North Korea’s BeagleBoyz Resumes International Attacks Targeting Banks

North Korea’s BeagleBoyz team resumed its efforts to target banks worldwide with fraudulent money transfers and ATM cash outs.
On August 26, the Cybersecurity and Infrastructure Security Agency (CISA) published Alert (AA20-239A) in coordination with the Department of the Treasury (Treasury), the Federal Bureau of Investigation (FBI) and U.S. Cyber Command (USCYBERCOM).
The four entities used the Alert to analyze BeagleBoyz, a North Korean team which forms a subset of Hidden Cobra activity and which overlaps with Lazarus, among other groups.
This group had attempted to steal $2 billion since 2015 at the time of writing. For much of that time, it had been conducting attacks as part of a sophisticated ATM cash-out campaign called “FASTCash.”
News about FASTCash first emerged in 2018. CISA noted that two things had changed since then, however. First, the group had adopted the ability to target banks that hosted their switch applications on Windows servers. Second, it had expanded its attacks to target interbank payment processors.
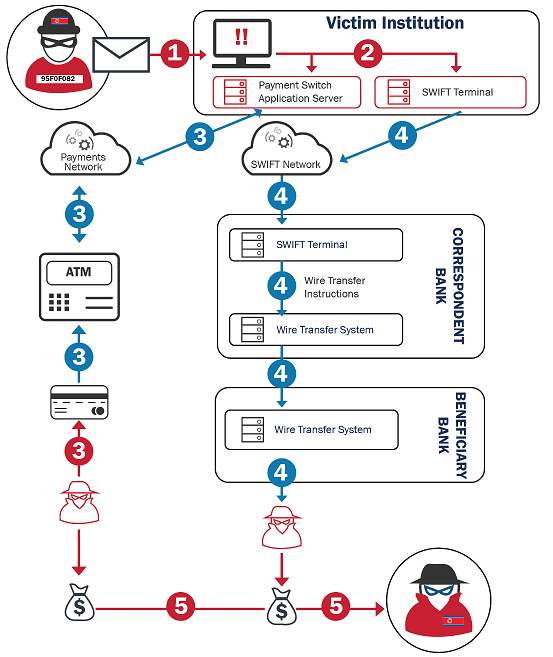
Per CISA, a typical attack from BeagleBoyz began with a spearphishing email or watering hole attack. These efforts enabled the malicious actors to gain initial access to a targeted bank’s network. They then selected which victims to exploit by drawing upon a number of tools including PowerShell scripts and command-line interfaces.
After using the Registry, Task Scheduler and other methods to establish persistence, BeagleBoyz escalated their privileges, all the while using code injection and compromised web services to evade detection.
CISA documented some in instances in which the North Korean attack team had used malware called “ECCENTRICBANDWAGON” to log keystrokes and take screenshots. Even so, it found that BeagleBoyz’s main aim was to find the SWIFT terminal along with the server responsible for hosting the institution’s payment switch application.
Ultimately, BeagleBoyz preyed on these systems by deploying FASTCash. This malware enabled the group to intercept financial request messages and respond with affirmative response messages that looked as if they were legitimate for the purpose of conducting ATM cash outs.
Financial institutions that detect activity associated with BeagleBoyz are urged to contact law enforcement authorities and CISA.
The post ” North Korea’s BeagleBoyz Resumes International Attacks Targeting Banks” appeared first on TripWire
Source:TripWire – David Bisson
