Cryptocurrency exchange Eterbase hacked, $5.4 million worth of funds stolen

European cryptocurrency exchange platform Eterbase has announced that it has suffered a security breach which saw malicious hackers access its network and steal funds worth US $5.4 million.
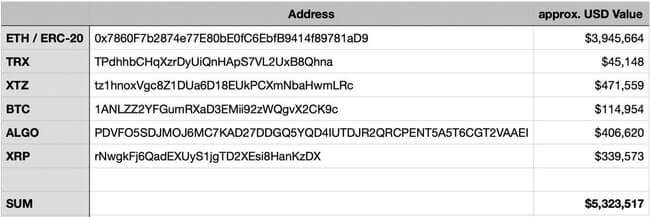
In a message posted on Telegram, the Slovakian cryptocurrency exchange listed the six hot wallets plundered by cybercriminals for their Ether, Tezos, Bitcoin, ALGO, Ripple, and TRON riches.
The majority of the cryptocurrency funds stolen from the hot wallets were in the form of Ether, making up almost $3.9 million of the almost $5.4 million stolen.
Eterbase put its exchange into “maintenance mode” following the security breach, and reported the attack to law enforcement. The cryptocurrency exchange says that it is co-operating with investigators, and “wants to assure our clients that we are taking all necessary steps to ensure that the amount of their deposit does not suffer any damage as a result of a hacker attack.”
In a tweet, Eterbase said that it had tracked the movement of stolen funds as they were transferred into rival exchanges including Binance, HitBTC, and Huobi, and requested their co-operation in freezing funds to thwart any attempts by the criminals to cash out their loot.
A hot wallet is a cryptocurrency wallet that is connected to the internet. A user entrusts responsibility of managing the private and public keys of their cryptocurrency hot wallet to an online platform, rather than looking after it themselves.
This means that hot wallets are relatively easy to set up and convenient to access – but, of course, that ease of access also means that there is an increased risk that online criminals will also be able to hack into the platform and steal a wallet’s contents.
The majority of known cryptocurrency hacks have involved stealing funds from hot wallets.
Cold wallets, meanwhile, are not connected to the internet. They may come in the form of a hardware device which is only plugged in when a transaction needs to take place. It’s more of a pfaff accessing your cryptocurrency fortune when you want to withdraw funds, trade, or make a payment, but it’s inherently more secure.
My advice? If you have a not-insignificant amount of cryptocurrency you would be much wiser to keep it offline in a cold wallet than risk leaving it online in a hot wallet which might one day be breached by hackers.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” Cryptocurrency exchange Eterbase hacked, $5.4 million worth of funds stolen” appeared first on TripWire
Source:TripWire – Graham Cluley
