Amazon Web Services Mitigated a 2.3 Tbps DDoS Attack

Amazon Web Services (AWS) said that it mitigated a distributed denial-of-service (DDoS) attack with a volume of 2.3 Tbps.
In its “Threat Landscape Report – Q1 2020,” AWS Shield revealed that its team members had spent several days responding to this particular network volumetric DDoS attack.
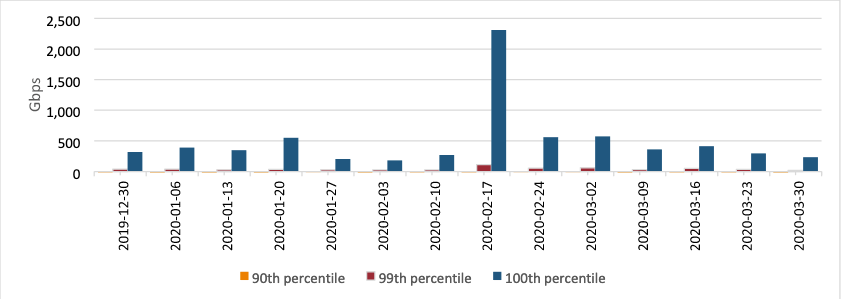
In Q1 2020, a known UDP reflection vector, CLDAP reflection, was observed with a previously unseen volume of 2.3 Tbps. This is approximately 44% larger than any network volumetric event previously detected on AWS. CLDAP reflection attacks of this magnitude caused 3 days of elevated threat during a single week in February 2020 before subsiding.
The AWS report did not disclose the identity of the customer that suffered this attack.
Short for “Connection-less Lightweight Directory Access Protocol,” CLDAP serves an alternative to Microsoft’s Lightweight Directory Access Protocol (LDAP).
Akamai first observed malicious actors abuse CLDAP for conducting amplified DDoS reflection attacks back in October 2016. Those attacks began when a nefarious individual sent a CLDAP request to a LDAP server with a spoofed IP address. The server then added its own data to the response and sent it to the spoofed IP address, or the victim’s IP address. This action subsequently produced a DDoS attack, as machines can’t process too much CLDAP data at once.
Prior to the attack discussed above, NETSCOUT Arbor observed a 1.7 Tbps reflection/amplification DDoS attack against a U.S. service provider in March 2018. News of that attack came just a month after GitHub announced that it had mitigated a volumetric DDoS attack that had peaked at 1.35 Tbps.
These attacks highlight the need for organizations to defend themselves against DDoS attacks. They can begin by creating a distributed denial-of-service mitigation plan and by building it into their incident response plan. For additional tips, click here.
The post ” Amazon Web Services Mitigated a 2.3 Tbps DDoS Attack” appeared first on TripWire
Source:TripWire – David Bisson
