Extortionists Preying on Site Owners with Fake Website Hacking Scam

Researchers found that extortionists are targeting website owners with a scam in which they claim to have hacked their site and extracted a database.
WebARX observed that the ploy first makes itself known to website owners when they receive a ransom message from the attackers.
In a sample note analyzed by the web application security platform, the scammers claimed that they compromised the recipient’s website and extracted the site’s database. They then told the recipient that they intended to either leak the site’s data online or sell it in an auction unless they received a ransom payment from their victims. That ransom demand ranged in amount from 1500 USD and 3000 USD.
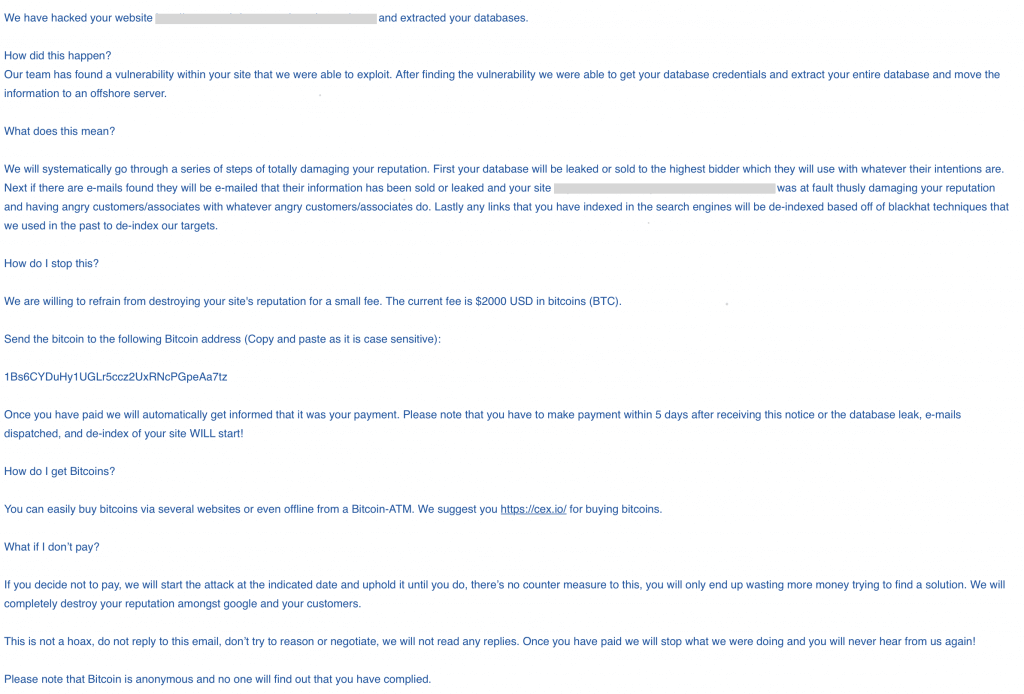
The attackers went on to threaten their use of black-hat SEO techniques to ruin non-compliant recipients’ website rankings.
Those responsible for penning the ransom note discussed above did not offer any proof to support their claims. That’s because they did not have any. The attack which they described never occurred; they were merely using recipients’ fear against them in an attempt to trick them into paying.
Given this observation, WebARX recommended that website owners resist reacting out of fear and instead ask themselves some questions to figure out if a threat made by extortionists is legitimate. As the platform explained its research:
Ask yourself, is there any proof of these claims? Does that email contain any information that could indicate that the website is compromised and that the database breached? What kind of information is there in the database? Does it even have a database? Critical questions as such often give you a quick reality check if this is something you should worry about.
Website site owners should also take additional steps to protect themselves against a malware infection, a distributed denial-of-service (DDoS) campaign and other common digital threats. This resource is a great place to start.
The post ” Extortionists Preying on Site Owners with Fake Website Hacking Scam” appeared first on TripWire
Source:TripWire – David Bisson
