Sloppy patches are a breeding ground for zero-day exploits, says Google
Security researchers at Google have claimed that a quarter of all zero-day software exploits could have been avoided if more effort had been made by vendors when creating patches for vulnerabilities in their software.
In a blog post, Maddie Stone of Google’s Project Zero team says that 25% of the zero-day exploits detected in 2020 are closely related to previously publicly disclosed vulnerabilities, and “potentially could have been avoided if a more thorough investigation and patching effort” were made.
Stone argues that there can often be multiple ways to trigger a vulnerability, or paths to access it – but often vendors will only block the method shown in a proof-of-concept code or exploit sample.
In the case of some zero-day exploits, it was only “only necessary to change a line or two of code”, with minimal differences, to create a new working zero-day exploit.
This is particularly worrying when you consider that many of the zero-day exploits were found in widely-used internet browsers, leaving millions of users at potential risk of attack.
“A correct patch is one that fixes a bug with complete accuracy, meaning the patch no longer allows any exploitation of the vulnerability. A comprehensive patch applies that fix everywhere that it needs to be applied, covering all of the variants,” Stone explained. “We consider a patch to be complete only when it is both correct and comprehensive.”
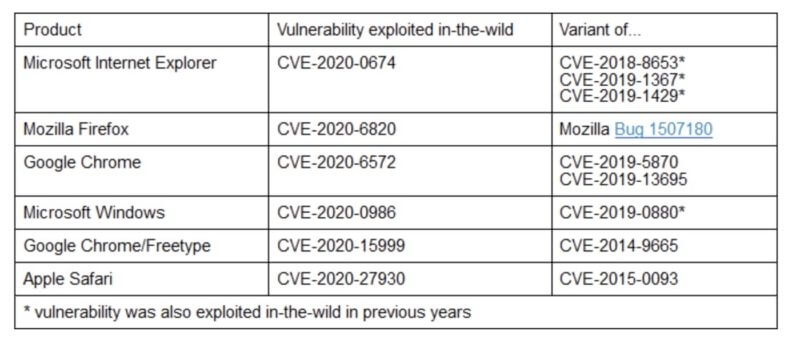
In her blog post, Maddie Stone specifically highlights three vulnerabilities (in Internet Explorer, Google Chrome, and Microsoft Windows) that were exploited in-the-wild, but were not properly fixed after they were reported to each software vendor.

Stone says that Google’s Project Zero team have identified six zero-days that were exploited in-the-wild last year that were closely related to vulnerabilities that had previously been encountered.

If the vulnerabilities had been properly thoroughly patched in the first place then an attacker would have needed to have gone back to the drawing board, and spent time and effort discovering a new method of exploitation. As it was, they were able to build upon the foundations of an existing exploit.
Fixing a security hole isn’t always easy, and fixing it correctly and comprehensively is inevitably going to take more resources, time, and money than an incomplete patch.
But if a vulnerability is properly patched at the first opportunity, then it should lead to everyone remaining more secure going forward and make the lives of malicious hackers harder.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” Sloppy patches are a breeding ground for zero-day exploits, says Google” appeared first on TripWire
Source:TripWire – Graham Cluley
