Egregor Ransomware Attack Hijacks Printers to Spit Out Ransom Notes
So, you’re a ransomware gang and you want to ensure that you have caught the attention of your latest corporate victim.
You could simply drop your ransom note onto the desktop of infected computers, informing the firm that their files have been encrypted.
Too dull?
You could lock infected PCs and display a ghoulish skull on a bright red background (most ransomware seems to insist upon using a shade of red. Maybe the developers have conducted market research as to what Pantone colour is most likely to ensure a swift coughing up of a ransom.)
Too clichéd?
Well, how about the approach taken by the ransomware that hit South American retail giant Cencosud last week?
Cencosud was infected by an Egregor ransomware attack which, in time honoured fashion, stole sensitive files that it found on the compromised network, and encrypted data on Cencosud’s drives to lock workers out of the company’s data.
A text file was left on infected Windows computers, telling the store that private data would be shared with the media if it was not prepared to begin negotiating with the hackers within three days.
That’s nothing unusual, but Egregor’s novel twist is that it can also tell businesses that their computer systems are well and truly breached by sending its ransom note to attached printers.
And in the case of a store like Cencosud, that means that printers at the checkouts of numerous retail outlets in Chile and Argentina were suddenly churning out the ransom demand as well.
As Bleeping Computer reported, one Twitter user managed to capture a ‘possessed’ printer spitting out Egregor’s extortion demand on camera, and upload a short video to Twitter.
Part of the ransom message, which is the same as that left on infected computers, reads:
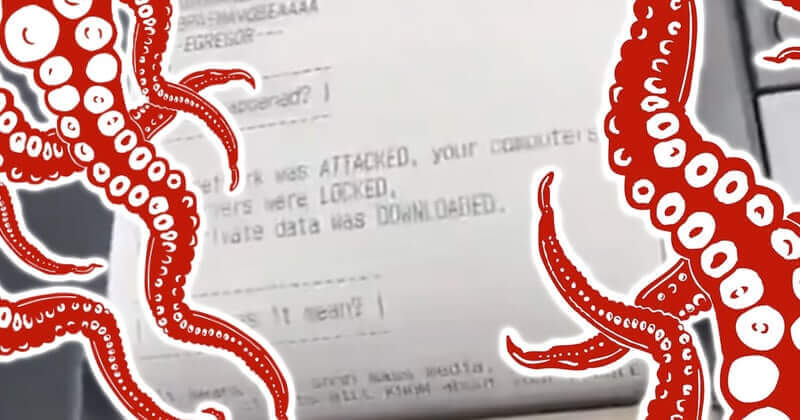
— EGREGOR —
What happened?
Your network was ATTACKED, your computers and servers were LOCKED.
Your private data was DOWNLOADED.What does it mean?
It means that soon mass media, your partners and clients WILL KNOW about your PROBLEM.
How it can be avoided?
In order to avoid this issue, you are to COME IN TOUCH WITH US no later than within 3 DAYS and conclude the data recovery and breach fixing AGREEMENT.
It’s hard to hide the fact that your company has been hit by ransomware if your printers are repeatedly churning out ransom notes in front of customers…
Egregor’s ransomware-as-a-service operations have been in the ascendancy since the retirement of the notorious Maze ransomware gang. It is apparent that Egregor has quickly recognised that the fear of lasting damage to business reputation caused by a data breach and ransomware attack is highly effective at convincing companies to pay up.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” Egregor Ransomware Attack Hijacks Printers to Spit Out Ransom Notes” appeared first on TripWire
Source:TripWire – Graham Cluley
