64 times worse than ransomware? FBI statistics underline the horrific cost of business email compromise

The FBI is reminding organisations of the serious threat posed by business email compromise (BEC) scams, declaring that it caused over $1.8 billion worth of losses to businesses last year.
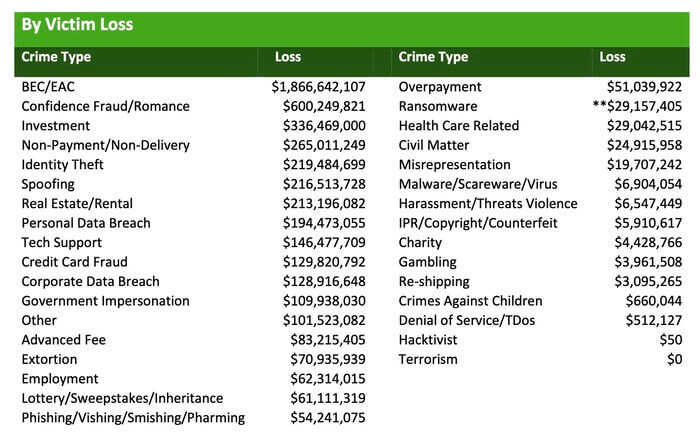
The newly-published annual cybercrime report from the FBI’s Internet Crime Complaint Center (IC3) reveals that it had received a record number of complaints and claims of financial loss – with internet crime causing more than $4 billion in losses.
And although ransomware tends to dominate the cybercrime headlines, the losses attributed to such extortion attempts ($29 million) are dwarfed by business email compromise and email account compromise (EAC).
Indeed, according to the FBI’s released statistics, BEC attacks account for losses that are a massive 64 times worse than ransomware.
Take a minute to look at the numbers, and they’re truly jaw-dropping.
“BEC comprised 37% of all losses last year. That’s an outrageous figure. Given the fact that “spoofing” is likely a subset of BEC, the total loss number is close to $2.1 billion,” says Crane Hassold, senior director of threat research at Agari. “Ransomware, the topic that tends to get the most media coverage, made up only 1% of cybercrime losses.”
Now, it’s important to recognise that even the IC3’s own report appears to be concerned that it might be under-representing the true cost of ransomware.
In a footnote the report indicates that the figure is clearly not reflective of the real cost of ransomware attacks:
“** Regarding ransomware adjusted losses, this number does not include estimates of lost business, time, wages, files, or equipment, or any third-party remediation services acquired by a victim. In some cases, victims do not report any loss amount to the FBI, thereby creating an artificially low overall ransomware loss rate. Lastly, the number only represents what victims report to the FBI via the IC3 and does not account for victim direct reporting to FBI field offices/agents.”
In short, I believe it would be fair to say that ransomware is a bigger problem than the report suggests – but that doesn’t make the threat posed by BEC any less massive.
As the report explains, one of the trends seen in the last year has been criminals stealing identities to open bank accounts. Then organisations struck by a BEC attack are fooled into transferring funds into the accounts, whereupon they are swiftly converted into cryptocurrency – making it significantly harder to trace their eventual destination.
In response to such techniques, the FBI has been running a Recovery Asset Team since 2018 that specialises in freezing accounts used for unauthorised transfers, working closely with financial institutions to recover funds while they can still be tracked.
IC3 recommends that BEC victims contact the originating financial institution as soon as fraud is recognised to request a reversal. In addition, complaints should be filed on the IC3 website.
And, of course, it’s better if the right checks are made before payment is made in the first place – such as verifying that any changes to banking details are verified carefully.
Organisations must put protective measures and policies in place to reduce the chance of being hit by scammers who are using a mixture of social engineering and the compromise of email accounts to trick victims into making unauthorised transfers of funds.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
The post ” 64 times worse than ransomware? FBI statistics underline the horrific cost of business email compromise” appeared first on TripWire
Source:TripWire – Graham Cluley
