Sextortionists Using Social Engineering Tactics to Collect Victims’ Data

Security researchers observed sextortionists leveraging social engineering techniques to steal their victims’ personal information.
SANS’ Internet Storm Center (ISC) discovered that sextortionists had begun creating profiles for young women on dating websites. They used those profiles and the stated interest of finding “good times” to connect with new contacts on the platforms.
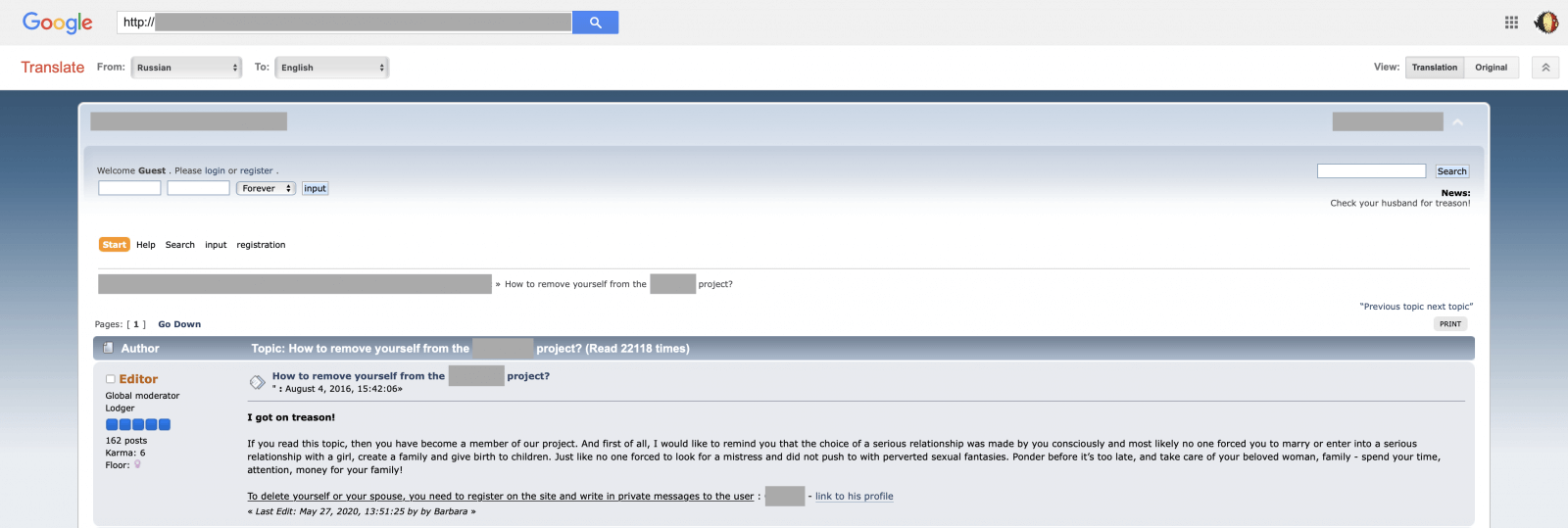
Once they connected with someone on the dating website, they used social engineering techniques to convince their target into disclosing their names, mobile phone numbers, locations, sexual preferences and other information. The sextortionists then posted that data on a publicly available Ukrainian forum.
At the time of discovery, the forum contained a page informing victims that they could become “unlisted” from the website by paying a fee to “help the project.” But the Internet Storm Center found that victims’ information would likely remain on the website regardless. As quoted in a post published by the program:
The forum seems to be online for a while but is still filled with new data. The problem is that, even if the victim pays, the forum is indexed by Google and other search engines (like the very popular yandex.ru). This makes the process to be unlisted very difficult, if not impossible!
This isn’t the first time that sextortionists have abused victims’ personal information. Back in July 2018, for instance, researchers detected a sextortion scam attempt that used breached passwords to trick their victims into thinking that they had suffered a data breach. It was a month later when another variant emerged in which scammers incorporated redacted victims’ phone numbers into their ploys.
The sextortion campaign described above underscores the importance of users not divulging their personal information with contacts on dating websites. Here are some additional tips on how they can keep themselves and their data safe.
The post ” Sextortionists Using Social Engineering Tactics to Collect Victims’ Data” appeared first on TripWire
Source:TripWire – David Bisson
