Lockdown Mode: Apple to protect users from targeted spyware attacks
Apple has previewed a new feature which aims to harden high-risk users from the serious threat of being spied upon by enemy states and intelligence agencies.
“Lockdown Mode” is scheduled to arrive later this year with the release of Apple iOS 16 and macOS Ventura. It’s an optional feature for users who believe their computers and smartphones face a real risk of being targeted by sophisticated state-sponsored spyware.
Apple acknowledges that its protection technology is “extreme,” and is not something that is ever likely to be required by anyone other than a tiny percentage of their customers.
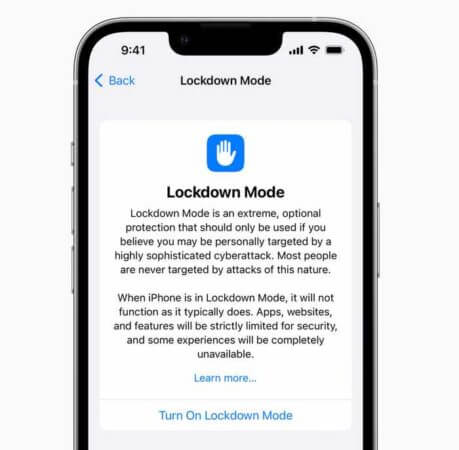
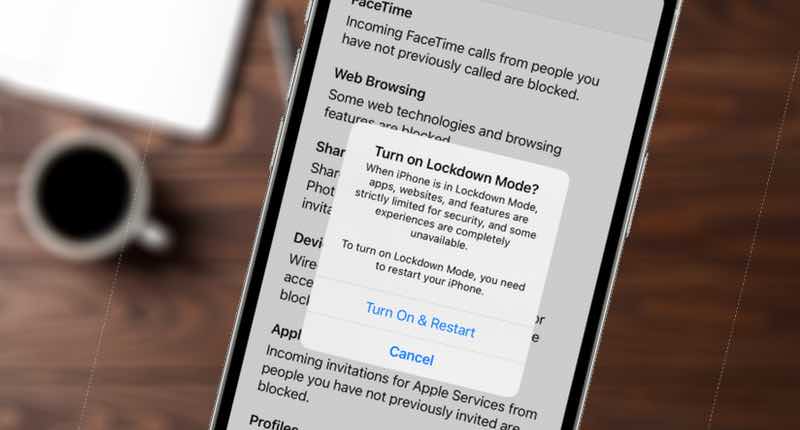
“When iPhone is in Lockdown Mode, it will not function as it typically does. Apps, websites, and features will be strictly limited for security, and some experiences will be completely unavailable.”
“While the vast majority of users will never be the victims of highly targeted cyberattacks, we will work tirelessly to protect the small number of users who are,” said Ivan Krstić, Apple’s head of Security Engineering and Architecture. “That includes continuing to design defenses specifically for these users, as well as supporting researchers and organizations around the world doing critically important work in exposing mercenary companies that create these digital attacks.”
Although the number of political activists, lawyers, journalists, and diplomats who may be at risk of being targeted by mercenary spyware may be very small, the impact of them being hacked may have grave consequences.
In its announcement, Apple practically acknowledges that enabling “Lockdown Mode” will severely limit your device’s functionality in various ways – but with the benefit of reducing the attack surface, limiting the potential for targeted spyware to exploit your phone or computer.
According to Apple, at launch “Lockdown Mode” will restrict devices as follows:
- Messages: Most message attachment types other than images are blocked. Some features, like link previews, are disabled.
- Web browsing: Certain complex web technologies, like just-in-time (JIT) JavaScript compilation, are disabled unless the user excludes a trusted site from Lockdown Mode.
- Apple services: Incoming invitations and service requests, including FaceTime calls, are blocked if the user has not previously sent the initiator a call or request.
- Wired connections with a computer or accessory are blocked when iPhone is locked.
- Configuration profiles cannot be installed, and the device cannot enroll into mobile device management (MDM), while Lockdown Mode is turned on.
Apple says that it will continue to strengthen “Lockdown Mode”, and is offering a bug bounty of up to $2,000,000 to researchers who can find a way to bypass its security.
In addition, Apple says it is making a $10 million grant available (in addition to any damages awarded from the lawsuit filed against the controversial Israeli spyware company NSO Group) to support organisations that investigate, expose, and prevent highly targeted attacks.
All eyes now turn to Google, to see whether it will roll out similar optional security features to Android users who may be at similar risk to their iPhone-loving cousins.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” Lockdown Mode: Apple to protect users from targeted spyware attacks” appeared first on TripWire
Source:TripWire – Graham Cluley
