CLOP ransomware suspects charged by police in Ukraine

Six people alleged to be part of the notorious CLOP ransomware gang have been detained and charged by Ukrainian police, following nearly two dozen raids across the country.
According to a statement released by the Ukraine’s cyber police, the hacking group is thought to have inflicted $500 million worth of damage on universities and organisations it exfiltrated data from and infected with ransomware.
The arrests are said to be connected to ransomware attacks that took place against organisations in the United States and South Korea, with law enforcement officers from both countries assisting in the investigation.
The attackers are thought to have used Cobalt Strike, a penetration testing tool which has become beloved by malicious hackers as a means of compromising organisations.
“Using remote access, the suspects activated malicious software ‘Cobalt Strike’, which provided information about the vulnerabilities of infected servers for further capture.”
Back in November 2020, a South Korean retailer was threatened by the CLOP ransomware gang which said it would release the payment card details of some two million customers if a Bitcoin ransom worth $40 million was not paid.
Some of this week’s arrests were recorded on video by police, showing armed officers raiding the suspects’ properties, seizing luxury vehicles, gathering computers and smartphones for forensic analysis, and counting large sums of money.
Obviously it’s good to see international law enforcement agencies working together to identify suspected members of a ransomware gang, and bring them to justice. If found guilty, those arrested could face up to eight years in prison.
But if you think that this might signal the end of the CLOP ransomware gang, then I fear I may have to dampen your hopes.
Those arrested in Ukraine do not appear to have been the masterminds of the group, but rather members of the gang who were engaged in the cashing-out and money-laundering side of the criminal enterprise.
Experts at Intel471 told journalists that they “did not believe that any core actors behind CLOP were apprehended, due to the fact they are probably living in Russia.”
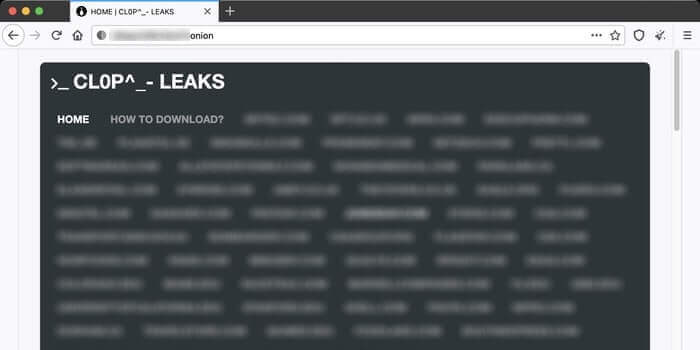
Meanwhile, CLOP’s website – where it publicises a list of past victims and shares terabytes of data files it has stolen from victims who refused to pay a ransom – remains online on the dark web.
Whether CLOP operatives further up the food chain will be apprehended in the future remains, for now, uncertain and may require a greater level of international co-operation than has been seen to date.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” CLOP ransomware suspects charged by police in Ukraine” appeared first on TripWire
Source:TripWire – Graham Cluley
