracy as Means of Distribution” appeared first on TripWire
Source:TripWire – David Bisson
