Lucifer Malware Abused Windows Exploits for Cryptomining, DDoS Attacks

New malware called “Lucifer” came with numerous exploits for conducting cryptomining functionality and performing distributed denial-of-service (DDoS) attacks on infected Windows machines.
Palo Alto Networks’ Unit 42 research team identified two versions of Lucifer in their research. (Both variants bore the name “Satan DDoS,” but for the sake of not confusing this threat with the Satan Ransomware-as-a-Service (RaaS) platform, Unit 42 decided to call the malware “Lucifer.”)
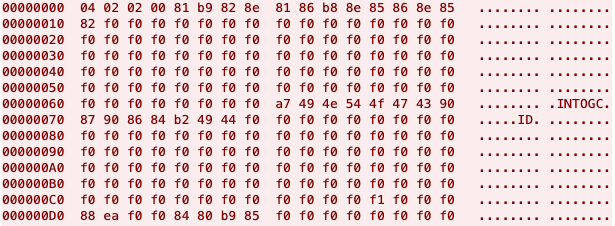
The first version of the malware acted upon successful execution by decrypting its command-and-control (C&C) IP address and using that information to create a mutant object. It then leveraged registry keys and scheduled tasks to establish persistence before reviewing whether any other cryptomining data was stored in a registry key. At that point, Lucifer enabled the debug privilege and used several threads to deploy its cryptomining binary.
Lucifer arrived with several propagation methods. Unit 42 witnessed the malware leveraging brute force techniques in the event that it spotted TCP port 1433 open on a target, for instance. The threat also arrived with the ability to abuse several well-known exploits, as the researchers explained in a blog post:
In addition to brute-forcing the credentials, the malware leverages exploitation for self-propagation. For intranet infection, it drops and runs EternalBlue, EternalRomance, and DoublePulsar backdoor against the target when the target has TCP port 445 (SMB) open. Upon successful exploitation, certutil is used to propagate the malware.
After launching its worker threads, Lucifer launched into infinite loop so as to remain in contact with its C&C server. This connected enabled the malware to receive instructions for the purpose of managing its miner’s functionality and for conducting a DDoS attack.
The second version of Lucifer wasn’t too dissimilar from the first variant spotted by Unit 42. However, it did stand out for the addition of anti-sandbox capabilities and an anti-debugger technique along with changes made to the list of exploits included in its arsenal.
Both variants of Lucifer highlight the need for organizations to ensure that their systems are up-to-date wherever possible. They can do this by creating a robust vulnerability management program. Some best practices for doing so are available here.
The post ” Lucifer Malware Abused Windows Exploits for Cryptomining, DDoS Attacks” appeared first on TripWire
Source:TripWire – David Bisson
