Gift Cards Requested in Two-Thirds of BEC Attacks, Report Reveals

A report revealed that scammers requested funds in the form of gift cards in two-thirds of business email compromise (BEC) attacks.
For a phishing trends report from the Anti-Phishing Working Group (APWG), APWG member Agari examined thousands of BEC attacks that occurred in the second half of 2020. It found that 66% of them involved gift cards. By contrast, direct bank transfers factored in just 18% of attacks, followed close behind by payroll diversions at 16%.
The amount of money requested by scammers varied according to these means of attack. Agari discovered that the average BEC wire transfer attempt was $80,183–up from $54,000 the previous quarter. By contrast, scammers requested an average of $1,213 in attacks involving gift cards. That was down from about $1,453 in the first quarter of the year.
APWG feels that these smaller asks in the form of gift cards might have benefited scammers. As it explained in its report:
Scam attempts around this dollar amount may have a decent chance of success, because they can be approved by multiple people in a medium-to-large company, and the amount is small enough to slip by some companies’ financial controls. Gift cards for eBay, Google Play, Apple iTunes, and Steam Walletmade up 70percentof gift card requests in the second quarter.
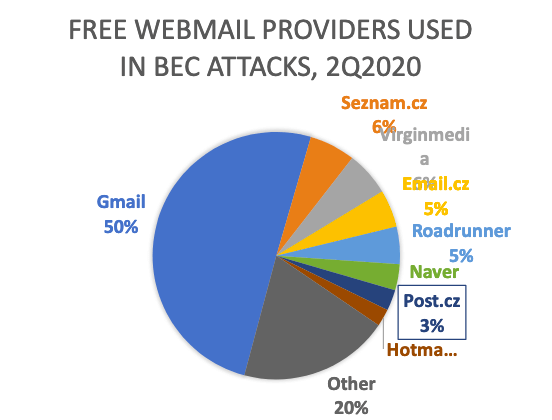
Agari found that 72% of BEC attacks sent in Q2 2020 emanated from free webmail attacks. (That was up from 61% the previous quarter.) Half of those attacks came from Gmail accounts.
These findings arrive approximately one year after the Federal Bureau of Investigation (FBI) revealed that BEC scams cost victims a combined total of $26 billion in losses over a three-year period.
The report from APWG serves as a reminder for organizations to strengthen their defenses against a BEC attack. One of the ways they can do this is by educating their employees about some of the most common phishing attacks that are in circulation today.
The post ” Gift Cards Requested in Two-Thirds of BEC Attacks, Report Reveals” appeared first on TripWire
Source:TripWire – David Bisson
