Multi-Platform Malware Framework ‘MATA’ Claimed Victims Worldwide

Security researchers discovered a multi-platform malware framework called “MATA” that had succeeded in targeting victims worldwide.
On Securelist, Kaspersky Lab revealed that it had shared its discovery of MATA with its Threat Intelligence Portal customers.
The Russian security firm explained in its analysis that the first artifacts pertaining to MATA emerged back in April 2018. Whoever’s behind the malware framework then used the threat to target enterprises in Poland, Germany, Turkey, Korea, Japan and India.
The targeted organizations operated in several different economic sectors. Among the victims were a software company, an e-commerce business and an Internet Service Provider (ISP).
In these campaigns, the actors responsible for MATA demonstrated that they held various intentions for attacking their victims. With one organization, for instance, the malicious actors used the framework to query the victim’s databases for the sake of acquiring customer lists. With another victim, they used their threat to distribute VHD ransomware.
Kaspersky Lab came across three versions of MATA that targeted either Windows, Linux and macOS.
The Windows version consisted of several components including a loader malware and an orchestrator element. Using a hardcoded hex-string, the loader invoked an encrypted payload. This action paved the way for the orchestrator to load plugin files and execute them from memory. Those plugins gave attackers the ability to manipulate files, create an HTTP proxy server and perform other tasks.
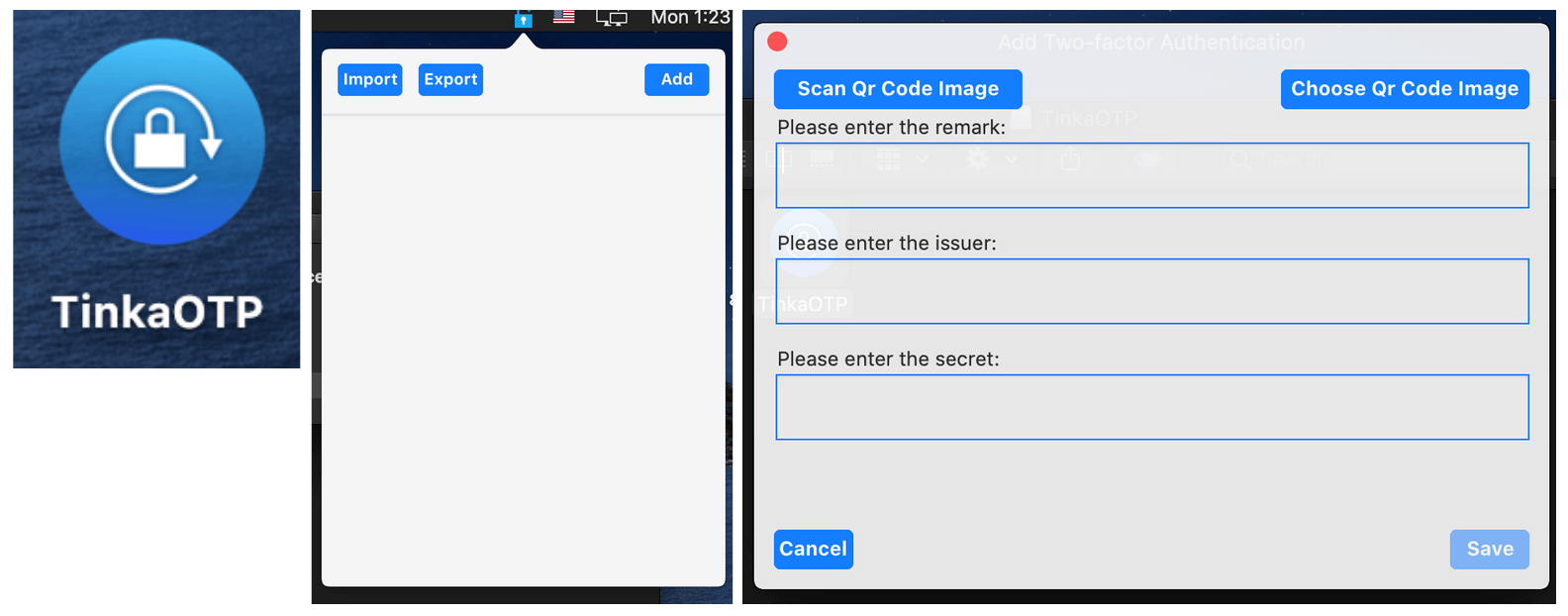
The Linux version of MATA was available on a legitimate distribution site, while the macOS variant arrived as a trojanized two-factor authentication (2FA) application.
In its analysis, Kaspersky Lab attributed the malware platform to a well-known threat actor:
We assess that the MATA framework is linked to the Lazarus APT group. The MATA orchestrator uses two unique filenames, c_2910.cls and k_3872.cls, which have only previously been seen in several Manuscrypt variants, including the samples (0137f688436c468d43b3e50878ec1a1f) mentioned in the US-CERT publication.
The security firm revealed that a variant of Manuscrypt, a malware family distributed by Lazarus, also shared a similar configuration structure with MATA.
Kaspersky Lab said it would continue to monitor the malware platform as it evolves.
The post ” Multi-Platform Malware Framework ‘MATA’ Claimed Victims Worldwide” appeared first on TripWire
Source:TripWire – David Bisson
