Transportation Systems Sector Cybersecurity Framework Implementation Guide

As smart ticketing systems and technological solutions become more prevalent in the transportation industry, the issue of transportation systems’ cybersecurity becomes a greater concern.
Transportation Systems Cybersecurity is a Major Concern
In August 2019, Transport for London (TfL) was forced to temporarily close down the online facility for its Oyster card system due to a data breach that saw around 1,200 customer accounts compromised. In July 2019, New York City Metropolitan Transport Authority’s (MTA) subway system shut down six major rail lines across the city suddenly and without warning after a widespread server failure attributed to a “software bug.”
While smart ticketing systems are at risk through the same vulnerabilities which affect any online transaction facility, the security of transportation systems themselves is also a pressing issue. Without significant cybersecurity deployment, transportation systems equipped with Internet of Things (IoT) and Artificial Intelligence (AI) capabilities would be vulnerable to outside interference. While leaving users’ data at risk of hacking poses concerns over the threat of fraud and theft, potential hacks of the operating systems of transportation systems could lead to genuine risks to passengers’ safety.
Transportation Systems Cybersecurity Framework
Understanding that a “one size fits all” methodology for implementation of the NIST Cybersecurity Framework is impractical, the Transportation Security Administration, Department of Transportation, United States Coast Guard, and Transportation Systems Sector (TSS) stakeholders created an implementation guide of greatest relevance to the TSS.
The purpose of the TSS Cybersecurity Framework Implementation Guidance is to provide the Transportation Systems Sector with guidance, resource direction, and a directory of options that can assist a TSS organization in its efforts to adopt the NIST Framework. The implementation guidance may be used by organizations to accomplish the following:
- Characterize their current and target cybersecurity posture.
- Identify opportunities for evolving their existing cybersecurity risk management programs.
- Recognize existing sector tools, standards, and guidelines that may support Framework implementation.
- Assess and communicate their risk management approach to both internal and external stakeholders.
This implementation guidance can be incorporated into an organization’s culture regardless of the organization’s current cybersecurity maturity level. For organizations that do not have a formal cybersecurity risk management program, this implementation guidance can help them to comprehend, evaluate, and establish the organizations cyber risk priorities. For those organizations that have a formal risk management office or program in place, this guidance provides additional mechanisms to review existing programs and identify areas for improvement while aligning current efforts to the Framework.
The document guides the Sector’s efforts in managing cyber risks and improving preparedness posture by enhancing cybersecurity awareness and promoting collaborative community action. To achieve its purpose, the Implementation Guide aligns the TSS strategic goals with the NIST Cybersecurity Framework categories. The TSS strategic goals are:
- Goal 1: Define Conceptual Environment
- Goal 2: Improve and Expand Voluntary Participation
- Goal 3: Maintain Continuous Cybersecurity Awareness
- Goal 4: Enhance Intelligence and Security Information Sharing
- Goal 5: Ensure Sustained Coordination and Strategic Implementation
Implementation Guidance
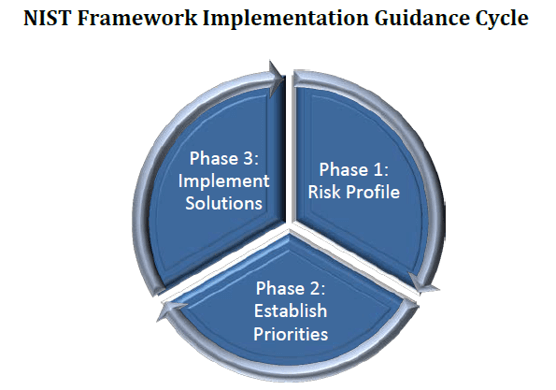
The following diagram illustrates the approach that the TSS is using to assist organizations with their implementation efforts.
Phase 1: Determining Risk Profile
Establishing a cyber-risk profile within an organization is the foundation of the Transportation Systems Sector’s implementation of the NIST Framework. A risk profile attempts to determine the corporation’s willingness to take risk (or its aversion to risk), which drives the overall decision-making strategy. Upon completion, the risk profile furthers an organization’s understanding of its current cyber risk posture and promotes mitigation strategies for improvement.
Phase 2: Establishing Priorities
Upon completion of Phase 1, the organization will be ready to pinpoint where opportunities reside and how to prioritize solutions to reduce its overall risk profile. When developing a strategy to implement solutions, the organization should take resource allocation (both personnel and financial) into account.
Phase 3: Implementing Solutions
The guidance does not provide any recommendations on any solutions or how to implement them, leaving free space for TSS organizations to choose the one that fits their needs. However, there are many publications and standards, such as NIST SP 800-53, NIST SP 800-82 and CIS Controls, that should be reviewed to ensure that the guidance most suitable to reducing the organization’s specific risk profile is selected.
How Tripwire Can Help
Tripwire can help mitigate the increasing cyber risks to the transportation systems sector. Tripwire’s solutions for agencies offering civil services help gain network visibility, continuously monitor your status for potential problems, and increase your resilience. You can learn more by reading this whitepaper.
The post ” Transportation Systems Sector Cybersecurity Framework Implementation Guide” appeared first on TripWire