Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware
Microsoft has warned of fresh campaigns that are capitalizing on the upcoming tax season in the U.S. to harvest credentials and deliver malware.
The email campaigns take advantage of the urgency and time-sensitive nature of emails to send phishing messages masquerading as refund notices, payroll forms, filing reminders, and requests from tax professionals to deceive recipients into opening malicious attachments, scanning QR code, or interacting with suspicious links.
“Many campaigns target individuals for personal and financial data theft, but others specifically target accountants and other professionals who handle sensitive documents, have access to financial data, and are accustomed to receiving tax-related emails during this period,” the Microsoft Threat Intelligence and Microsoft Defender Security Research teams said in a report published last week.
While some of these efforts direct users to sketchy pages designed through Phishing-as-a-service (PhaaS) platforms, others result in the deployment of legitimate remote monitoring and management tools (RMMs), such as ConnectWise ScreenConnect, Datto, and SimpleHelp, enabling the attackers to gain persistent access to compromised devices.
The details of some of the campaigns are below –
- Using Certified Public Accountant (CPA) lures to deliver phishing pages associated with the Energy365 PhaaS kit to capture victims’ email and password. The Energy365 phishing kit is estimated to be sending hundreds of thousands of malicious emails on a daily basis.
- Using QR code and W2 lures to target approximately 100 organizations, mainly in the manufacturing, retail, and healthcare industries located in the U.S., to direct users to phishing pages mimicking the Microsoft 365 sign-in pages and built using the SneakyLog (aka Kratos) PhaaS platform to siphon their credentials and two-factor authentication (2FA) codes.
- Using tax-themed domains for use in phishing campaigns that trick users into clicking on bogus links under the pretext of accessing updated tax forms, only to distribute ScreenConnect.
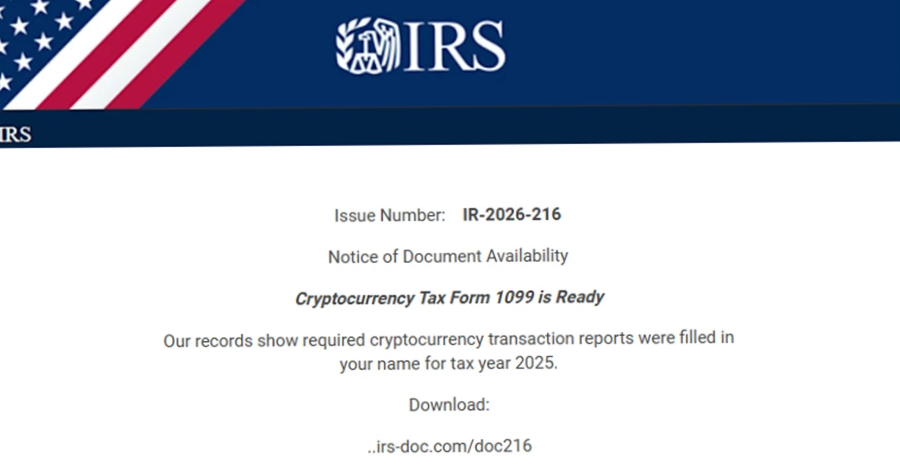
- Impersonating the Internal Revenue Service (IRS) with a cryptocurrency lure that specifically targeted the higher education sector in the U.S., instructing recipients to download a “Cryptocurrency Tax Form 1099” by accessing a malicious domain (“irs-doc[.]com” or “gov-irs216[.]net”) to deliver ScreenConnect or SimpleHelp.
- Targeting accountants and related organizations, asking for help to file their taxes by sending a malicious link that leads to the installation of Datto.
Microsoft said it also observed a large-scale phishing campaign on February 10, 2026, in which more than 29,000 users across 10,000 organizations were affected. About 95% of the targets were located in the U.S., spanning industries like financial services (19%), technology and software (18%), and retail and consumer goods (15%).
“The emails impersonated the IRS, claiming that potentially irregular tax returns had been filed under the recipient’s Electronic Filing Identification Number (EFIN). Recipients were instructed to review these returns by downloading a purportedly legitimate ‘IRS Transcript Viewer,'” the tech giant said.
The emails, which were sent through Amazon Simple Email Service (SES), contained a “Download IRS Transcript View 5.1” button that, when clicked, redirected users to smartvault[.]im, a domain masquerading as SmartVault, a well-known document management and sharing platform.
The phishing site relied on Cloudflare to keep bots and automated scanners at bay, thus ensuring that only human users are served the main payload: a maliciously packaged ScreenConnect that grants the attackers remote access to their systems and facilitates data theft, credential harvesting, and further post‑exploitation activity.
To stay safe against these attacks, organizations are recommended to enforce 2FA on all users, implement conditional access policies, monitor and scan incoming emails and visited websites, and prevent users from accessing the malicious domains.
The development coincides with the discovery of several campaigns that have been found to drop remote access malware or conduct data theft –
- Using fake Google Meet and Zoom pages to lure users into fraudulent video calls that ultimately deliver remote-access software like Teramind, a legitimate employee monitoring platform, by means of a bogus software update.
- Using a fraudulent website that leverages the Avast branding to trick French-speaking users into handing over their full credit card details as part of a refund scam.
- Using a typosquatted website impersonating the official Telegram download portal (“telegrgam[.]com”) to distribute trojanized installers that, in addition to dropping a legitimate Telegram installer, execute a DLL responsible for launching an in-memory payload. The malware then initiates communication with its command-and-control infrastructure to receive instructions, download updated components, and maintain persistent access.
- Abusing Microsoft Azure Monitor alert notifications to deliver callback phishing emails that use invoice and unauthorized-payment lures. “Attackers create malicious Azure Monitor alert rules, embedding scam content in the alert description, including fake billing details and attacker-controlled support phone numbers,” LevelBlue said. “Victims are then added to the Action Group linked to the alert rule, causing Azure to send the phishing message from the legitimate sender address [email protected].”
- Using quotation-themed lures in phishing emails to deliver a JavaScript dropper that connects to an external server to download a PowerShell script, which launches the trusted Microsoft application “Aspnet_compiler.exe” and injects into it an XWorm 7.1 payload via reflective DLL injection. The updated malware comes with a .NET-developed component engineered for stealth and persistence. Similar requests for quotation lures have also been used to trigger a fileless Remcos RAT infection chain.
- Using phishing emails and ClickFix ploys to deliver NetSupport RAT and gain unauthorized system access, exfiltrate data, and deploy additional malware.
- Using Microsoft Application Registration Redirect URI’s (“login.microsoftonline[.]com”) in phishing emails to abuse trust relationships and bypass email spam filters to redirect users to phishing websites that capture victims’ credentials and 2FA codes.
- Abusing legitimate URL rewriting services from Avanan, Barracuda, Bitdefender, Cisco, INKY, Mimecast, Proofpoint, Sophos, and Trend Micro to conceal malicious URLs in phishing emails evades detection. “Threat actors have increasingly adopted multi-vendor chained redirection in their phishing campaigns,” LevelBlue said. “Earlier activity typically relied on a single rewriting service, but newer campaigns stack multiple layers of already‑rewritten links. This nesting makes it significantly harder for security platforms to reconstruct the full redirect path and identify the final malicious destination.”
- Using malicious ZIP files impersonating a wide range of software, including artificial intelligence (AI) image generators, voice-changing tools, stock-market trading utilities, game mods, VPNs, and emulators, to deliver Salat Stealer or MeshAgent, along with a cryptocurrency miner. The campaign has specifically targeted users in the U.S., the U.K., India, Brazil, France, Canada, and Australia.
- Using digital invitation lures sent via phishing emails to divert users to a fake Cloudflare CAPTCHA page that delivers a VBScript, which then runs PowerShell code to fetch an evasive .NET loader dubbed SILENTCONNECT from Google Drive to eventually deliver ScreenConnect.
The findings follow an uptick in RMM adoption by threat actors, with the abuse of such tools surging 277% year-over-year, according to a recent report published by Huntress.
“As these tools are used by legitimate IT departments, they are typically overlooked and considered ‘trusted’ in most corporate environments,” Elastic Security Labs researchers Daniel Stepanic and Salim Bitam said. “Organizations must stay vigilant, auditing their environments for unauthorized RMM usage.”
The post “Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware” appeared first on The Hacker News
Source:The Hacker News – [email protected] (The Hacker News)
