Attackers Targeted Dozens of U.S. Companies with WastedLocker

Security researchers identified a string of attacks in which malicious actors attempted to target dozens of U.S. organizations with WastedLocker ransomware.
Symantec detected the attack attempts on several of its customers’ networks. As part of this discovery, the security firm realized that the threat behavior it was observing coincided with research published by NCC Group on WastedLocker, a new crypto-ransomware family attributed to Evil Corp.
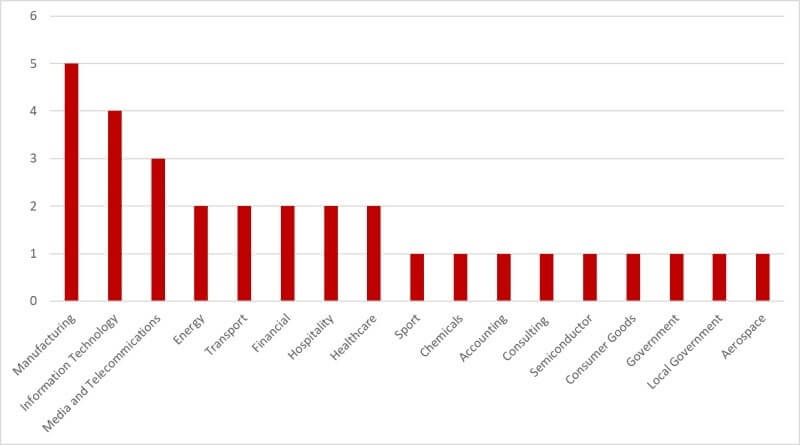
This revelation led Symantec to identify attacks at least 31 U.S. organizations. Of those, 11 were listed companies, and eight were Fortune 500 companies. The affected organizations also spanned across multiple sectors including manufacturing, accounting, IT and media/telecommunications.
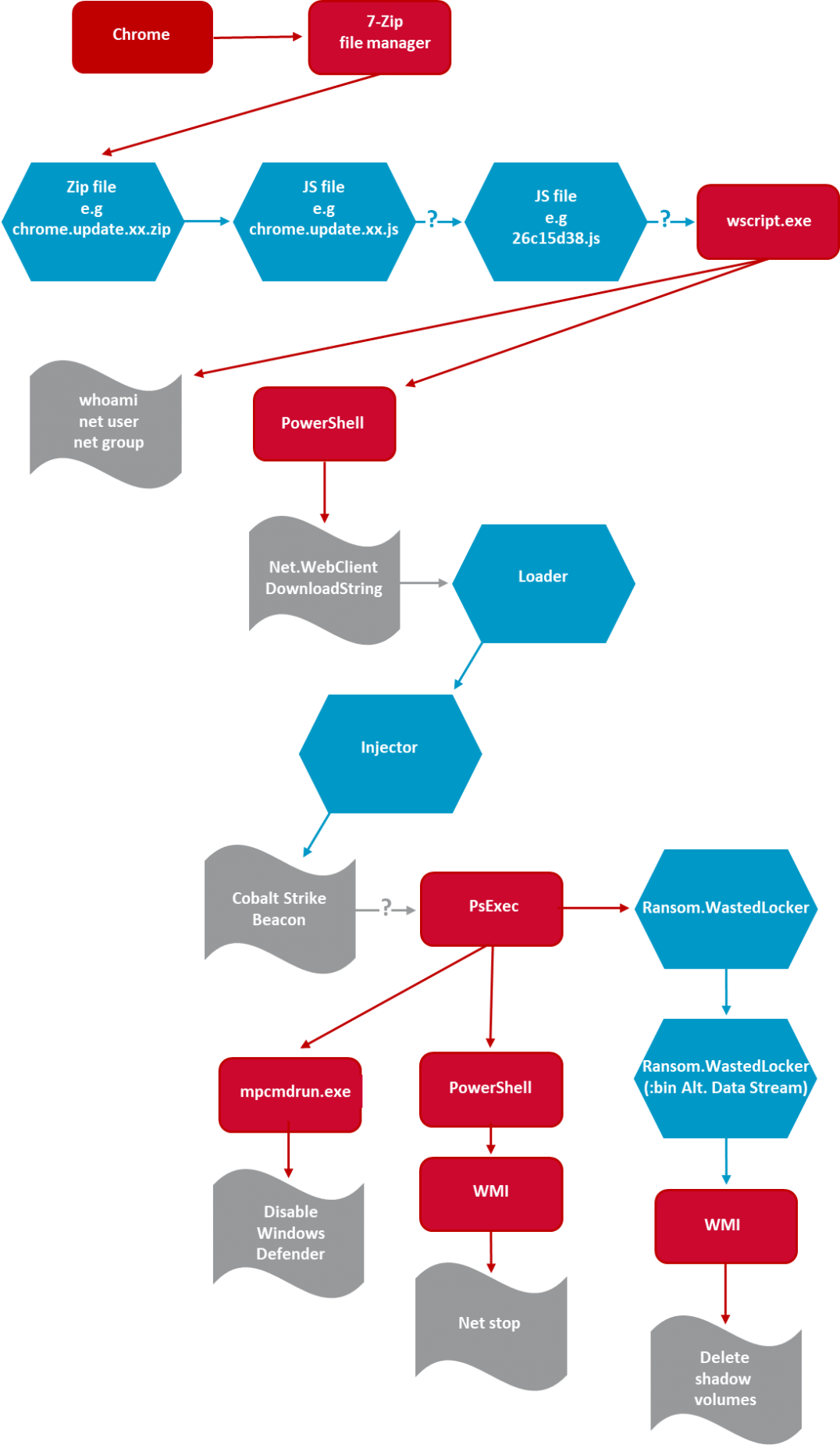
The attacks detected by Symantec began when a compromised website delivered the SocGholish framework via a .ZIP archive. This resource contained malicious JavaScript masquerading as a browser update. After the execution of a second piece of JavaScript, the attack campaign leveraged PowerShell to execute a loader from a domain delivering Cobalt Strike for the purpose of executing commands and injecting other processes.
Ultimately, those behind the malicious campaign used PsExec to disable security functions performed by Windows Defender. They then launched WastedLocker, a threat which got to work encrypting a victim’s data and deleting shadow volume copies.

Symantec didn’t mince its words in summarizing the threat posed by WastedLocker:
The attackers behind this threat appear to be skilled and experienced, capable of penetrating some of the most well protected corporations, stealing credentials, and moving with ease across their networks. As such, WastedLocker is a highly dangerous piece of ransomware. A successful attack could cripple the victim’s network, leading to significant disruption to their operations and a costly clean-up operation.
As such, organizations could focus on defending themselves against ransomware. One of the ways they can do this is working to prevent a ransomware attack in the first place. They can use these tips to get started.
The post ” Attackers Targeted Dozens of U.S. Companies with WastedLocker” appeared first on TripWire
Source:TripWire – David Bisson
