BlackRock Android Banking Malware Targeting 337 Mobile Apps

Security researchers discovered a new Android banking malware family called “BlackRock” that targets 337 mobile applications.
ThreatFabric found that BlackRock hid its icon when it first launched itself on a mobile device. It then posed as a Google update in an attempt to gain access to a user’s Accessibility Service. Once it received access to these privileges, the malware granted itself additional permissions that enabled it to communicate with its command-and-control (C&C) server and to perform overlay attacks.
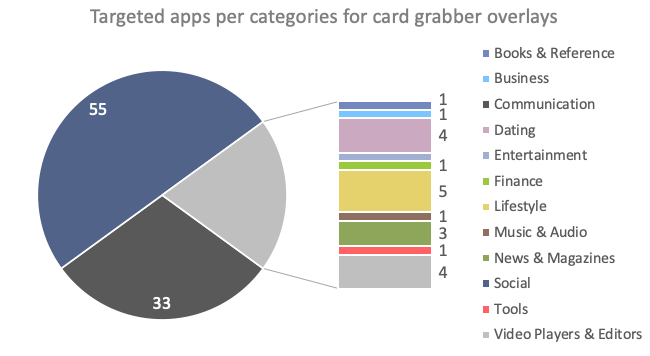
At this stage in its infection chain, BlackRock checked to see which app was running in the foreground on the infected device. The Android malware then had the option of deploying one of two types of overlays: a generic credit card grabber or an overlay that specifically mimicked one of 337 applications that appeared on the threat’s target lists.
In analyzing BlackRock’s target list, ThreatFabric found that the majority of apps related to banking operations in Europe followed by Australia, the United States and then Canada. Even so, the security firm found that the banking malware also went after social, communication, lifestyle and even dating programs.
As it explained in its research:
Most of the trending social and dating apps are included, the actors’ choice might have been driven by the pandemic situation, pushing people to socialized more online. It also seems that actors have made a particular effort on including dating apps, which wasn’t something common in targets list so far.
According to ThreatFabric’s analysis, BlackRock arrived as the latest attempt by malicious actors to revive LokiBot. This threat first appeared on the threat landscape in 2016 and 2017 with various attack campaigns, including one in which it deployed ransomware if a user attempted to remove it. LokiBot died down after its source code appeared online, though it was involved in some attack operations as recently as May 2019.
The emergence of BlackRock highlights the need for organizations to defend themselves against mobile banking malware by downloading apps only from trusted developers on official app marketplaces, keeping an eye out for apps that require excessive permissions and protecting their banking accounts with some form of multi-factor authentication.
The post ” BlackRock Android Banking Malware Targeting 337 Mobile Apps” appeared first on TripWire
Source:TripWire – David Bisson
