FluBot malware warning after 70,000 attacks launched over SMS

Finland’s National Cyber Security Centre (NCSC-FI) has issued a warning about malicious SMS messages that have been spammed out to mobile users, directing iPhone owners to phishing sites and Android users to download malware.
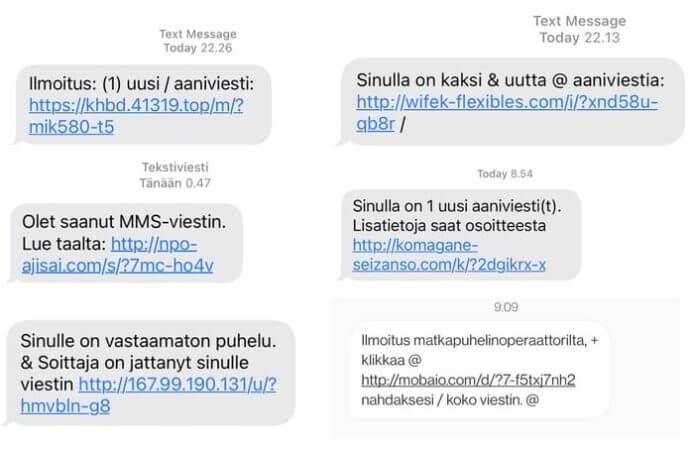
The messages are written in Finnish but without the customary accented characters. In some instances, the messages pose as a notification that the user has received a voicemail message, or a communication from their mobile network provider.
Fortunately, clicking on the link contained within the message does not automatically initiate an automatic download for recipients using Android devices, but instead requires user confirmation that they wish to install a program.
According to an alert issued by NCSC-FI, which saw approximately 70,000 SMS messages sent by hackers in just 24 hours, victims have found their Android devices infected with the FluBot malware.
Of course, non-Finnish speakers will likely be instantly suspicious if they receive a message written in a language they understand. But there is nothing to stop hackers from altering the campaign to target users of other languages.
In the past cybercriminals have distributed FluBot via bogus messages that claim to help intended victims track parcel deliveries or listen to a voicemail message, or via web pages that claim a user’s Android device has been infected with malware, and that they should urgently install a security update.


Of course, following the instructions and installing the security update actually infects devices.
Once in place, FluBot is capable of stealing banking credentials, payment details, text messages, and contact information from victims’ devices.
Users who have already infected their devices with FluBot are advised by NCSC-FI to perform a factory reset and restore from a backup that was created before the malware infection took place.
Last week Netcraft reported that criminals have compromised legitimate websites running vulnerable WordPress plugins and themes to upload their malicious content.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” FluBot malware warning after 70,000 attacks launched over SMS” appeared first on TripWire
Source:TripWire – Graham Cluley
