Google App Engine, Azure App Service Abused in Phishing Campaign

A phishing campaign abused both the Google App Engine and the Azure App Service to steal victims’ Microsoft Outlook credentials.
Netskope observed that the attack campaign started with a shortened link “https://bitly[.]com/33nMLkZ” distributed by a phishing email. This link redirected a recipient of the email to a Google App Engine domain “https://o365apps[.]oa.r.appspot.com.”
A Google Cloud Platform (GCP) service used for developing and hosting web applications, Google App Engine enables customers to direct SSL-protected traffic through their appspot.com domain.
This characteristic thereby lent the domain used in this campaign a sense of legitimacy.
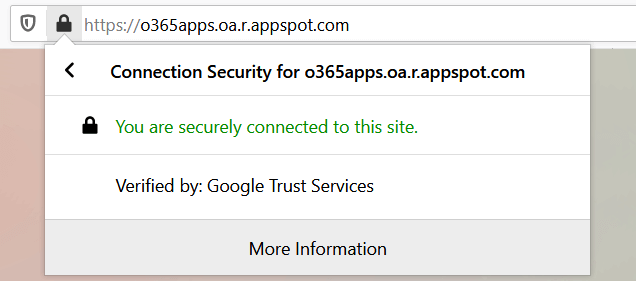
At the time of Netskope’s analysis, https://o365apps[.]oa.r.appspot.com served as the location for a phishing page that prompted visitors to submit their Microsoft Outlook credentials.
The phishing page informed the visitor that their account credentials were incorrect after they had submitted their username and password. It then sent those details to ‘handler.php,’ a page hosted via Azure’s App Service at “july-28[.].azurewebsites[.]net.”
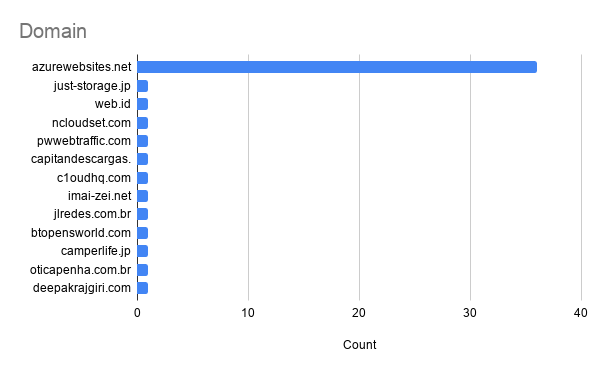
This domain was one of 110 bait URLs and 72 credential hosting URLs that traced back to this phishing campaign. As noted by Netskope, however, the vast majority of those sites used Azure’s App Service:
…[T]he threat actor has mostly used Azure App Service to host the credential harvester at azurewebistes.net. It appears the attacker tried out multiple different options to serve the credential harvester and chose to use Azure App Service on an ongoing basis, likely because of its ease of use and Microsoft-issued SSL certs.

The campaign described above highlights the need for organizations to defend themselves against a phishing attack. One of the ways they can do this is by training their employees to spot some of the most common types of phishing campaigns that are in circulation today. They can use this resource to lay the basis for their education efforts.
The post ” Google App Engine, Azure App Service Abused in Phishing Campaign” appeared first on TripWire
Source:TripWire – David Bisson
