Phishing Campaign Leads Users to Site Disguised as Email Scanner

A phishing campaign tricked users into visiting a website that masqueraded as an email scanner in an effort to steal their account credentials.
Kaspersky Lab found that the campaign began with a scam email containing a fake virus alert.
This email claimed to originate from an organization’s “Email Security Team,” but it actually originated from a Hotmail account.
In an attempt to intimidate the recipient, the email message used a “Virus Alert” heading followed by three exclamation points.
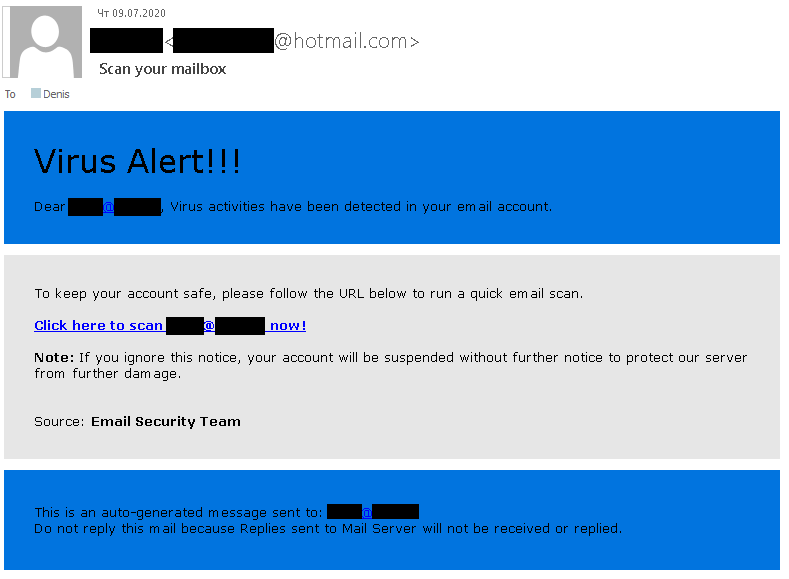
Researchers at the Russian security firm said this design trait was a poor choice on the attackers’ part:
However trifling punctuation may seem, it’s the first thing that should tip off the recipient that something may be wrong. Unnecessary punctuation in a work e-mail is a sign of drama or unprofessionalism. Either way, it’s inappropriate in a notification supposedly intended to convey information about a threat.
But the malicious actors didn’t stop there.
Instead, they built upon this urgency by informing the recipient that they would no longer have access to their email account unless they agreed to scan their email account by clicking on an embedded link.
Clicking on the link led the recipient to a website disguised as an email scanner. This website used the logos of several reputable antivirus providers to convince the user that it was legitimate. It also used the recipient’s email address to personalize the name of their employer in the site’s heading.

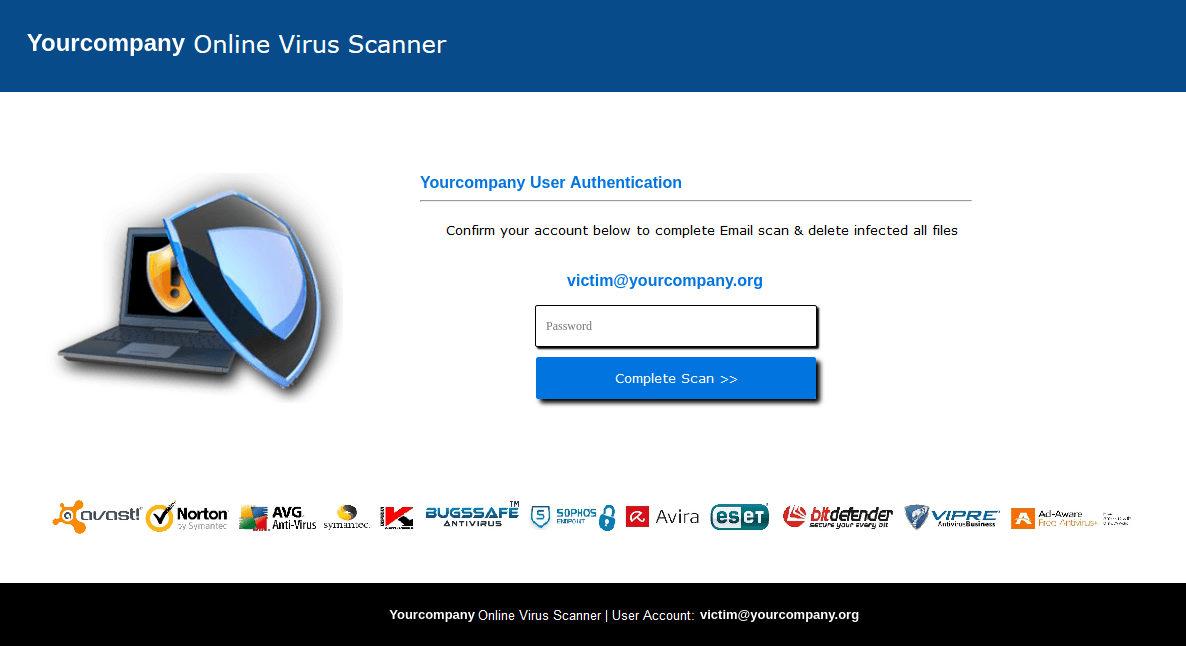
At first, the site simulated a scan, but it interrupted this process with the message “Confirm your account below to complete Email scan & delete infected all files.” It then prompted the user to submit their email account credentials.
This attack highlights the need for organizations to protect themselves against a phishing campaign. They can do this by educating their users about some of the most common types of email-borne campaigns in circulation today.
The post ” Phishing Campaign Leads Users to Site Disguised as Email Scanner” appeared first on TripWire
Source:TripWire – David Bisson
