MITRE ATT&CK July 2020 Update: Sub-Techniques!

The highly anticipated structural update to the MITRE ATT&CK framework was released July 8th, 2020. After a quiet first half of the year, it appears the ATT&CK team has been putting in lots of work into some significant redesign of the framework’s structure. This update introduces a new layer of abstraction: sub-techniques.
ATT&CK is a taxonomy of adversarial behavior comprised of tactics and techniques, the what and how of adversarial behavior. Tactics classify objectives attackers look to achieve, i.e. what they are trying to do. Whereas techniques classify specific behavior to achieve those objectives, i.e. how they do it. However, with 266 enterprise techniques and growing, ATT&CK needed a way to better organize and represent the knowledge it contained.
I examined the structural problems within ATT&CK exactly one year ago in this two-part blog post on ontology and ATT&CK (part 1, part 2). There I argued that ad hoc tagging of techniques led to an unevenness of abstraction. Some techniques are very specific and others are very general. Moreover, some techniques are just types of other techniques. So, I concluded that a richer, more principled structure is needed to resolve those problems, and sub-techniques are a natural solution.

Sub-techniques are specific techniques. In some ways, the analogy to the animal kingdom taxonomy is apt, where subspecies refer to specific population groups of a species. For instance, the Bengal tiger, Sunda Island tiger, Trinil tiger are all subspecies of tiger. This kind of taxonomic structure allows for more granularity and relationship modeling between categories.
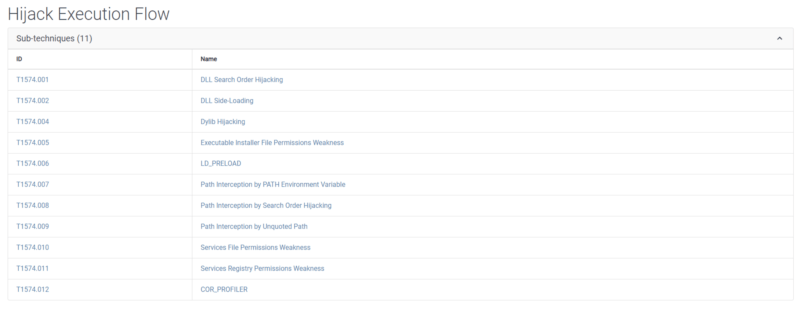
Consider technique T1574, Hijack Execution Flow. Adversaries can execute their own payloads by hijacking the way operating systems run programs. This can be used to achieve persistence, evade defenses, and escalate privileges. However, there is a myriad of ways that attackers can hijack execution flow. This new ATT&CK technique groups up some of the more specific techniques from the old version into a single technique grouping, with 11 sub-techniques.

The new ATT&CK with sub-techniques has 156 techniques and 272 sub-techniques. Techniques from the old ATT&CK have either (1) remained techniques, (2) become sub-techniques, (3) merged with other techniques/sub-techniques, or (4) become deprecated. There are some new techniques and new sub-techniques. It will be a bit painful for most organizations to transition at first, but the useability payoff in the long run will recoup the cost.
MITRE’s official blog post about the update goes into detail about how to ease the transition from the old to the new framework. Previous versions of the ATT&CK framework are still available, however new content will only be added to the sub-techniques version. We look forward to the exciting ways MITRE is developing and evolving the ATT&CK framework.
The post ” MITRE ATT&CK July 2020 Update: Sub-Techniques!” appeared first on TripWire
Source:TripWire – David Lu
