Hacker Tools Used for Good as Exposed Amazon Cloud Storage Accounts Get Warnings

Responding to the all too familiar news of compromised Amazon cloud storage, security researchers have begun leaving “friendly warnings” on AWS S3 accounts with exposed data or incorrect permissions.
The misconfiguration of access control on AWS storage “buckets” has been behind numerous high profile data breaches, including Verizon, The Pentagon, Uber and FedEx.
Researchers have begun taking security notification into their own hands, with security advice left behind on publicly accessible storage.
These warning messages come in multiple forms from multiple sources, pointing to a plethora of interested parties performing these white hat notifications.
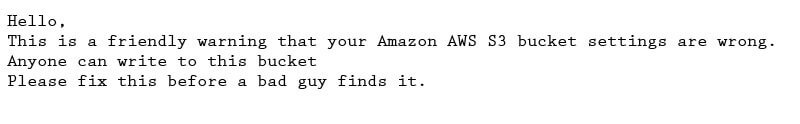
The messages range from the simple “Please fix this before a bad guy finds it” to more complex warnings about the consequences of exposed cloud storage:
Use of Amazon S3 for cloud storage has exploded in recent years as more and more organizations migrate to the cloud. The ease of purchase and use lends itself to quick projects that can often be left unmonitored after project completion.
This, combined with the complex nature of S3 access control, has led to many unused buckets being left forgotten and exposed.
Tools such as BuckHacker and AWSBucketDump make it easy for attackers to scan the AWS S3 storage service for publicly exposed data, and now those same tools are being used by security researchers in a defensive capacity.
By first using these tools to find exposed cloud storage accounts, defenders then upload files containing messages of warning and advice on security.
It is vital that you perform a check-up of your cloud security posture, doubly so if you see warnings or other suspicious behavior in your cloud accounts.
Tripwire has multiple tools to help secure your cloud infrastructure, from cloud storage monitoring to vulnerability management and breach detection in your cloud computing resources.
Tripwire Configuration Manager can be used to automatically assess your AWS S3 buckets to determine if they are exposed to anonymous access and even perform automatic remediation and enforcement on buckets that have become newly exposed as might happen with accidental changes to access permissions.
Since you can’t possibly know everything and be everywhere (any more than you already do), let Tripwire® Configuration Manager automate your cloud security. Test drive it with your own cloud accounts or use our sample data to see what simplified cloud monitoring looks like in action.
Learn more here: https://www.tripwire.com/products/tripwire-configuration-manager/worry-less-about-cloud-security
The post ” Hacker Tools Used for Good as Exposed Amazon Cloud Storage Accounts Get Warnings” appeared first on TripWire
Source:TripWire – Ben Layer
