REvil reborn? Notorious gang’s dark web site redirects to new ransomware operation

Sometimes referred to as Sodinokibi, the notorious REvil ransomware-as-a-service (RAAS) enterprise was responsible for a series of high profile attacks against the likes of the world’s biggest meat supplier JBS Foods and IT service firm Kaseya.
However, it looked like its activities had come to a halt after law enforcement agencies pushed REvil offline in October 2021, and Russia reportedly arrested 14 of the gang’s members earlier this year.
So some will view new activity linked to REvil’s ironically-titled “happy blog”, where it announced its hacks against corporations and leaked data, with understandable disappointment.
As Bleeping Computer reports, researchers have spotted that the TOR address used for REvil’s leak site is now redirecting to a new website, with information about seemingly new attacks.
Amongst those listed as having fallen foul of hackers is Oil India, which last week disclosed it had suffered a security breach which required it to shut down its computer systems.
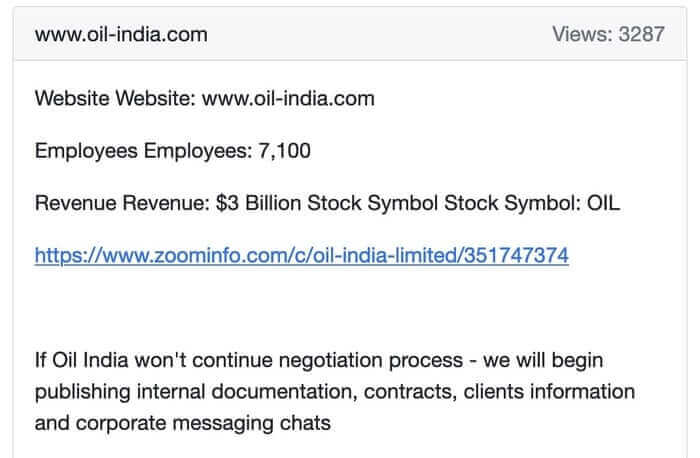
The blog posted by the supposed perpetrators threatens to start publishing exfiltrated data – including contracts, client information, and messaging chats – unless Oil India continues its negotiations.
Most of the other victims listed on the webpage relate to past REvil ransomware attacks.
Meanwhile, a “Join us” page written in Russian explains how criminals can request to become an affiliate, offering benefits such as the “same proven (but improved) software” and an 80/20 split of ransoms collected.

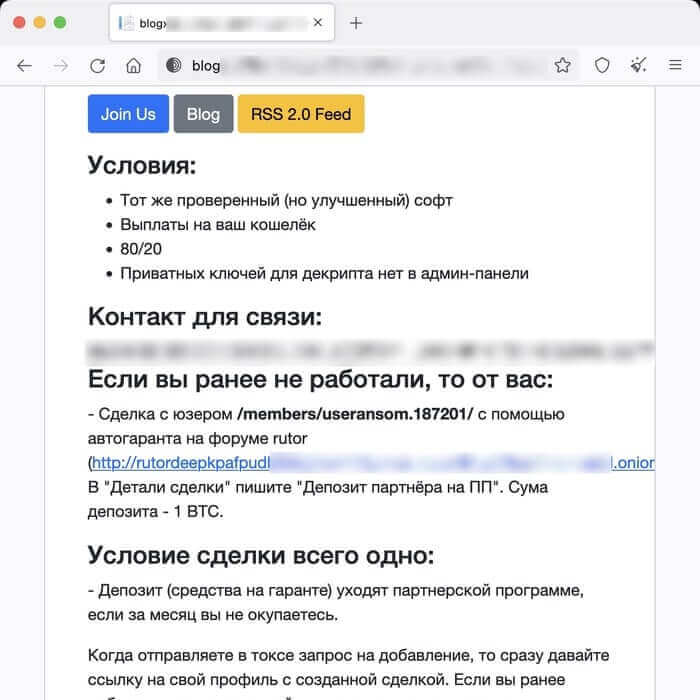
Some may be more wary than normal, of course, of becoming a ransomware affiliate – given evidence uncovered in the past that REvil had no qualms about scamming its fellow cybercriminals.
So, is this latest development evidence that the REvil group is back in operation, or has a new ransomware-as-a-service operation somehow managed to seize control of REvil’s old site and point it to their own pages?
Or is it possible that this the new site is operating as a honeypot, trying to gather information about those interested in becoming ransomware affiliates, collecting intelligence for law enforcement agencies?
For now there are no clear answers, and the pages themselves don’t offer much in the way of clues – failing to make any claims about whose banner they might be operating.
What is definite is that no organisation should rest on its laurels when it comes to defending itself from attack, and take steps now to reduce the chances of being the next victim of a ransomware attack.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” REvil reborn? Notorious gang’s dark web site redirects to new ransomware operation” appeared first on TripWire
Source:TripWire – Graham Cluley
