Attack Misuses Google Docs Comments to Spew Out “Massive Wave” of Malicious Links
Security researchers say they have seen a “massive wave” of malicious hackers exploiting the comment feature in Google Docs to spread malicious content into the inboxes of unsuspecting targeted users.
According to a blog post published by Avanan, the comments functionality of Google Docs, as well as its fellow Google Workplace web-based applications Google Sheets and Google Slides, is being exploited to send out malicious links.
The flaw can be exploited by cybercriminals to send messages to just about any email address, and yet the emails are actually sent from Google and so may appear trustworthy.
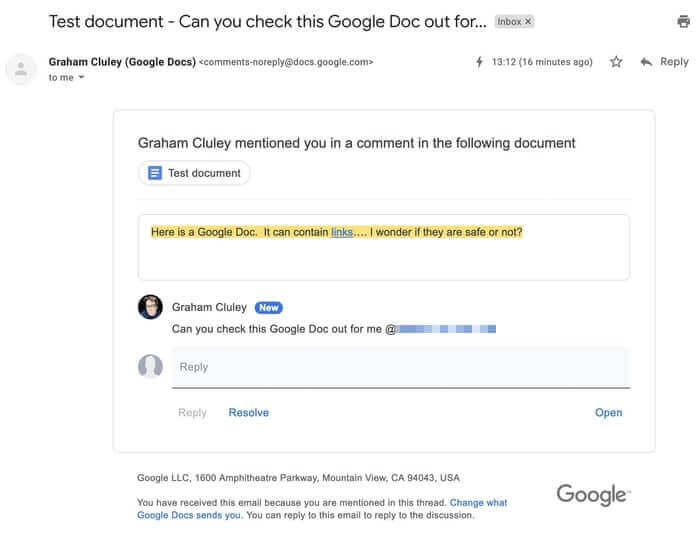
All a fraudster needs to do is create a Google document, spreadsheet, or presentation, and add comments that tag the intended target’s email address. Google sees that as an invitation to “helpfully” inform the user that they have been tagged and send them the document’s content (including any malicious links.)

Use of the technique to spread malicious spam and phishing messages not only makes it more difficult for individuals to determine if an email is dangerous or not, but may also present additional challenges for email-filtering solutions that treat Google as a trusted sender.
Avanan researcher Jeremy Fuchs writes that the latest attack he has seen targeted Outlook users – although not exclusively:
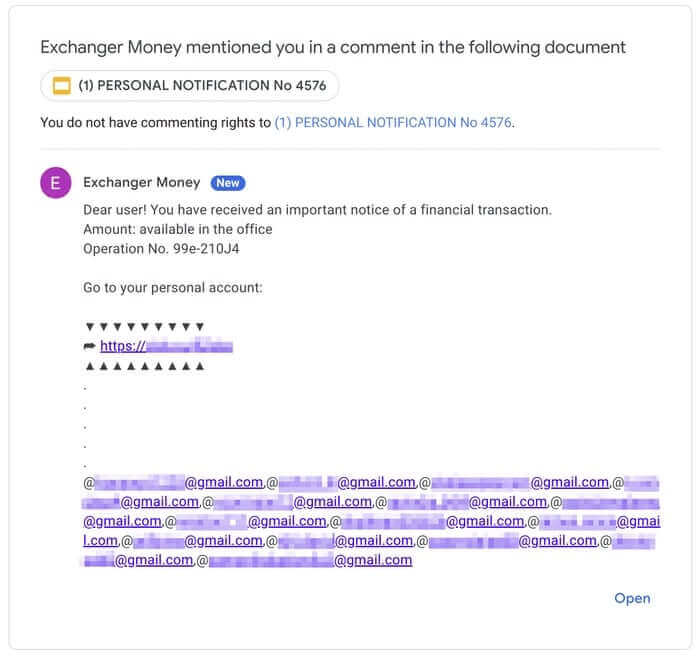
“It hit over 500 inboxes across 30 tenants, with hackers using over 100 different Gmail accounts.”
The problem is compounded by the emails not containing the attacker’s email address, but just their display name.
In other words, a malicious attacker could create a free Google account of “[email protected]”, for instance, and use it to pose as “[email protected]”. If the intended target also worked at “company.com” then they might easily be fooled into thinking it was a genuine notification about a comment left in a Google Doc by one of their colleagues.
The technique could be used to spread links pointing to malware, as well as phishing links that may attempt to steal login credentials from unwary users.
Fuchs claims that Google has not responded to the issue, despite the threat of how Google Docs comments could be exploited to spread spam being publicised in the tech press last October.
Concerned users can protect themselves by being cautious about clicking on suspicious links, and – if still unsure – reach out to the legitimate sender to see if they genuinely tagged them in a Google Doc or other collaboration app.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” Attack Misuses Google Docs Comments to Spew Out “Massive Wave” of Malicious Links” appeared first on TripWire
Source:TripWire – Graham Cluley
