Australia Proposes Security Law to Protect Critical Infrastructure Against Cyber Attacks

The Australian Government is committed to protecting the essential services all Australians rely on by uplifting the security and resilience of critical infrastructure.
Increasingly interconnected and interdependent critical infrastructure is delivering efficiencies and economic benefits to operations. However, connectivity without proper safeguards creates vulnerabilities that can deliberately or inadvertently cause disruption resulting in cascading consequences across national economies, affecting their security and sovereignty.
The Australian Department of Home Affairs proposed national security laws in a consultation paper aimed at industry, academia and state and territory governments. The consultation period is expected to run until September 16.
The proposed laws will grant federal government agencies the power to “take direct action” against cyber-attacks and obtain information from critical infrastructure entities if it is deemed to be in the national interest.
New definition of critical infrastructure
The Australian’s Government Security of Critical Infrastructure Act 2018 defines as critical infrastructure those entities or facilities “which if destroyed, degraded or rendered unavailable for an extended period, would significantly impact on the social or economic wellbeing of the nation, or affect Australia’s ability to conduct national defense and ensure national security.”
Within that broad definition of critical infrastructure, the Act currently places regulatory obligations on specific entities in the electricity, gas, water and maritime ports sectors. However, entities across all critical infrastructure sectors are facing increasing threats and may require enhanced protections.
The reforms outlined in the paper would include a number of additional sectors to the definition of critical infrastructure: banking, finance, communications, data, the Cloud, defense industry, education, research, innovation, energy, food, grocery, health, space, transport and water.
Objective of the proposed framework
The primary objective of the proposed framework is to protect Australia’s critical infrastructure from all hazards and impacts of catastrophic cyber-attacks. The enhanced framework outlines a need for an uplift in cyber security and resilience in all critical infrastructure sectors, combined with better identification and sharing of threats. The goal is to make Australia’s critical infrastructure – whether private or state owned and operated – more resilient and secure.
Elements of the proposed framework
The proposed security law is comprised of three elements:
- Positive Security Obligation, which includes baseline protections against all hazards for critical infrastructure and systems, implemented through sector-specific standards proportionate to risk.
- Enhanced Cyber Security Obligations that establish the ability for Government to request information to contribute to a near real-time national threat, owner and operator participation in preparatory activities with the Government as well as the co-development of a scenario based ‘playbook’ that sets out response arrangements.
- Government Assistance for entities that are the target or victim of a cyber-attack through the establishment of a Government capability and authorities to disrupt and respond to threats in an emergency.
These three initiatives will be underpinned by an enhanced Government-industry partnership.
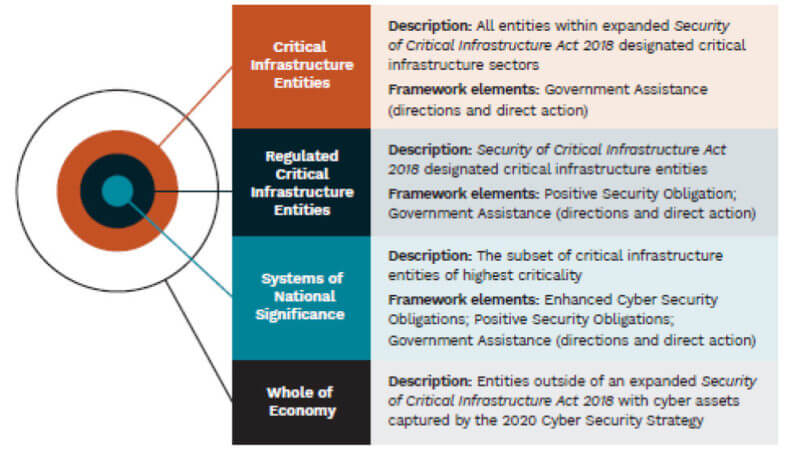
Categorization of covered entities
Entities covered under the proposal would be categorized as either a “critical infrastructure asset,” a “regulated critical infrastructure asset” or “systems of national significance.” The image below maps these categories with the elements of the proposed framework.
“Direct action to protect critical infrastructure”
The government has proposed the development of a national alerting system for cyber-attacks for situations where it may “declare an emergency.” To elevate an incident into an emergency, the Government would consider factors such as the potential consequence to Australia’s economy, security or sovereignty, the extent to which the incident would spread across jurisdictions and the imminence of the threat.
However, the consultation paper takes one step further. In cases when a cyber-attack is determined as “an immediate and serious cyber threat to Australia’s economy, security or sovereignty (including threat to life),” it is proposed that the government be granted the power to “take direct action to protect a critical infrastructure entity or system in the national interest.” The primary purpose of these powers would be to allow the Australian government “to assist entities take technical action to defend and protect their networks and systems, and provide advice on mitigating damage, restoring services and remediation.”
The proposal also says that critical infrastructure operators must not be allowed to hack back but should “be empowered to take necessary, preventative and mitigating action against significant threats.” Under such circumstances, critical infrastructure operators should be given “appropriate immunities to ensure they are not limited by concerns of legal redress for simply protecting their business and the community.”
Information sharing
Finally, to develop better situational awareness, the Australian government plans to facilitate information sharing with the owners and operators of “systems of national significance.” The information shared will be about networks and systems, “not information about consumers.” Under the proposed laws, the government would be able to ask entities for their information on a voluntary basis “in the first instance,” but eventually entities would be forced to provide their information especially if they are determined as “systems of national significance.”
“In the longer term, owners and operators of systems of national significance will be obligated (under amendments to the Act) to provide information about networks and systems to contribute to this threat picture if requested,” the paper says.
Final thoughts
The consultation paper, which is aligned with Australia’s 2020 Cyber Security Strategy, intends to make Australian critical infrastructure entities act proactively, rather than being reactive, to address the expanded threat landscape. A strong proactive mentality like this can be a win-win case. The biggest challenge is to cement a working relationship between the industries and the Australian government based on mutually accepted risks of discovered vulnerabilities to eliminate false positives and establish trust.
The post ” Australia Proposes Security Law to Protect Critical Infrastructure Against Cyber Attacks” appeared first on TripWire
